The Security BSides concept is brilliant. After being founded in 2009, it’s spread like wildfire. There are now dozens of regional events that take place around the world, and if you take a look at their website, you’ll more than likely find one not too far away.
For any of you that don’t know, the principles behind the idea are simple:
-
Expand the conversation.
-
Enable people to join the discussion.
-
Get people involved.
This week, I was lucky enough to attend BSides London.
The morning started with a bang – hundreds of people quickly came through the doors at 8:30 AM and made their way to the opening keynote from Wendy Nather of 451 Research.
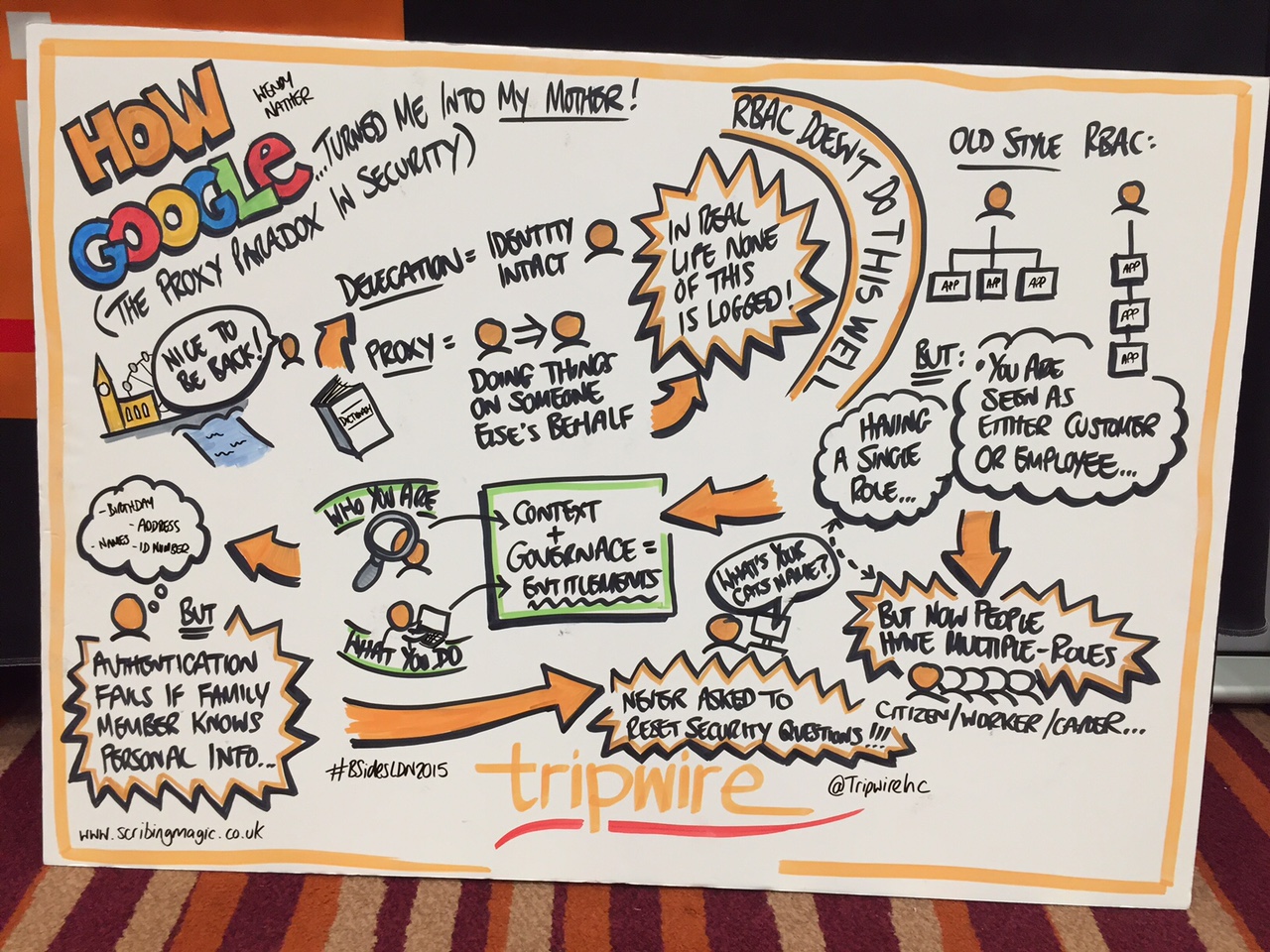
We also had a very talented graphic artist capture visual representations of some of the talks delivered.
Below is a quick read recap of some of today's presentations:
DarkComet From Defense to Offense – Identify your Attacker
Speaker: Kevin Breen (@KevTheHermit)
Kevin began talking about the history of DarkComet, a RAT that has been in the public domain since 2008 and came to light off the back of the Syrian conflict.
However, it’s no longer developed, meaning there are plenty of exploits in the system (AKA good news for the good guys and bad news for the criminals).
Kevin gave some insight about the type of people that use the RAT, ranging from "script kiddies" to governments alike.
He then followed on by diving in to the technical defense of offense aspects of the tool and then entertained us further with a series of demonstrations on how to a stop a criminal running DarkComet on both a Windows and Linux System.
It was also extremely fascinating to see the work Kevin is doing, and how you can use this tool to retrieve data and keep your environment secure.
