
Researchers have discovered two new utilities that are closely associated with the wiper malware used to disrupt the computer networks of Sony Pictures Entertainment last year. After phishing for employees' login information, the attackers responsible for the breach used a strain of wiper malware known as "Destover" to wipe the files off of company workstations, thus rendering them inoperable. Since then, much has been revealed about the breach except for how the attackers were able to remain within the network long enough to exfiltrate terabytes of information, some of which they posted online a month after their initial intrusion. Last week, however, Willis McDonald and Loucif Kharouni, senior threat researchers with advanced threat protection firm Damballa, published a blog post in which they explain two tools that the attackers used to evade detection in Sony's networks. Both utilities had usage statements, and they were called setMFT and afset.
"setMFT is used to copy the timestamp settings from a source file on disk to a destination file, also called timestomping," explain the researchers.
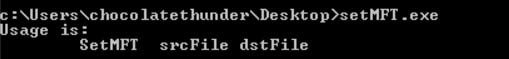
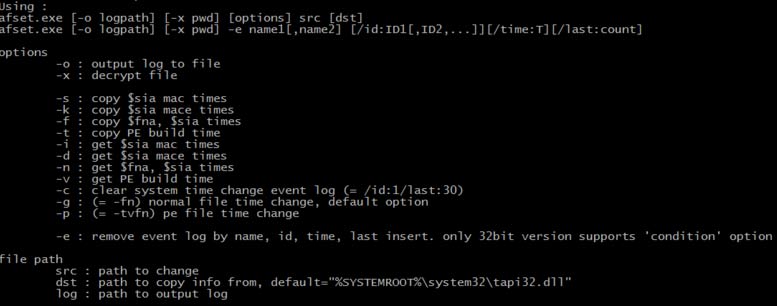
Source: Damballa Timestomping is a technique that when combined with similarly named files allows a file to blend into a directory. A forensic investigation into files' record dates and possibly log files could reveal that a particular file has been timestomped; without such an examination, however, timestomping can easily conceal files from a cursory check for malicious files. McDonald and Kharouni also note that the setMFT tool interacts with the attacker on the command line and is neither delivered nor executed by a dropper without interaction. The other utility, afset, is another timestomping tool that can clean Microsoft Windows logs, as well as alter the PE build time and checksum.
"Afset is used interactively on the target system," the duo observe. "It allows the attacker to remain stealthy and erase their tracks as they move through the network. A full forensic analysis of a system would reveal the presence of afset and missing log activity but it’s likely this activity would go undetected initially creating high-risk infection dwell time."
Source: Damballa Together, setMFT and afset enable a malicious attacker to breach a network, disable defenses, and hide their tracks. Given the fact that only one anti-virus solution successfully detected the tools, attackers employing these utilities could remain undetected for a considerable length of time. A few weeks after the initial intrusion, it was revealed that the North Korean government was responsible for the Sony hack.

