
TrickBot malware is using a Windows Task named "service update" in an attempt to evade detection and maintain persistence on infected endpoints. The refinement is part of a new wave of phishing emails that distribute the botnet trojan, a threat which shares many characteristics with Dyre. These emails all come with PDF documents containing an embedded Word document. Other malware families like Jaff ransomware and Dridex have leveraged this technique in response to users' growing awareness of malspam campaigns pushing out Microsoft Office documents with malicious macros. While it does also push out Word attachments with macro scripting, TrickBot's newest campaign seeks to trick recipients with a distribution method about which many users are still unaware.
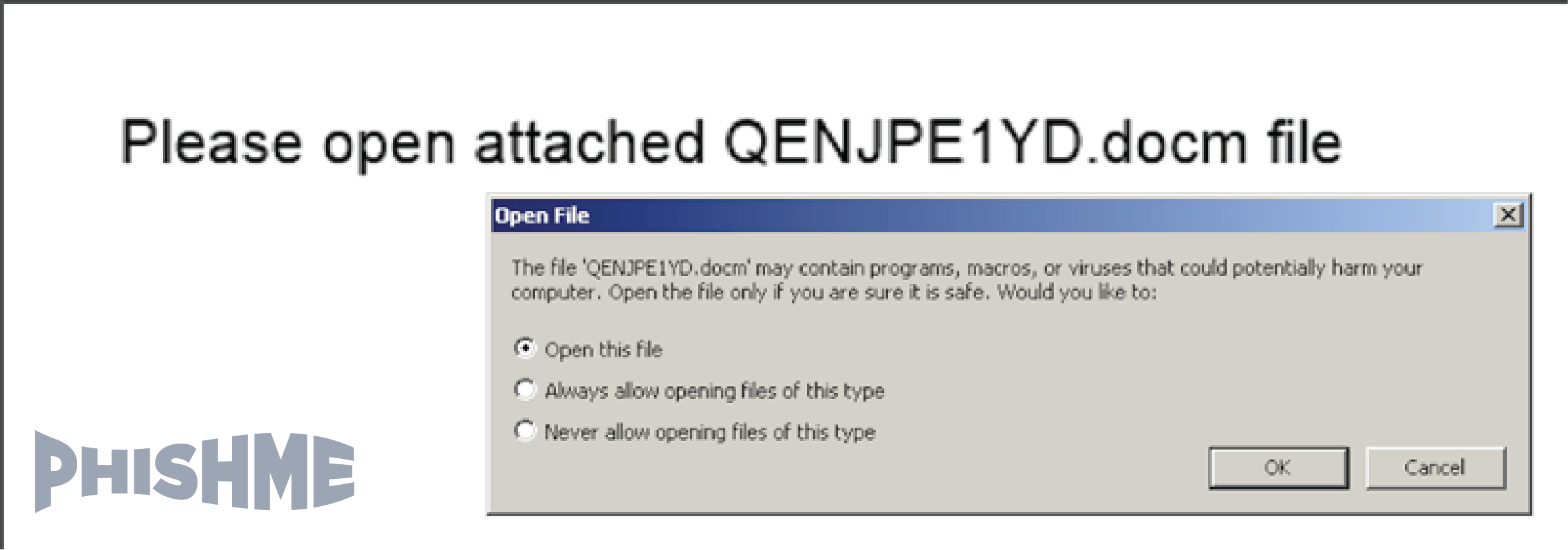
PDF reader requests permission to extract and open a Word document as seen with Jaff, Locky, and Dridex. (Source: PhishMe) Each attack email also comes with no message content or subject line. Researchers have seen this tactic before in other attack operations like Blank Slate. Bad actors don't provide any content in the hope that curiosity will move recipients to open the email attachment. Upon execution, the malware attempts to achieve persistence with its new Windows Task. PhishMe's Brendan Griffin provides further details about this change:
"... [T]his renewed threat actor utilization also brings a very subtle refinement to the overall polish of the TrickBot deployment intended to improve its rate of successful infection as well as its likelihood to persist undetected on infected endpoints. The TrickBot malware relies on a Windows Task to ensure its persistence within infected environments. This task is defined by an XML file written to disk after TrickBot is initially run. Early examples of this persistence task were named 'Bot' and would show up as such during audits of system tasks. However, this most recent iteration of task from 'Bot' to the much less obvious 'services update'. While this refinement may seem insignificant, it portends a much more serious approach on the part of the threat actor. One of these two filenames would look entirely out of place within an infected environment while the latter would be more reasonable–perhaps reasonable enough to escape detection."
