
The 18th annual Black Hat USA conference gathered thousands of professionals, researchers and enthusiasts to discuss not only the industry’s current trends and threats but also what we, as a community, can do to improve the security of ourselves, and of those around us. With over 100 briefings to choose from, this year’s presentations discussed a variety of issues. We saw a particular interest in topics around industrial control system (ICS) security, mobile vulnerabilities and exploits, the rise of the Internet of things, privacy, as well as legislation affecting cybersecurity. For those of you who missed Black Hat, we’ve compiled a short recap of some of the intriguing presentations we attended while at the show.
Certifi-gate: Front-Door Access to Pwning Millions of Androids
Speakers: Ohad Bobrov & Avi Bashan (@checkpointsw) Ohan and Avi from Check Point’s mobile threat research team revealed their findings on “Certifi-gate” – a previously unknown vulnerability present in the architecture of popular mobile Remote Support Tools (mRSTs), which are used by IT departments, mobile carriers, and nearly every major Android device manufacturer.
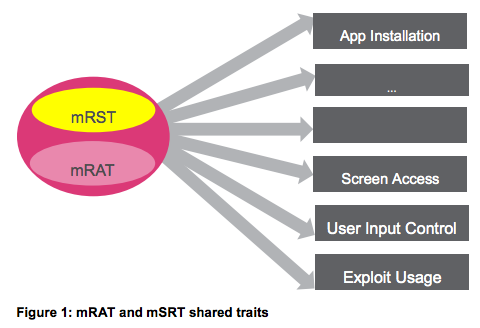
The duo began by explaining their research led to finding certain similarities between mRSTs and mobile Remote Access Trojans (mRATs). Attackers leverage mRATs to stealthily gain unauthorized access to a user’s device, giving them the capability to exfiltrate information such as photos, contacts, location, and more. Among the common traits they found, many of them are considered privileged permissions – app installation, screen access and user input control. A big difference, however, was that MRSTs do not use an exploit to obtain privileged permissions. During their research, the team identified certificate verification vulnerabilities in mRSTs from various vendors, including TeamViewer, RSupport, AnySupport and CommuniTake. In a live demonstration, they showed how an attacker could exploit this flaw to ultimately, gain full control of the device. The team warned that this particular issue affects hundreds of millions of Android devices. The vulnerability has since been reported to vendors, OEMs and Google, but although most of the vendors have resolved the issue or began the process to, other vendors have yet to respond. See their presentation slides here (PDF).
How to Implement IT Security After a Cyber Meltdown
Speaker: Christina Kubecka (@secevangelism)

When Saudi Aramco – the world’s biggest oil producer – suffered a massive cyber attack that greatly affected business operations back in 2012, Chris Kubecka took on the seemingly impossible task of building its IT security program from scratch. Her Black Hat presentation described how she was able to do so, the lessons learned and her recommendations for security professionals. Chris explained the attack started as a targeted spear phishing attack. An internal PC was then used as a proxy by the attackers, and in August 2012, the company identified the first indicators of the compromise. By mid-August, nearly 35,000 Windows-based PCs began shutting down, and their data was wiped.
“Never underestimate how dependent you are on your information technology and systems. It’s become like oxygen. You think you can live without it but you can’t.” – Khalid A. Al-Falih, Saudi Aramco CEO
Saudi Aramco responded extremely fast – it isolated ICS and IT networks, cut off vendor support, and even shut down employee desk phones. Next, Chris came on board, “starting from zero to hero,” to get IT systems back up and running. One of the most important steps of the process was recruiting for the security and network operations center, and she gave several suggestions on how to build a successful team:
- “Don’t cheap out, good analysts are difficult to find.” – It’s also not just about the salary, employees want today’s education to address today’s challenges. Focus on employee training and development.
- “Hackers, lock-pickers, geniuses and Harlem Shakers.” – Don’t look for the corporate image, the certificates or degrees. Look for people who demonstrate they do this because it’s their real passion, not because it’s their job.
She also highly recommended making good use of your network, including recruitment agencies, as well as social networks like Reddit. When it comes to building an incident response team and CERT, Chris mentioned the ENISA CERT Exercises Handbook as a great, free resource. One of the biggest lessons learned for Chris was that an incident like this is going to affect corporate culture – it will cause stress and panic for employees, and recovery will be time-consuming. But if there is one thing that can help you in the long run, it’s to plan ahead. Have a communication process in place, involve legal, PR and external resources beforehand, and it will cost you significantly less time, money and effort. See Chris’ presentation slides here.
ZigBee Exploited: The Good, The Bad and The Ugly
Speakers: Tobias Zillner & Sebastian Strobl (@cognosec)

Tobias and Sebastian of Australian security firm Cognosec discussed the gaping vulnerabilities found in ZigBee – one of the most widespread communication standards commonly used in the IoT, including home automation and smart lighting systems. Despite its widespread use, however, the two demonstrated that ZigBee’s home automation network with applied security and smart home communication is not properly protected.
