
A popular WordPress plugin has fixed a vulnerability that allowed an unauthenticated user to download the subscriber lists for more than 100,000 websites. Email Subscribers & Newsletters incorporated the fix into version 3.4.8 on 19 January after working closely with Dominykas Gelucevicius from ThreatPress, a company which offers security products and services for WordPress users. Gelucevicius says the vulnerability exists in all plugin versions prior to 3.4.8. He went on to explain the issue in an email with The State of Security:
The exploit of the security gap is as follows: HTTP POST request is send[sic] to the website address that ends with /?es=export parameter, adding extra POST data, option=view_all_subscribers . The file that exports data is export-email-address.php, which also accepts parameters like view_active_subscribers, view_inactive_subscribers, registered_user, commentposed_user .
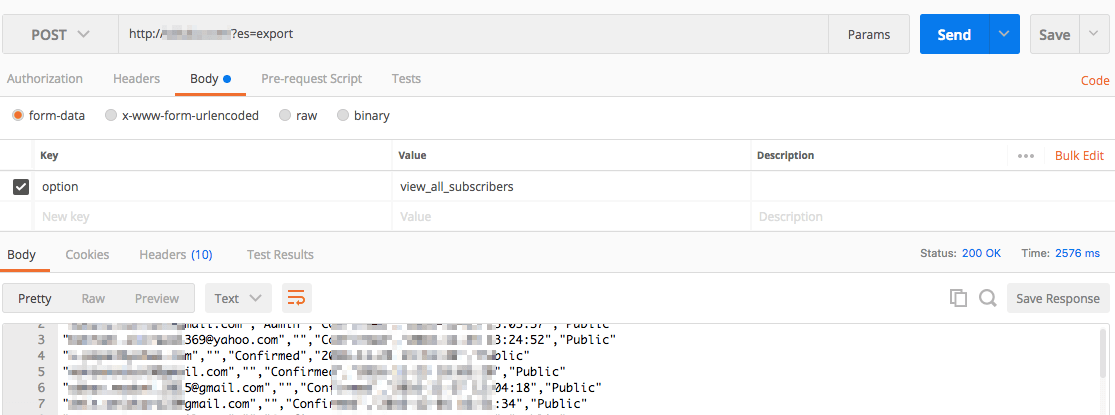
A screenshot in which the data leaked from Email Subscribers & Newsletters has been masked. Using a simple query, PublicWWW.com determined it was easy to find more than 80,000 websites that use Email Subscribers & Newsletters. (The plugin's official page says there are more than 100,000 websites that use it.) A bad actor could then exploit the vulnerability to "yield hundreds of thousands e-mail addresses with names," in Gelucevicius' words. This isn't the only flaw recently uncovered by ThreatPress. In 2017 alone, the security company added 221 vulnerabilities found in plugins and themes from multiple sources to its database. More than a third (35.1%) of those bugs were cross-site scripting (XSS), followed by SQL injection (19.8%) and unrestricted access (9.9%).
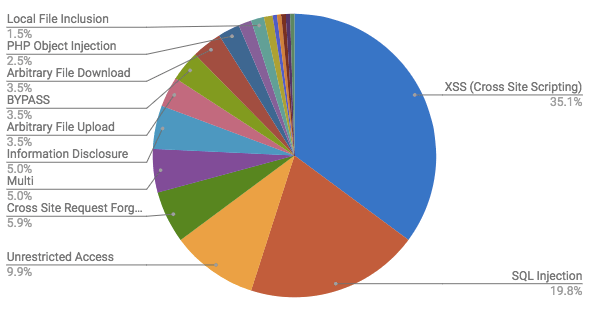
A representation of the plugin and theme vulnerabilities discovered by ThreatPress in 2017. Overall, ThreatPress estimates that vulnerabilities in plugins and themes put at least 17,101,300 websites at risk in 2017. Any organization that uses Email Subscribers & Newsletters with their website should update their plugin as soon as possible. They should also consider investing in a vulnerability management solution so that they can discover and prioritize bugs in all assets on their network. To learn how Tripwire IP360 can help in this regard, click here.

