
A new ransomware family called Spora comes outfitted with a sophisticated encryption scheme and a professionally designed payment portal. Spora, which is Russian for the word "spore," relies on fake invoice emails for distribution. The emails bear ZIP files containing HTML Application (HTA) files as attachments. But users might not realize it. That's because the HTA files use double extensions like PDF.HTA and DOC.HTA, which means they might only see the first extension. Clicking on any of the HTA files launches Spora. It's then that the ransomware begins to have some fun. Catalin Cimpanu of Bleeping Computer explains:
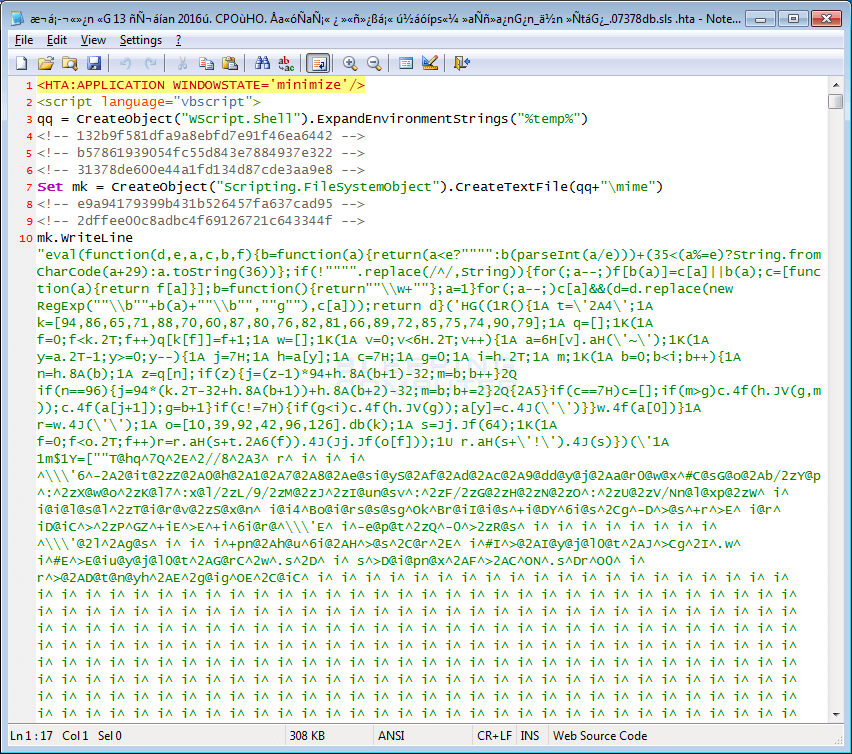
"When a user runs the HTA file, it will extract a Javascript file named close.js to the %Temp% folder, which further extracts an executable to the same folder and executes it. This executable uses a randomly generated name. On our test run it was '81063163ded.exe.' This executable is the main encryptor and will begin to encrypt the files on the computer."
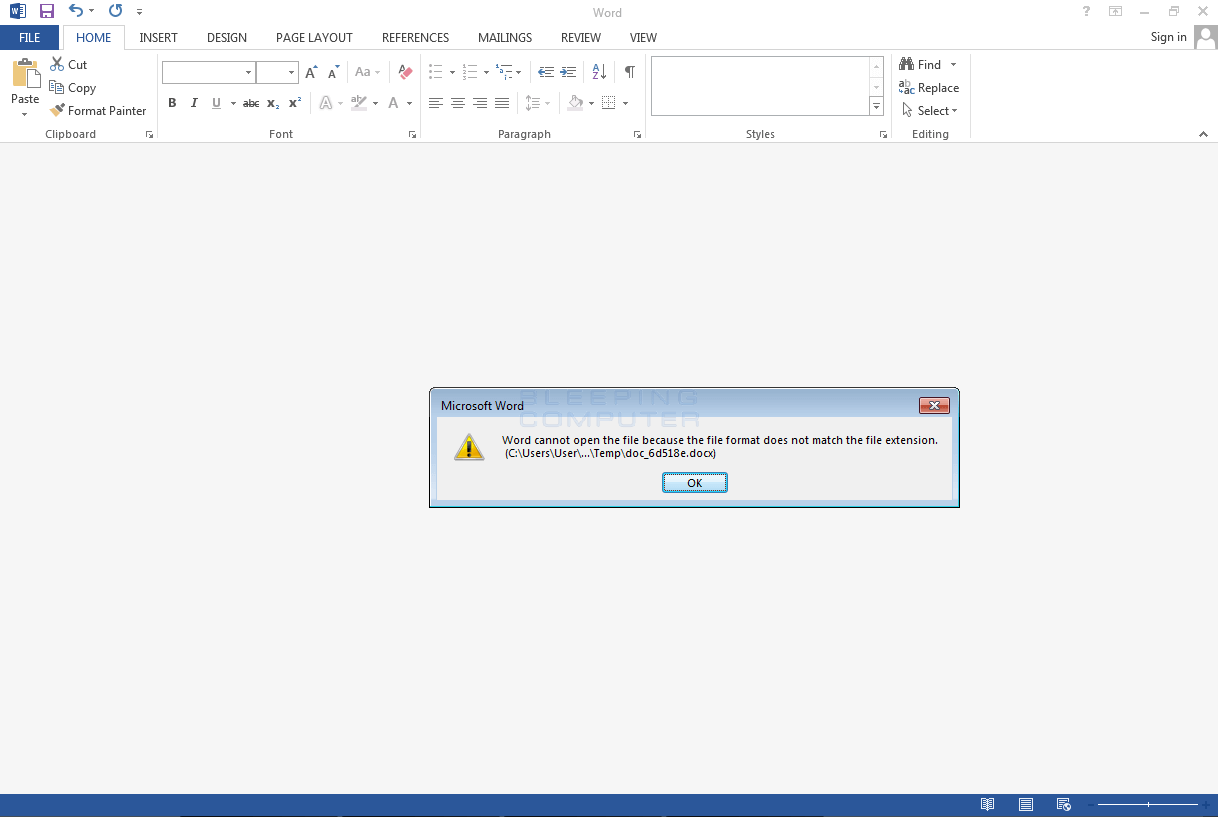
Source: Bleeping COmputer The ransomware's encryption routine is more than sophisticated than that of most other crypto-malware samples. In addition to creating an encryption key, Spora creates a .KEY file using an RSA key, an AES key, and a public key embedded in the executable. That .KEY file is essential to victims who wish to decrypt their files using the computer criminals' services. While Spora encrypts files with one of 22 different file extensions on both the local computer and network shares, it extracts and executes a DOCX file that leads the user to believe something went wrong when they attempted to open the email attachment.