“Due to interoperability and compatibility requirements, as well as the application of legacy security concepts, it is possible to compromise ZigBee networks and take over control of all connected devices.”
The ZigBee protocol is based on an “open trust” model, the researchers explained, meaning all protocol stack layers trust each other and cryptographic protection only occurs between devices. In other words, every layer is responsible for the security of their respective frames. The security of ZigBee networks is based on encryption keys. Its security architecture is dependent on:
- Safekeeping of the symmetric keys
- Key protection mechanisms employed
- Implementation of the cryptographic mechanisms
To verify the implementation of ZigBee’s applied security measures, the researches tested a door lock, a smart home system and lighting solutions using their newly developed security-testing tool SecBee. The results were that all tested systems only use the default TC Link Key for securing the initial key exchange. They found that no link keys are used or supported, leading to a complete compromise after they were able to get the network key. Furthermore, they found that device resets were often difficult to complete, with one device not supporting the reset at all.
“Every assessed device showed that the solutions are designed for easy setup and usage but lack configuration possibilities for security and perform a vulnerable device pairing procedure that allows external parties to sniff the exchanged network key.”
For additional information, read the white paper here (PDF).
Pen Testing a City
Speakers: Greg Conti (@cyberbgone), Tom Cross (@_decius_) & David Raymond (@dnomyard) This high-level presentation examined a penetration testing framework, and demonstrated how its methodology could be applied for a city-level penetration test. The team began by explaining that the security of countries and nations is based on cities. Even without an adversary, certain disruptions can paralyze a city for hours, days or weeks, impacting hundreds of thousands to millions of residents. But these scenarios are typically happening by accident, and now, the infosec community has done great research and provided point cases that make this a very real and imminent threat.
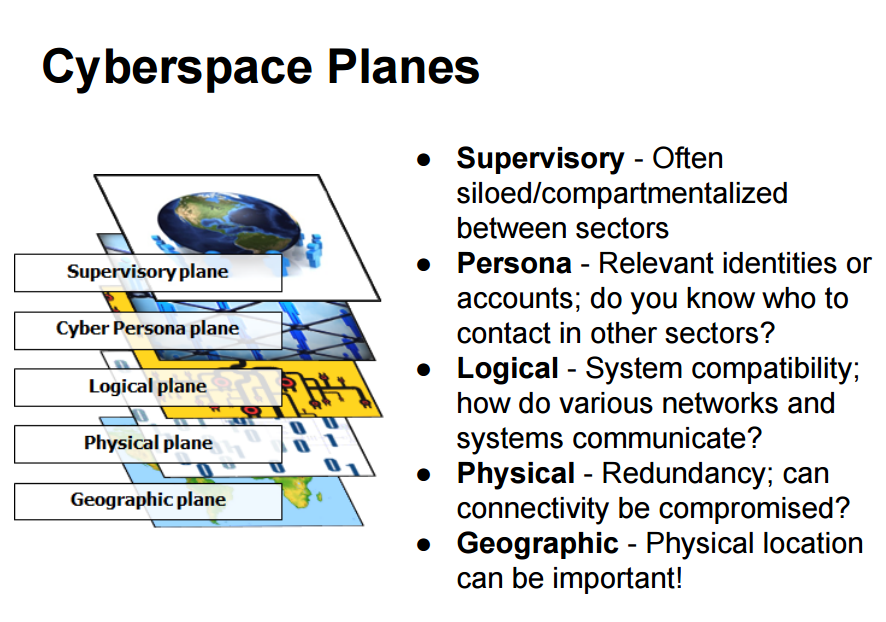
The three noted that there is a big delta between securing a company, and securing a city, so using the SANS network pen testing process as a building block, they created a more robust process that could be executed at the city level. They then demonstrated how to dissect a city in order to understand how a city’s IT infrastructure is organized. They broke it down into “cyberspace planes,” starting from the supervisory and the cyber persona planes, down to the physical and geographic planes. Next, they noted that each city has a different mix of critical infrastructure sectors, making each of their attack surfaces very different. For example, New York City’s financial sector is seen as the city’s source of power and strength, and if attacked, it would cause immense damage; the same goes to Las Vegas’ gambling industry or the oil and energy companies in Houston, Texas. The team also outlined previous research, many of which has been presented in previous Black Hat and DEF CON conferences, showing the potential vulnerabilities a city might face, such as hacked wireless traffic control systems and electronic road signs; smart parking meters; gas stations; ATMs; elevators; water plans; and airport security and air traffic control. Lastly, the researchers detailed the cascading effects of such event, potentially leading to major disruptions of a city’s critical and non-critical infrastructures. They proposed a variety solutions and initiatives that could help solve these security challenges.
“By understanding a city’s pressure points, and the interdependencies between critical and non-critical infrastructure sectors, we can test the limits of a municipality’s defenses and find ways to mitigate vulnerabilities brought on by new technologies designed to improve energy efficiency and enhance livability.”
For more information, you can read the team’s research paper here (PDF).
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

