
Phishers are running a scam through a Russian hosting provider that's designed to target Bank of America customers' data. On 21 July, HackRead came across the ploy. Those responsible for the ruse impersonate financial representatives working for the second largest bank in the United States. Under that disguise, the scammers send out emails informing a recipient that they've placed limits on their account and that the recipient must confirm ownership of their account to restore full access.
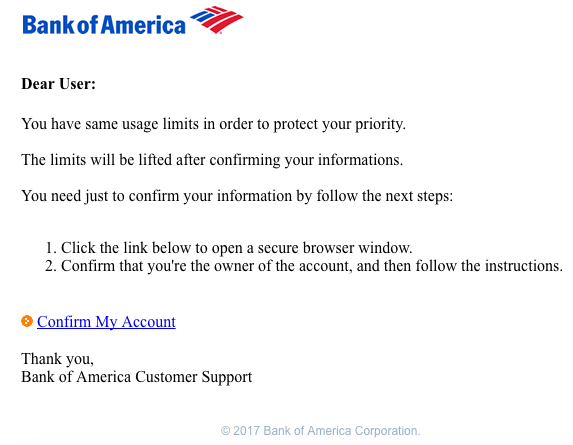
The phishing email targeting Bank of America customers. (Source: HackRead)
"Dear User: You have same usage limits in order to protect your priority. The limits will be lifted after confirming your informations. You need just to confirm your information by follow the next steps: Click the link below to open a secure browser window. Confirm that you’re the owner of the account, and then follow the instructions. [sic]”
Such a grammatical mess helps give away the email's illegitimacy. For those recipients who are undeterred, clicking on "Confirm My Account" redirects them to another page designed to steal their banking credentials. But that's not the end of it. These phishers are particularly greedy. As HackRead security journalist Waqas Amir explains:
"Once signed in, the cyber criminals already have victim’s login credentials, but they want more, therefore, the victim has to fill a form with their personal and financial information and click continue. "The details a victim needs to enter include first and last name, address, city, zip code, mobile number, email address, credit card number, card expiry date and CVV number."
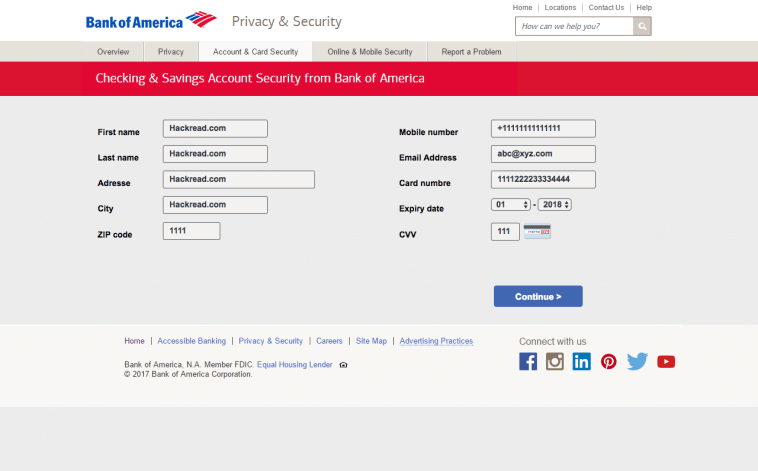
Screenshot of the fake page asking users to enter their personal and banking details. (Source: HackRead) Still not completely satisfied, the scammers then redirect the victim to another page urging them to "[p]lease synchronize [their] BOA account with [their] email to secure every transaction by card." In reality, it's just an effort to steal the victim's email username and password. Scammers can then abuse that email to regain access to the victim's banking account if they ever lose access. They can also potentially use it as a platform off of which they can conduct password reuse attacks against additional web accounts owned by the user. HackRead has traced the scam back to http://sgfreef7[dot]beget[dot]tech, a domain which is serviced by Russian hosting provider Beget. The news outlet has contacted Beget about the ruse. Hopefully, the hosting provider will take down the ploy soon. In the meantime, Bank of America customers can protect themselves by exercising caution around suspicious links and email attachments. They can then take their anti-phishing strategies to the next level by following these tips. Finally, they can turn on two-factor authentication (2FA) for their accounts, a security feature which will help them maintain control of each account for which it is activated even if computer criminals manage to steal their login credentials.
Financial Services Cybersecurity Regulations
Learn how Tripwire's strategies bolster cybersecurity in the financial sector. Facing heightened risks, financial organizations can benefit from Tripwire's expertise in security configuration management and file integrity monitoring, ensuring compliance with critical regulations and safeguarding sensitive data.

