
The newest variant of Locky ransomware has begun to add yet another file extension to the files it encrypts, and it is the .thor file extension. The virus drops a _WHAT_is.html and the same named .bmp type of file after an infection has been caused. The ransomware also creates several other files, such as a malicious .dll file that causes the encryption. For Locky to encrypt files, the virus relies entirely on the RSA and AES encryption algorithms combined in its distinctive encryption mechanism. If your computer was infected with the latest Locky threat appending the .thor file extension, be sure to read this article to learn more information about this particular variant of one of the nastiest malware threats out there.
Detailed Information about Locky’s .thor Ransomware Variant
Having different file extensions is nothing new for Locky ransomware. In fact, the virus has used different file extensions for different spam campaigns that helped spread it. Here are the file extensions associated with Locky ransomware so far:
- .locky
- .bart
- .zepto
- .perl
- .odin
And what is even more curious about the virus is that most campaigns being spammed were detected at relevantly the same time, pointing to attack campaigns by Locky to be organized.
The .thor Locky Variant’s Infection Process
To better explain how the Locky ransomware causes damage to your computer, we will go over the threat methodically. To cause a successful infection of the .thor variant of Locky, the cyber-criminals have undertaken massive spam campaigns to spread the malware. The spam campaigns spread two types of malicious files:
- .wsf malicious JavaScript type of files
- .hta types of files.
The files may be archived in a .zip archive that has the name of the files, which looks similar to “Receipt_12847182_12481”. After this has been done and the malicious file is opened, it connects to a malicious website to download the malicious payload. As soon as the payload is downloaded, Locky begins encrypting files on the stop. The .thor Locky variant is pre-programmed to hunt for a massive list of file extensions which, if it detects, the virus will immediately begin appending AES-128 encryption on the files in combination with RSA-2048 cipher for the decryption keys. Due to the many file extensions present, we have summarized the important files Locky encrypts down to audio and image files, as well as files connected to commonly used programs like Adobe Reader and Microsoft Office documents. After the encryption process performed by Locky .thor ransomware has been completed, unique decryption keys are generated and sent possibly via UDP, HTTP or TCP connection to the command and control (C2) servers of the virus, which according to researchers are located at the following addresses:
- 102.13677:80/linuxsucks.php
- 200.14124:80/linuxsucks.php
- 234.35215:80/linuxsucks.php
- bwcfinntwork:80/linuxsucks.php
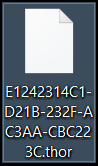
As part of the encryption process, each encrypted file's name is changed, like the example on the right. The .thor ransomware virus also drops two more files – .html and .bmp – after infection that aim to notify the infected users what has happened to their files. Those files are designed to motivate victims to pay a hefty ransom fee in Bitcoin. The .html file is usually opened with the web browser, and it has the following message to users:
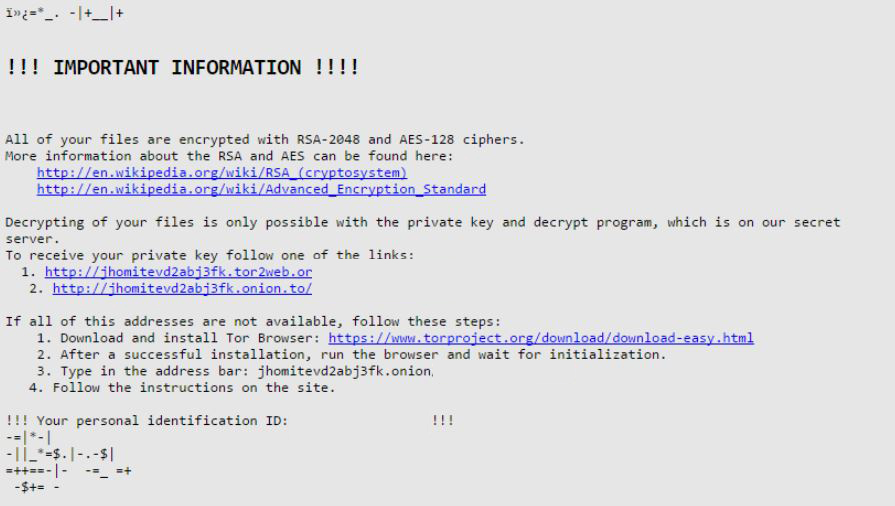
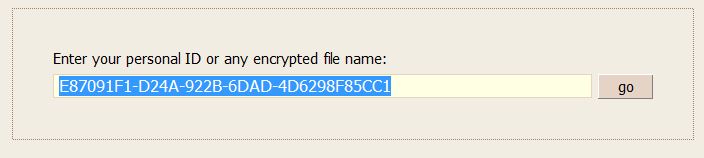
At the moment, the virus demands 0.52 BTC for ransom payoff. Users can see that by clicking on the payment page and typing in their unique ID number or name of one of the encrypted files:
The sad part is that users are left with nothing but to pay the ransom because, at this point, there is no current decryptor available either for the .thor Locky virus or other variants of the notorious threat.
Locky .thor Ransomware – What If I am Infected?
In case you have been a victim of this virus, there are several things you can do. One of those is to pay the ransom of approximately 0.5 BTC, which may or may not get your files back. However, this is a large amount, and you have no guarantee that the files will be deciphered with the decryptor provided by the cyber-criminals. Instead of paying the ransom, malware researchers strongly advise users who have been infected by this variant of Locky ransomware to focus on removing the malicious files yourself and attempting alternative methods to restore your files. You can hunt for the .dll file created by Locky’s .thor variant manually. You can also remove the virus and all of its associated objects automatically with an anti-malware software, which may also detect other malware or unwanted software.
How to Restore Files Encrypted by Locky Ransomware
There are several alternatives to trying to restore your files while waiting for decryptor to be released. But bear in mind that you should backup the encrypted files before attempting any of them and also keep in mind that they are not guaranteed to succeed every time. Here are some alternative solutions:
- Try scanning the sectors of your hard drive to assemble files using data recovery programs.
- Try using network sniffers to capture different packets in an effort to intercept the private RSA decryption key.
- Try using Python to attempt and factorize public keys to establish private keys in an effort to develop a decryptor.
Since Locky is out on the web in many forms, users are strongly advised to be careful when opening online emails and to create more than one backup of their important files on another device. Interested in learning more about Ransomware? Click here.

About the Author: Vencislav Krustev has a degree in Marketing and Value Chain Management and is currently accomplishing the Cisco CCNA engineering course for network and system administrators. He is passionate about cyber-security and malware research, which is why he dedicated a great deal of his time to gain experience in the cyber-security field. You can find him at SensorsTechForum.com – a blog and a forum on cyber security and threats – where he is researching solutions against malware infections from morning till dusk. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Save
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

