
A new variant of the SpyNote remote access trojan (RAT) is infecting Android devices by masquerading as a mobile Netflix app. The malware, which is based off the SpyNote RAT builder leaked in 2016, displays the same icon used by the official Netflix app that's found on Google Play. But it's a fake. Clicking on the app causes the icon to disappear from the device's home screen.
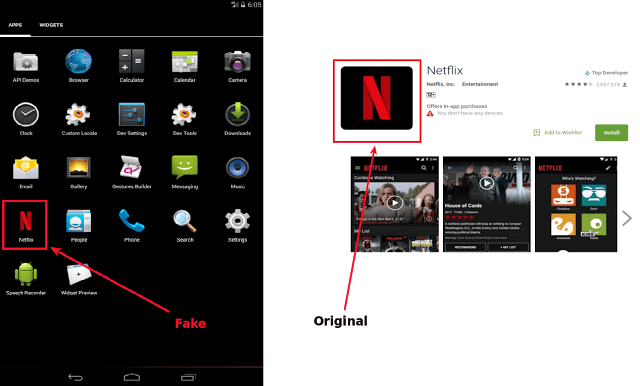
Fake Netflix vs. legitimate Netflix. (Source: Zscaler) It's the perfect ruse. The user believes the app has somehow uninstalled from their device. In the meantime, SpyNote RAT gets to work in the background. First, it establishes communication with its command and control (C&C) server and achieves a degree of persistence on the infected device. Zscaler's ThreatLabZ research team explains in a blog post:
"The SpyNote RAT registers a service called AutoStartup and a broadcast receiver named BootComplete. MainActivity registers BootComplete with a boot event, so that whenever the device is booted, BootComplete gets triggered. BootComplete starts the AutoStartup service and the AutoStartup service makes sure that MainActivity is always running."
With that level of access guaranteed, the malware can get to work executing any of its main functions. For instance, it can leverage command execution to root the device using known vulnerabilities or zero-days, capture screen shots and audio recordings, and intercept SMS messages. It can even steals contacts so that it can infect other Android users.
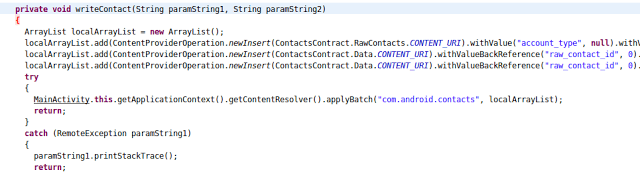
Stealing and writing contacts. (Source: Zscaler) Further investigation revealed that SpyNote, which isn't the only spyware targeting Android devices, poses as a variety of legitimate services like Facebook, WhatsApp, and PokémonGo. ThreatLabZ feels this malware owes its explosion to its widely available RAT builder:
"The days when one needed in-depth coding knowledge to develop malware are long gone. Nowadays, script kiddies can build a piece of malware that can create real havoc. Moreover, there are many toolkits like the SpyNote Trojan builder that enable users to build malware with ease and few clicks."
Given the prevalence of SpyNote and others like it, Android users should install applications only from the Google Play Store. They should also avoid installing any mobile app that's not yet officially available for Android, as unofficial copies could be malicious in nature.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

