
The movie ‘Blackhat’ succeeds in highlighting the prevalence of security breaches caused by human error. Even so, it fantasizes many aspects of our digital world to help depict an international cyber crisis and flubs as a film more generally. ‘Blackhat,’ starring Chris Hemsworth and Viola Davis, is an American action thriller about a former blackhat hacker who is summoned by the FBI to aid in an investigation surrounding a cyber attack against a Hong Kong nuclear power plant. As we learn early on in the movie, the persons responsible for the attack used a remote access tool (RAT) to increase the RPM of the plant’s coolant pumps, causing them and one of the cooling towers to explode. This type of attack vector is not impossible. After all, the RAT is in some ways similar to the infamous Stuxnet attack, in which a joint U.S.-Israeli virus caused the centrifuges at Iran’s Natanz uranium enrichment site to malfunction and spin out of control. The targets, attack vectors, (Stuxnet was delivered via USB) and consequences of the two attacks are different. But at the very least, both incidents demonstrate that hackers can use cyber attacks to compromise ICS/SCADA systems.
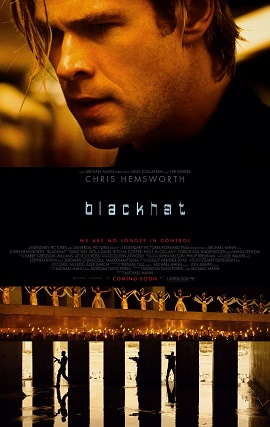
The film begins to stray from reality when we are introduced to Nicholas Hathaway (Hemsworth). Hathaway starts the film off in prison, where he is serving a 13-year sentence for hacking a number of banks and corporations. After guards search his cell, he is brought in front of the prison warden, who accuses him of having used a contraband cell phone to hack into the prison computer system, access which “gave him a command line” to transfer moneys to his fellow inmates’ accounts. Whether such an attack could have actually occurred is doubtful. Indeed, under the Trust Fund Limited Inmate Communication System program (TRULINCS), most penitentiaries in the United States limit inmates’ computer access to heavily supervised text-only activities with family and friends. Couple this with the widespread use of Wi-Fi signal jammers in prisons, it is improbable that Hathaway was able to successfully access the Internet and move around funds from inside his cell. But there’s more. The investigation into the nuclear power plant attack is headed by two FBI agents, as well as a high-ranking member of the People’s Liberation Army Cyber Division. This is an unlikely premise, at best, Given China’s refusal to aid the United States in preventing future cyber attacks from North Korea following the Sony hack, not to mention the remarks of high-ranking U.S. intelligence officers that China is one of the only cyber actors that could successfully shut down American critical infrastructure, it is next to impossible that the two countries would agree to jointly investigate a cyber attack. To do so, each side would need to reveal the internal goings-on of its respective cyber security state apparatus, vital intelligence which the other site could exploit once the investigation had concluded. Given how much each side has to lose, both the FBI and the PLA Cyber Division would likely forego cooperation in cyberspace as a strategic blunder, thereby undermining the movie’s notion of a Sino-American cyber investigation. Additionally, there is at one point mention of a secret NSA program called “Black Widow” that allegedly searches the web for code fragments and allows the U.S. intelligence community to reconstruct corrupt and partially destroyed files. But there is currently no way to piece together corrupted, fragmented bits of code, and if there were, the NSA would certainly not host it on the public Internet. These are just some of the movie’s technical faults. There are others, but in the attempt to not reveal any spoilers, I have chosen not to discuss them. To its credit, the movie does accurately capture how “human error” allows attackers to infiltrate a variety of computer systems. For example, at one point we see Hathaway’s love interest breach a bank’s computer networks by having a security officer print a presentation stored on an infected USB stick. In another scene, we learn that the nuclear plant attackers breached another target via the use of a USB stick left on an IT manager’s desk. All of these intrusions are possible and have occurred in real life countless times over, which goes to show that security breaches are everywhere—at our workplaces and on the movie screen. Unfortunately, this testament to actual security threats is not enough to save ‘Blackhat.’ Besides its technical flaws, the movie makes a number of outlandish choices that together undermine Hathaway’s tenuous position vis-à-vis U.S. federal authorities—an important sub-conflict in the film. Helmsworth also lacks in charisma and seems to find his character only when he is beating up on gunmen. To be fair, the digital representation of the RAT infecting the nuclear power plant at the beginning of the movie is aesthetically intuitive, but it lasts only a minute or two. ‘Blackhat’ has very good intentions, but when it comes down to the technical and national security details, it turns out to be another script kiddie looking for attention.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

