
Security researchers recently uncovered a new type of malware—known as ProxyBack—designed to turn the infected systems of unsuspecting victims into Internet proxies. According to researchers at security firm Palo Alto Networks, the family of malware contains more than 20 versions, and may have been used to infect systems as far back as March 2014. Researchers observed the primary distribution of ProxyBack is focused heavily in Europe, with the majority of targets belonging to educational institutions. “The problem of a non-legitimate proxy is that the network traffic destined to reach the proxy server, which is a compromised system, will usually not be able to reach it because of firewalls or other network-based restrictions put in place to protect systems,” explained Palo Alto Senior Threat Researcher Jeff White in a blog post.
“ProxyBack gets over this hurdle by building a reverse tunnel over TCP to an attacker-controlled proxy server. In other words, it has the victim proxy make the initial call home, thus allowing the proxy server to send its traffic through the tunnel and out to the Internet, or to other devices internal to that network.”
Each infected device operates as a bot inside a larger network controlled by the attackers, who send commands and update instructions via simple HTTP requests.
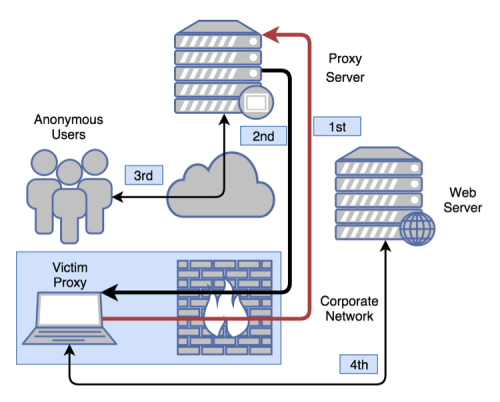
Source: Palo Alto Networks As of last week, the firm reported a head count of more than 11,000 infected computers. The researchers noted that when a system infected with the malware was actively operating, there was a sizable volume of traffic being routed through. “It was clear that there were legitimate, benign users of the [proxy], along with malicious users,” White said, leading to the conclusion that the malware was being leveraged as a proxy service. When analyzing the web traffic routed through their victim proxy, researchers said a particular website stood out: buyproxy.ru – a service claiming to operate between 700 and 3,000 proxy servers per day lasting between 4-24 hours. Buyproxy.ru also claimed to use a “Back End proxy,” which shares an IP for access while distributing the exit. Although it’s yet unclear who is responsible for the distribution of the malware, researchers stressed it’s evident that its designed for, and used in, the [proxy’s] service.

