
Researchers have identified an ongoing campaign that has infected over 200 point-of-sale terminals leveraging ‘PunkeyPOS’ – a malware variant first uncovered in April 2015. According to security experts at PandaLabs, the malware sample has been predominantly targeting US businesses – more specifically, restaurants. In a blog post, researchers explained PunkeyPOS, which originates from an older version of the NewPOSThings malware, is capable of accessing payment systems’ credit card data. “The cyber-criminal’s plan is to install the malware in POS terminals in order to steal sensitive information, such as account numbers, magnetic strip contents (tracks) from bank cards, etc.,” read the blog post. Based on their analysis, the researchers found the malware is comprised of a keylogger (to monitor keystrokes) and a RAM scraper (to read the memory of all processes running on the system). “Regarding the keystrokes, PunkeyPOS ignores all information other than credit card data,” the post said. “It is mostly interested in tracks1/2 from the process memory that is obtained from RAM-scraping.
“The POS terminals read this information from the bank cards’ magnetic strips and then can use this data to clone the cards at a later time.”
Once the credit card data has been gathered, the information is encrypted using an AES algorithm and sent to a remote command and control (C&C) server. Interestingly enough, the researchers also discovered the malware sample’s C&C server address can be easily obtained by reverse engineering the code or analyzing its communication. They came across a web-based control panel with a username and password login.
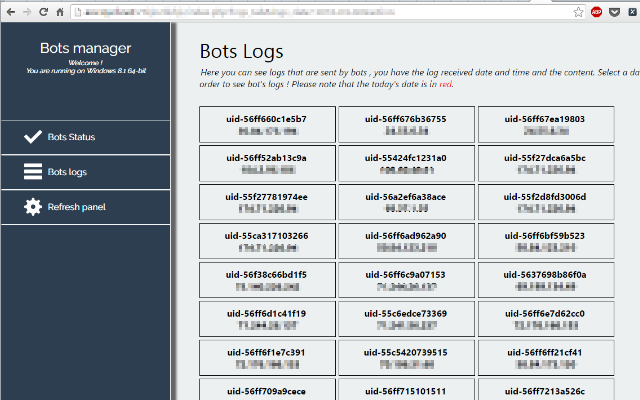
Source: PandaLabs “The cyber-criminals behind this attack haven’t been very careful. Since the server was not configured correctly, PandaLabs was able to access [the control panel] without credentials,” the blog post read. Researchers were able to geolocate around 200 point-of-sale terminals that had been compromised by the malware variant, which is hardcoded with the version number “2016-04-01”.
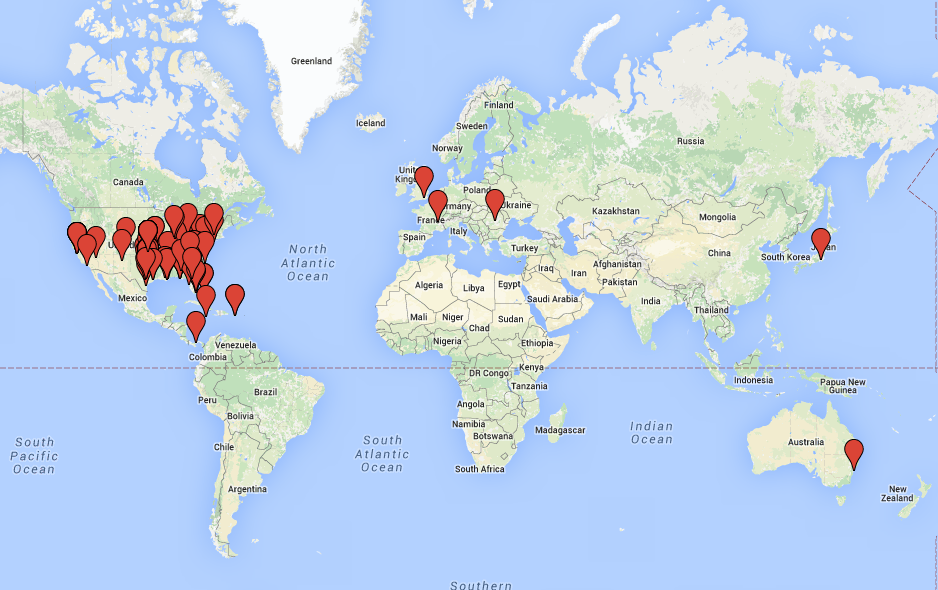
Source: PandaLabs “Taking into account how easy it is to sell this information on the black market, and how convenient it is to compromise these POS terminals anonymously through the internet, we are certain that cyber-criminals will be increasingly drawn to these terminals,” the researchers warned.