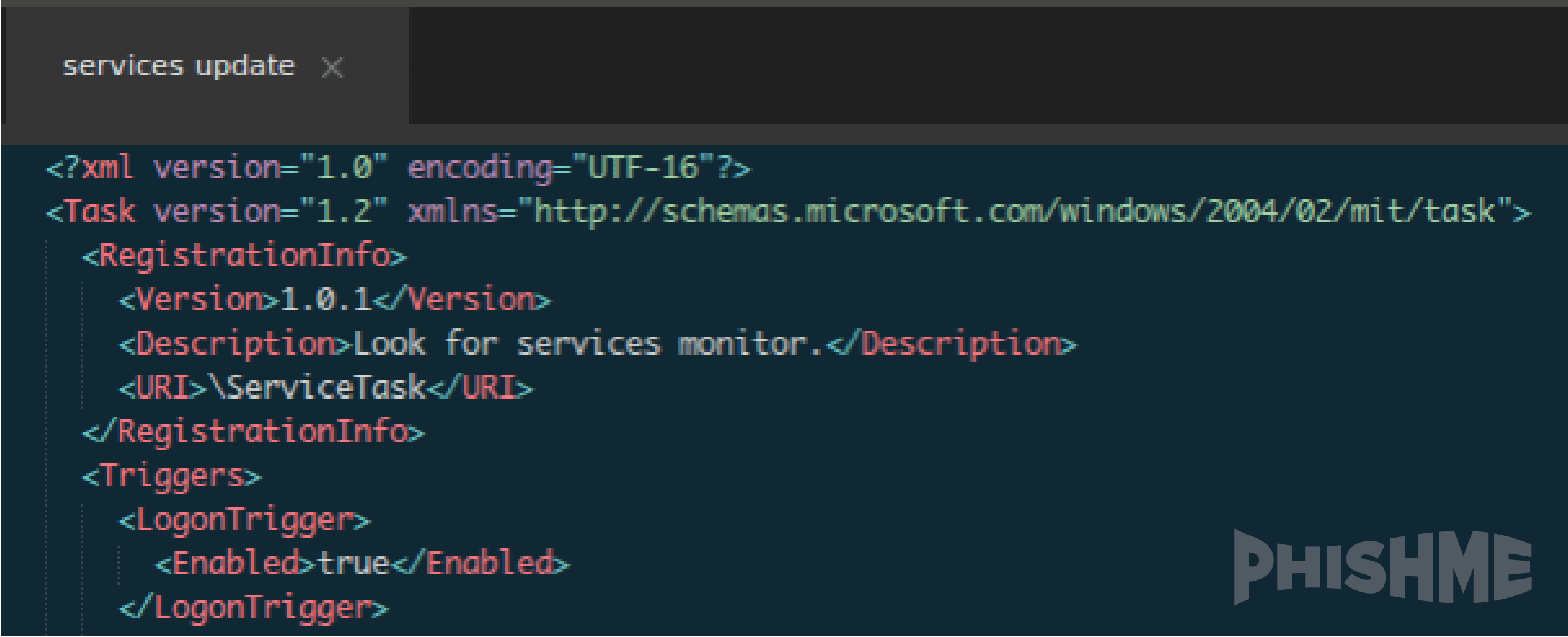
An excerpt from the “services update” Windows task. (Source: PhishMe) While the "service update" Windows Task can help conceal TrickBot upon infection, users can defend themselves against this attack campaign by focusing on the initial infection vector. Specifically, they should exercise extreme caution around emails that lack message content and subject lines. In most cases, they can send these messages to the trash bin. But in the event they do go ahead and click on the attachment, they should refrain from enabling macros in unknown Office documents, and they should not download Word documents embedded in suspicious PDFs.

