
Researchers have released a decryption utility that victims of TeleCrypt ransomware can use to restore access to their files. The Delphi-written trojan first reared its ugly head in the beginning of November 2016. Most crypto-ransomware samples communicate with their command-and-control (C&C) servers over HTTP-based protocols to send information about a victim to the attackers. Attackers then use those same channels to provide the ransomware with an encryption key with which it can deny a user access to their information. But TeleCrypt does something different. It uses the public API of Telegram, a messaging app which experienced a sustained distributed denial-of-service (DDoS) attack back in 2015, to communicate with its developers. Anton Ivanov and Fedor Sinitsyn of Kaspersky Lab explain how the ransomware works its dark magic against primarily Russian users:
"The cybercriminals first create a 'Telegram bot'. A unique token from the Telegram servers identifies the newly-created bot and is placed into the Trojan’s body so it can use the Telegram API. "The Trojan then sends a request to the URL https://api.telegram.org/bot<token>/GetMe, where <token> the unique ID of the Telegram bot, created by the cybercriminals, is stored. According to the official API documentation, the method ‘getMe’ helps to check if a bot with the specified token exists and finds out basic information about it. The Trojan does not use the information about the bot that the server returns."
To encrypt a user's files, TeleCrypt generates a random string that's between 10-20 length and that contains only the letters vo, pr, bm, xu, zt, and dq. It then encrypts each file by looping through them one byte at a time and adding a byte from the key in order before finally displaying its ransom message.
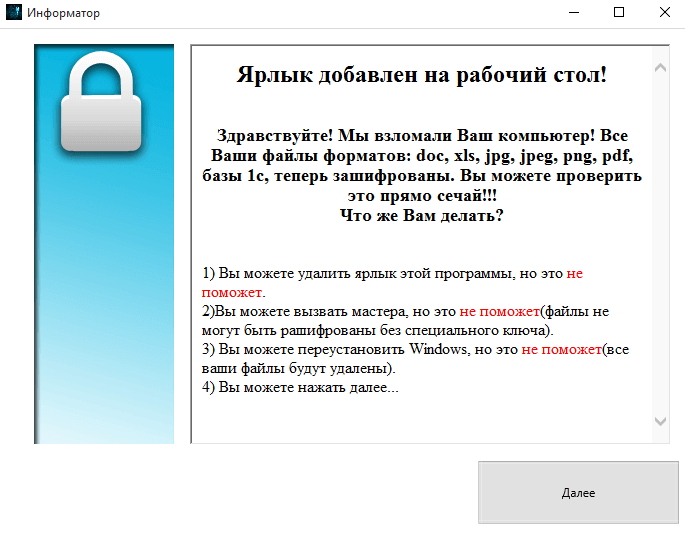
TeleCrypt ransom note (Source: Malwarebytes) But in its simple encryption method rests the ransomware's undoing. Researchers at Malwarebytes Labs elaborate on that point:
"Fortunately, the encryption used was not strong and one of our employees, Nathan Scott, already prepared a decryption tool, allowing the victims to recover their files without paying."
To use Malwarebytes' decryptor, all users need is a non-encrypted copy of an encrypted file so that the application can generate a key. Users can then use that key to restore access to their files for free.
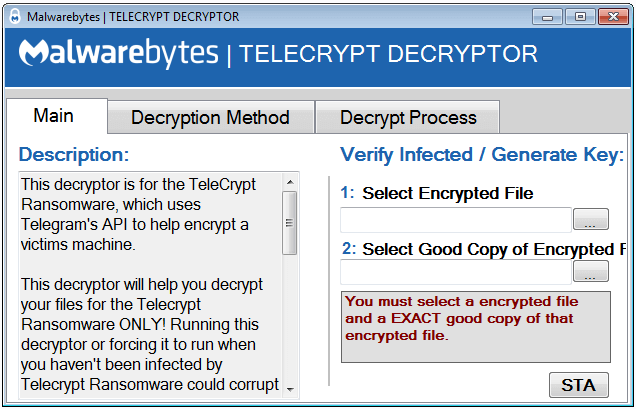
TeleCrypt Decryptor (Source: Malwarebytes) It's fantastic when security researchers find a way to decrypt ransomware victims' files for free. But that doesn't always happen, and even if it does, it could take weeks if not months of looking for researchers to find a suitable coding error in the ransomware. With that in mind, it's up to users to create a data backup strategy and to implement additional ransomware prevention tips before they suffer an infection. For more information about ransomware in general, please click here.

