
Security researchers have spotted a sophisticated type of malware that is capable of bypassing CAPTCHA authentication systems in the Google Play Store. According to a blog post written by Bitdefender security researcher Liviu Arsene, the malware, which has been identified as Android.Trojan.MKero.A, seems to have somehow found its way into legitimate apps hosted on the Play Store and simultaneously evaded detection by Google Bouncer, the tech giant's vetting system. The purpose of the malware is to subscribe mobile users to premium SMS services without the victims noticing. First, MKero bypasses the CAPTCHA systems that most of these SMS services use in an effort to prevent fraud.
"The Trojan’s sophistication lies in its ability to bypass CAPTCHA authentication systems by redirecting these requests to an online image-to-text recognition service, Antigate.com," writes Arsene. "Because the online service relies on actual individuals to recognize CAPTCHA images, requests are sent back to the malware within seconds so that it can proceed with the covert subscription process."
After receiving the CAPTCHA request, the Trojan interacts with a command-and-control (C&C) infrastructure to load the CAPTCHA code onto a target website, parse an SMS code for an activation link, and ultimately subscribe the user to the subscription service.
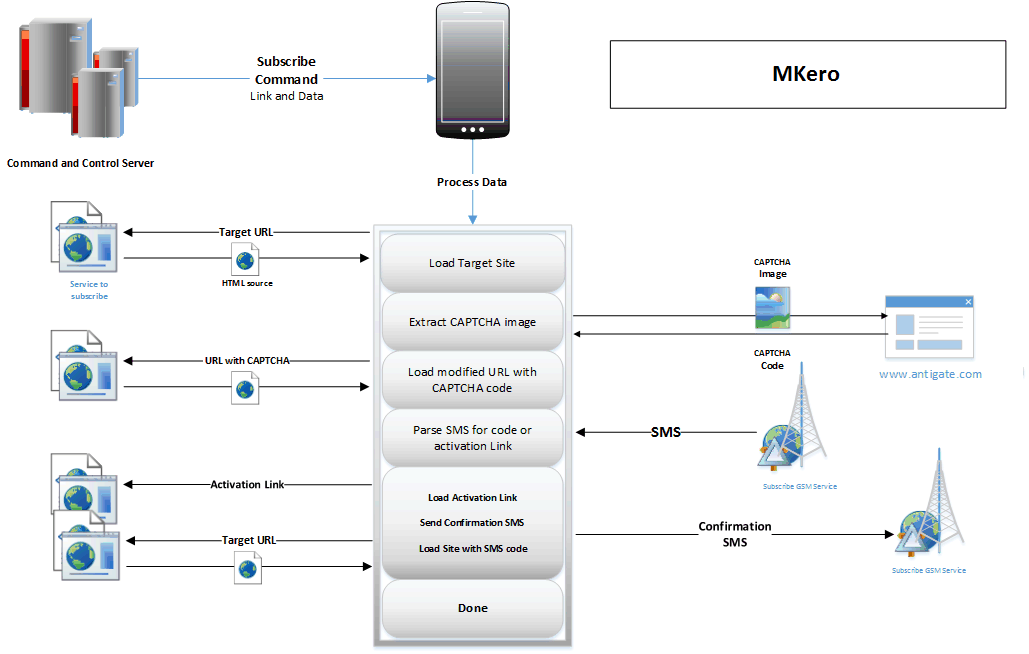
General subscription procedure (Source: Bitdefender) Google Play has been notified of at least seven apps that exhibit this type of behavior, two of which have been downloaded between 100,000 and 500,000 times.
"The total financial losses could amount to a staggering $250,000 purely from the minimum $0.50 charge by subscribed SMS messages," Bitdefender's researchers say.
In order for the malware to discreetly subscribe users to a premium SMS service, it requires administration privileges to block notifications to the victim's device. Users are therefore urged to read the permissions of each app they download carefully, as well as consider downloading a mobile anti-virus solution to scan their devices for malware. News of this Trojan follows Google's announcement back in March of new procedures designed to eradicate malware from the Google Play Store.

