
Commercial Virtual Private Network (VPN) services, claiming to provide users enhanced privacy and anonymity, may not be as secure as users think. A group of researchers from Queen Mary University of London and the University of Rome disclosed their findings today, revealing that many of the most widely used VPN services are susceptible to DNS hijacking attacks and leak sensitive IP data. Using a hostile test environment, the students analyzed the infrastructures and tunneling technologies of 14 of the most popular commercial VPN services, including IPVanish, StrongVPN, Astrill and ExpressVPN. The researchers discovered that as many as 10 of the 14 providers studied were vulnerable to leaking IPv6 data. Furthermore, they found that all but one of the VPN services appeared vulnerable to IPv6 DNS hijacking attacks.
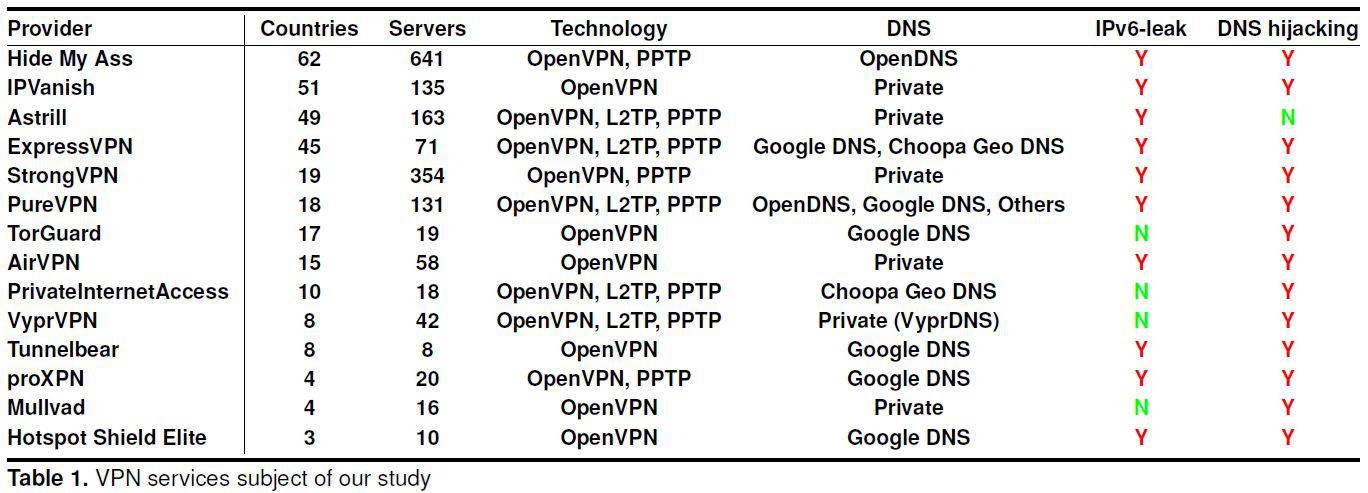
Source: A Glance through the VPN Looking Glass: IPv6 Leakage and DNS Hijacking in Commercial VPN clients “Whereas our work initially started as a general exploration, we soon discovered that a serious vulnerability, IPv6 traffic leakage, is pervasive across nearly all VPN services,” the researchers explained in their paper, A Glance through the VPN Looking Glass: IPv6 Leakage and DNS Hijacking in Commercial VPN clients. “In many cases, we measured the entirety of a client’s IPv6 traffic being leaked over the native interface,” they added. The students said further security screening led them to discover two DNS hijacking attacks, which allowed them to gain access to a victim’s entire traffic.
“The vulnerability is driven by the fact that, whereas all VPN clients manipulate the IPv4 routing table, they tend to ignore the IPv6 routing table. No rules are added to redirect IPv6 traffic into the tunnel. This can result in all IPv6 traffic bypassing the VPN’s virtual interface.”
Although not a serious issue some years ago, the group of researchers noted that an increasing amount of traffic is now IPv6, bringing the problem to criticality. Possible countermeasures for the two vulnerabilities are outlined in the paper but the students state their findings may be part of a wider issue. “Throughout this study, we realised that another worrying aspect of today’s market of VPN services is the large misinformation end users are exposed to, which makes it hard for them to properly tell apart vague and bold claims typical of product advertisement campaigns with actual facts,” they wrote. The students said a more privacy-conscious customer base would likely encourage VPN service providers to take proactive measures towards securing their services and clients against issues like these.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