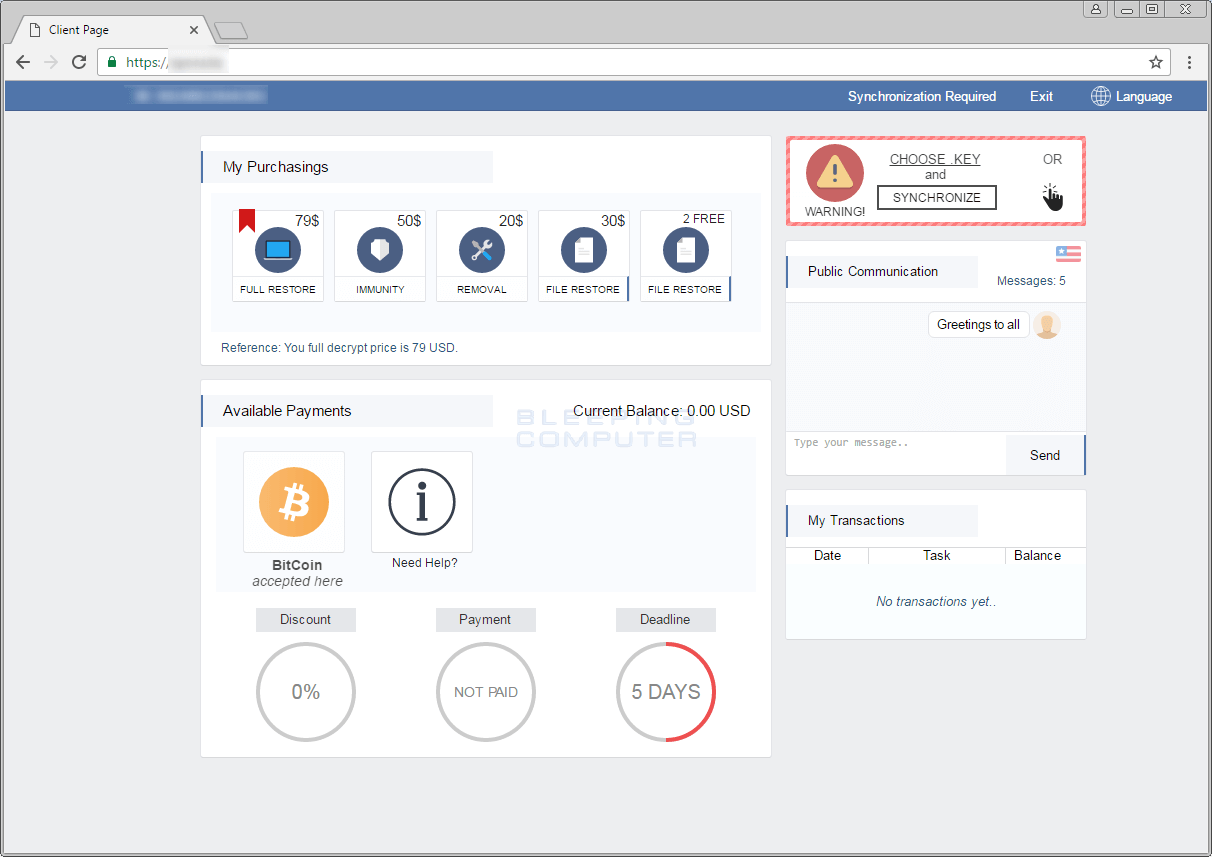
Source: Bleeping Computer The ransomware will then add a ransom note containing a unique infection identifier and the .KEY file to the user's desktop. If a user to decides to decrypt their files with the computer criminals, they'll need to first enter their infection identifier into a login page for a hidden TOR site. Assuming they successfully enter their ID, the victim will then need to upload their .KEY file to synchronize their computer's infection with the payment site. The criminals' service needs that information to create a dashboard that the victim can use to restore some or all of their files, purchase immunity to future Spora infections, remove the ransomware from their computer, and more. They can even use the website to ask Spora's authors up to five questions.
Source: Bleeping Computer As of this writing, Spora is targeting only Russian users. But that could change in the near future. With that said, users should protect themselves by avoiding suspicious links and email attachments, maintaining an up-to-date antivirus solution on their computers, updating their systems regularly, and following some additional ransomware prevention technologies. They should also make sure they back up their data regularly just in case they experience an infection.

