
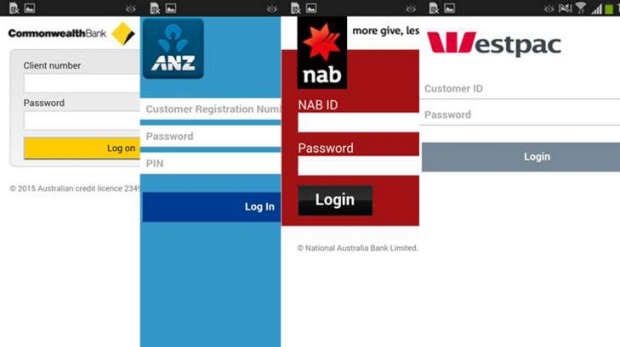
Researchers have discovered a sophisticated strain of Android malware targeting the mobile banking apps of some of Australia’s largest banks. Experts at IT security company ESET said the malware – dubbed Android/Spy.Agent.SI – is not only capable of stealing users’ credentials but also thwarting two-factor authentication. “The malware . . . presents victims with a fake version of the login screen of their banking application and locks the screen until they enter their username and password. Using the stolen credentials, the thieves can then log in to the victim’s account remotely and transfer money out,” said ESET. Researchers noted the criminals behind the malware attacks are also capable of re-routing all SMS text messages received by the infected device and deleting them from the device. ESET Malware Researcher Lukáš Štefanko said this allows SMS-based two-factor authentication of fraudulent transactions to be bypassed, without raising the suspicions of the device’s owner. The Trojan first spreads onto Android devices by imitating the Adobe Flash Player application, often required by websites to play streaming video. After being downloaded and installed, the app requests device admin rights and checks for installed banking applications. Next, it receives fake login screens for each banking app found on the device from its command & control server.
Source: The Sydney Morning Herald “This malware is subject to ongoing development,” ESET said. “While its first versions were simple, and their malicious purpose easily identifiable, the most up-to-date versions feature better obfuscation and encryption." According to reports, the following banks are among the 20 financial institutions currently being targeted, including several banks based in New Zealand and Turkey:
- Commonwealth Bank
- ANZ Bank
- National Australia Bank
- Westpac
- Bendigo Bank
- George Bank
- Bankwest
- ME Bank
- ASB Bank
- Bank of New Zealand
- Kiwibank
- Wells Fargo
- Halkbank
- Yapı Kredi Bank
- VakıfBank
- Garanti Bank
- Akbank
- Finansbank
- Türkiye İş Bankası
- Ziraat Bankası
"This is a significant attack on the banking sector in Australia and New Zealand, and shouldn’t be taken lightly,” says Nick FitzGerald, Senior Research Fellow at ESET.
“While 20 banking apps have been targeted so far, there’s a high possibility the e-criminals involved will further develop this malware to attack more banking apps in the future,” he warned.
FitzGerald noted mobile malware is becoming more common and complex. Hence, smartphone and tablet users should be aware of the ramifications of entering personal information into potentially fake login screens.

