
Uber credentials of thousands of users were spotted for sale on an underground marketplace for as low as $1 per stolen username and password. According to a report by Ars Technica, the logins are being offered by two separate vendors on AlphaBay – an online black market operating on the Tor network.
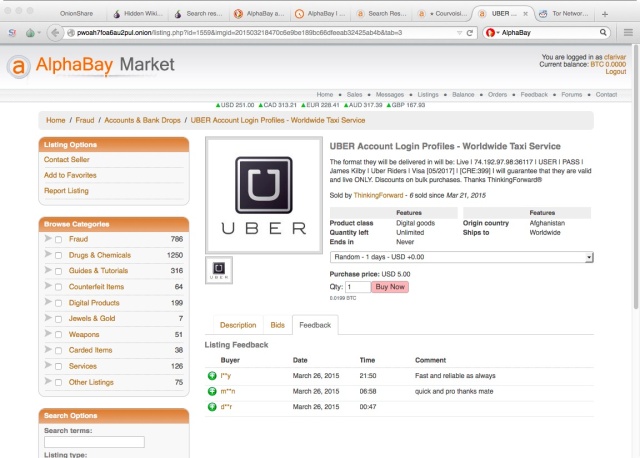
Source: Ars Technica One seller reported more than 100 Uber accounts had already been purchased, letting buyers order free rides with the account’s payment information on file, as well as access to the user’s trip history, email address, phone number and other location information. In a statement, Uber has responded to the issue by claiming it has “found no evidence of a breach.”
“Attempting to fraudulently access or sell accounts is illegal and we notified the authorities about this report.”
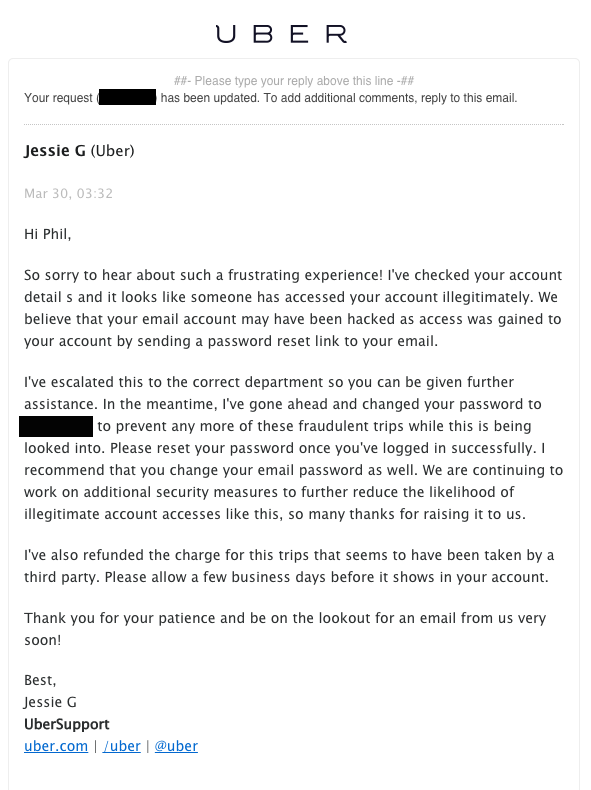
An email to an affected customer from Uber reads: “We believe that your email account may have been hacked as access was gained to your account by sending a password reset link to your email.” The user’s password is changed – and included in plain text – but as the UberSupport representative says:
“We are continuing to work on additional security measures to further reduce the likelihood of illegitimate account access like this…”
The transportation company also added the instance was a good opportunity to remind people to use strong and unique usernames and passwords, and to avoid reusing the same credentials across multiple sites and services. “The amount of data available on underground forums and markets is reaching horrifying levels, simply because there are data sets that nobody knows where they came from,” said Tripwire Senior Security Analyst Ken Westin.
“In many respects, this trend reveals the number of breaches that are occurring that go unreported or undetected, and not just with service providers themselves but also when data sets are shared with business partners, or when the data is compromised between device and server.”
Westin said the evident value in this data is likely making cyber criminals and syndicates work around the clock to identify weaknesses in email, social media, loyalty programs and other sources. “Many times these logins and passwords are shared across multiple systems – hackers are well aware of this and will test what other systems they can access with a compromised data set,” he added. Westin suggests this may be the case with Uber, where the data may have been compromised from another data set. As long as the logins are shared, fraudsters are able to access a higher value target using the same credentials.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

