
Cybercriminals are leveraging social media to lure unsuspecting users into handing over their online banking credentials. According to researchers at security firm Proofpoint, a new series of phishing attacks has been seen targeting customers of major UK banks via Twitter. The attack is carried out as follows: First, cybercriminals create convincing fake customer service accounts with a handle similar to the bank’s real customer support account, explained Proofpoint. Then, they wait for customers to tweet at the legitimate bank accounts with a help request. When the customer attempts to contact the bank, the attacker hijacks the conversation by responding with a bogus support link sent from the fake support page, said Proofpoint.
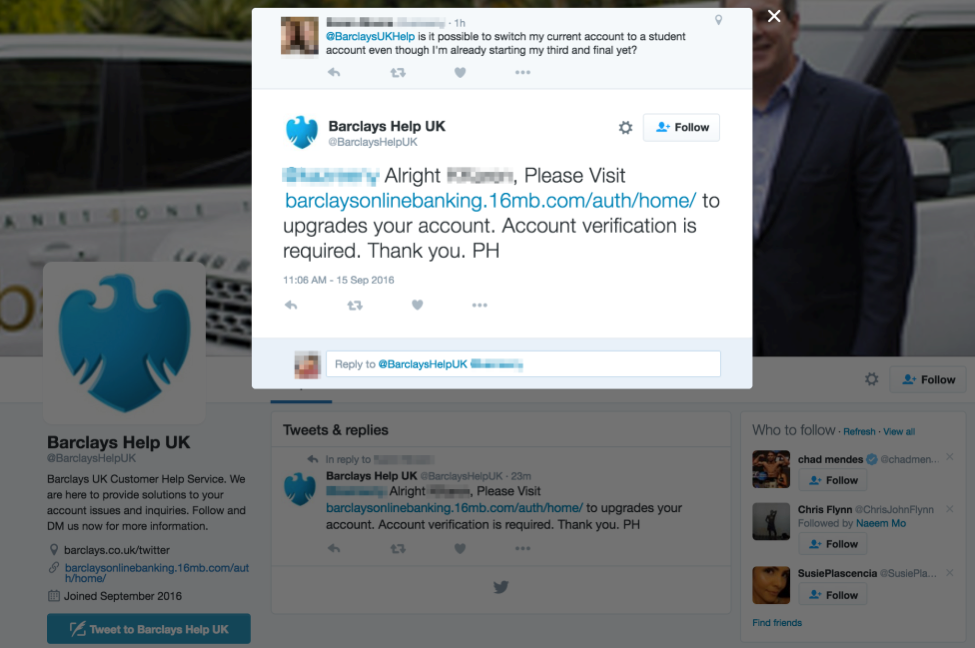
In this particular instance, we see a customer tweeting at the real Barclays Bank handle – @BarclaysUKBank – inquiring about student banking. Cybercriminals promptly responded from a fake customer support account with the handle @BarclaysHelpUK.
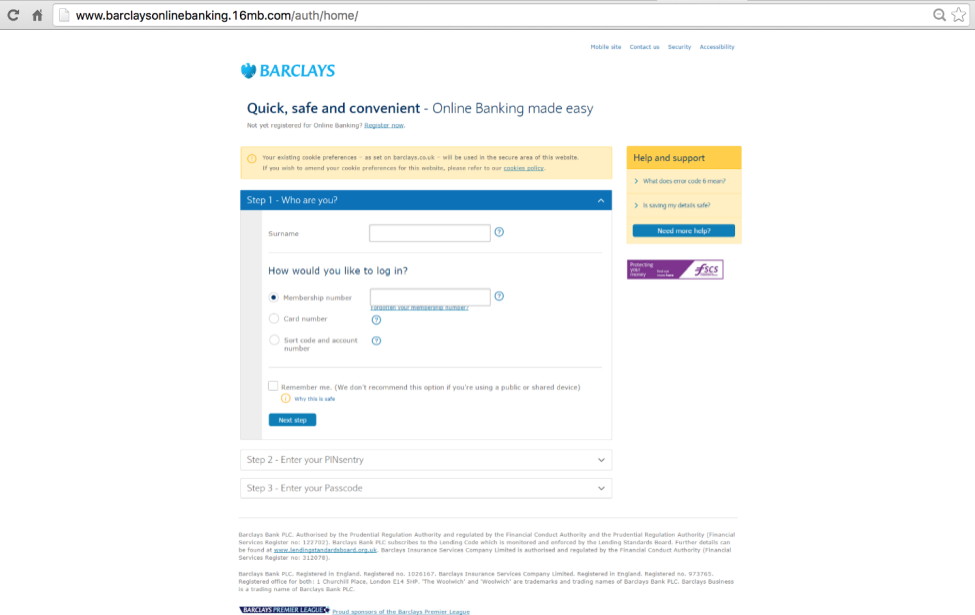
The link in the fraudulent response directs users to a lookalike login page intended to steal the customer’s information, including their surname, membership number, card number and more.
“This method of phishing is highly effective because customers are already expecting a response from [the bank],” said Proofpoint.
The security firm warns that such tactics are part of a growing threat as social media phishing increased more than 100 percent between Q2 and Q3 of 2016. To protect against these attacks, users are advised to always proceed with caution when engaging in conversations on social media. Twitter accounts of legitimate businesses will generally have a blue verified tick to indicate the account is authentic, and will never ask for login credentials. Additionally, users should check for the number of followers on the account. Unlike scam accounts, real customer support handles will likely have a much larger following. For more tips on how to protect against phishing, click here.

