
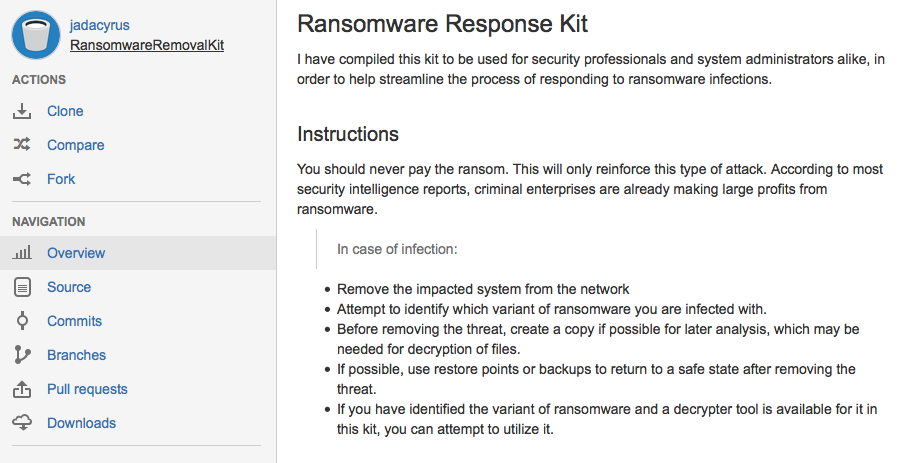
A security researcher has made a ransomware removal kit available online with the hope that it will help security professionals and system administrators alike in responding to instances of ransomware infection. Researcher Jada Cyrus has published the kit on Atlassian Bitbucket. The kit itself consists of removal tools for common ransomware variants, as well as guides on how to perform the necessary removal tasks.
One of the infections that can be removed by the kit is TeslaCrypt, a ransomware variant that uses AES encryption to lock victims’ video game files and demands a ransom payment of 1.5 BTC for the decryption key. The kit also provides removal tools for CryptoLocker, FBIRansomWare, and CoinVault and comes preloaded with ransomware decryptors provided by FireEye and Trend Micro. Cyrus released his kit online under the firm belief that victims should never pay the ransom payments demanded by crypto ransomware.
“You should never pay the ransom. This will only reinforce this type of attack,” explains Cyrus. “According to most security intelligence reports, criminal enterprises are already making large profits from ransomware.”
Instead of paying the ransom, security professionals and system administrators should remove the infected system from a network in order to prevent the infection from spreading. They can then attempt to identify which strain of ransomware has infected their systems, at which point they can determine how best to remove the malware from the infected unit. Cyrus also recommends creating a copy of the ransomware for future analysis, as it may be needed to decrypt affected files. In today’s evolving threat landscape, new variants of ransomware are constantly emerging. One recent example is a new crypto ransomware discovered by Symantec that incorporates elements of the popular television show Breaking Bad into its ransom message and infection processes. To learn more about how you can protect your computer against ransomware, please click .

