

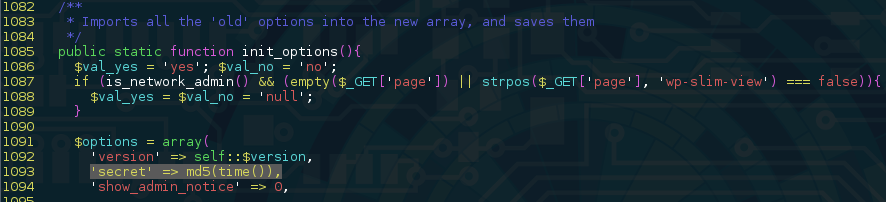
A “very high risk” vulnerability was recently discovered in the analytics plugin WP-Slimstat, potentially impacting more than one million websites operating the WordPress content management system. According to security researchers, the flaw was found to give attackers the capability of performing an SQL Injection attack against the website by breaking the plugin’s weak “secret” key. “This bug can be used by any visitor browsing the vulnerable website,” said Marc-Alexandre Montpas, senior vulnerability researcher at web security firm Suciri, in a blog post published Tuesday. Montpas warned attackers successfully exploiting the bug could grab sensitive information from the target’s database, including username, (hashed) passwords, as well as WordPress Secret Keys, which could result in a complete site takeover. The WP-Slimstat flaw is found in all versions, except for the latest version – 3.6. “WP-Slimstat used a ‘secret’ key to sign data sent to/from the client,” explained Montpas. “By looking at how it was generated, we found it would be possible for an attacker to guess its original value.”
Source: Sucuri Security Advisory
“The ‘secret’ was a hashed version of the plugin’s installation timestamp. An attacker could use sites like Internet Archive to approximately guess what year the site was put online (which would leave us with approx. 30 million values to test, something doable within 10 minutes with most modern CPUs).”
Once the secret key has been attained, an attacker is capable of pulling data from the database. According to the WordPress Plugin Directory, the free tool has been downloaded more than 1.3 million times. As always, users are urged to update their versions as soon as possible.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