Finally, I must point out Kevin stated that there are legal implications to using the tool, so don’t try this at home (or talk to your legal team first)!
A Look at The Real Social Engineers
Speaker: Richard De Vere (@Rfdevere)
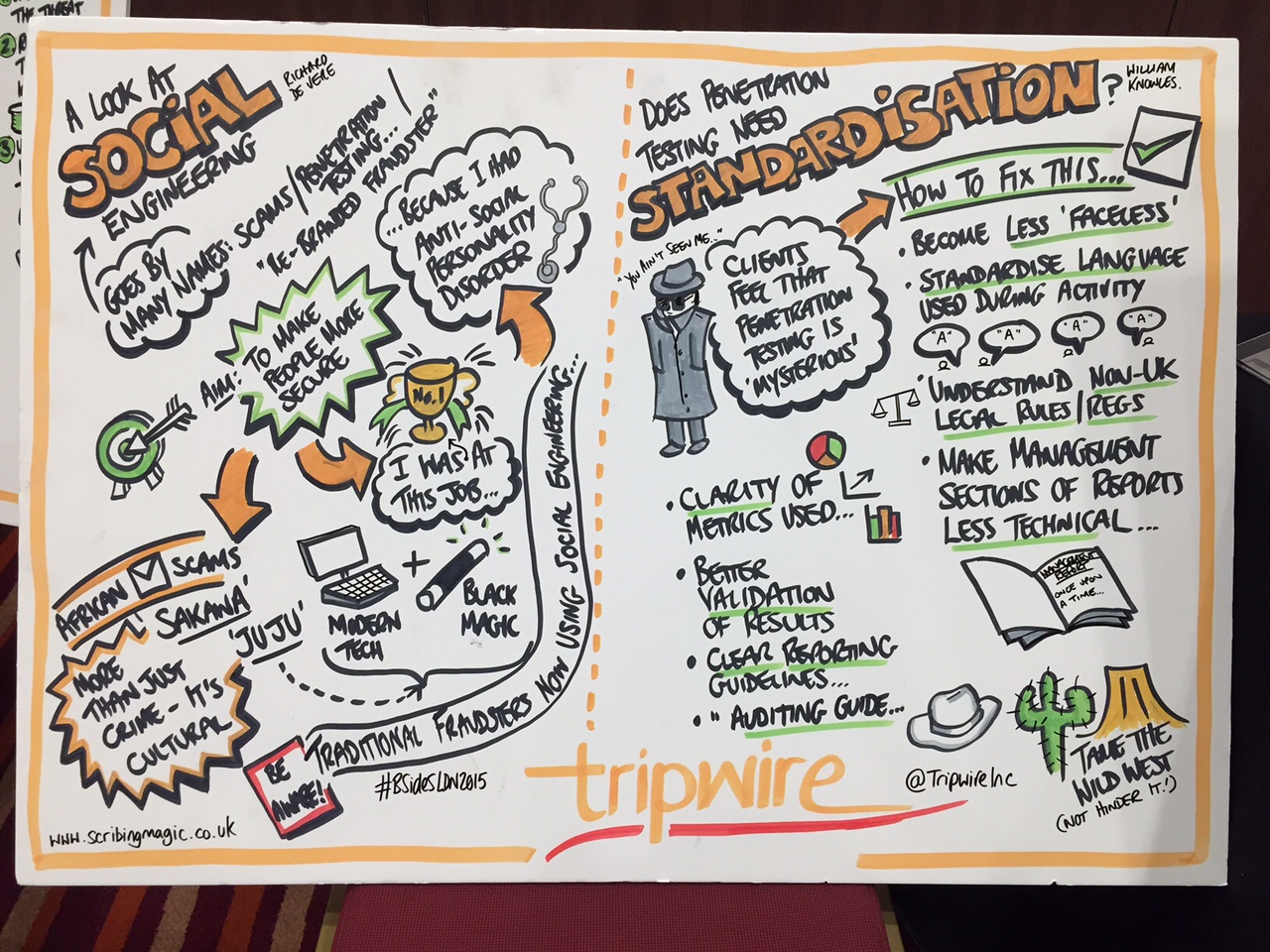
Richard De Vere is a social engineer—he’s not a developer or a researcher, and he admits he doesn’t have the same technical knowledge as a lot of the potential audience. However, his passion for security is clear to see.
The reason Richard moved in the world of security is simple: he wanted to make people safer.
Richard gave us a brief introduction into his background, and gave mention of his fourth assignment in which he walked out of a bank with a range of devices.
He then took us on a security journey, giving us real insight on what the values of African social engineers look like. It was fascinating to watch.
Talking about local cultures, “Sakawa” and “Ju Ju,” Richard explained how these guys take traditional Internet crime and believe they mix it with black magic.
The people who are working on these phishing scams are brought up to believe that the western world actually “stole their money” and they are doing the right thing in trying to get it back. They believe this so much, they will go visit a priest and pray, to hope that their phishing scams work.
It’s clear to see that the main objective is to extract money, and they use techniques to try and develop relationships with people to make this easier. However, with money comes power, and the most successful scammers use their money to obtain power in African nations.
It’s a growing issue and it doesn’t look like it will slow down anytime soon. Richard then finished off talking about who the attackers actually are, why they do it and how social engineering is now applied to fraud strategies to make it more effective.
My Love-Hate Affair with Security Operations
Speaker: Javvad Malik (@J4vv4D)
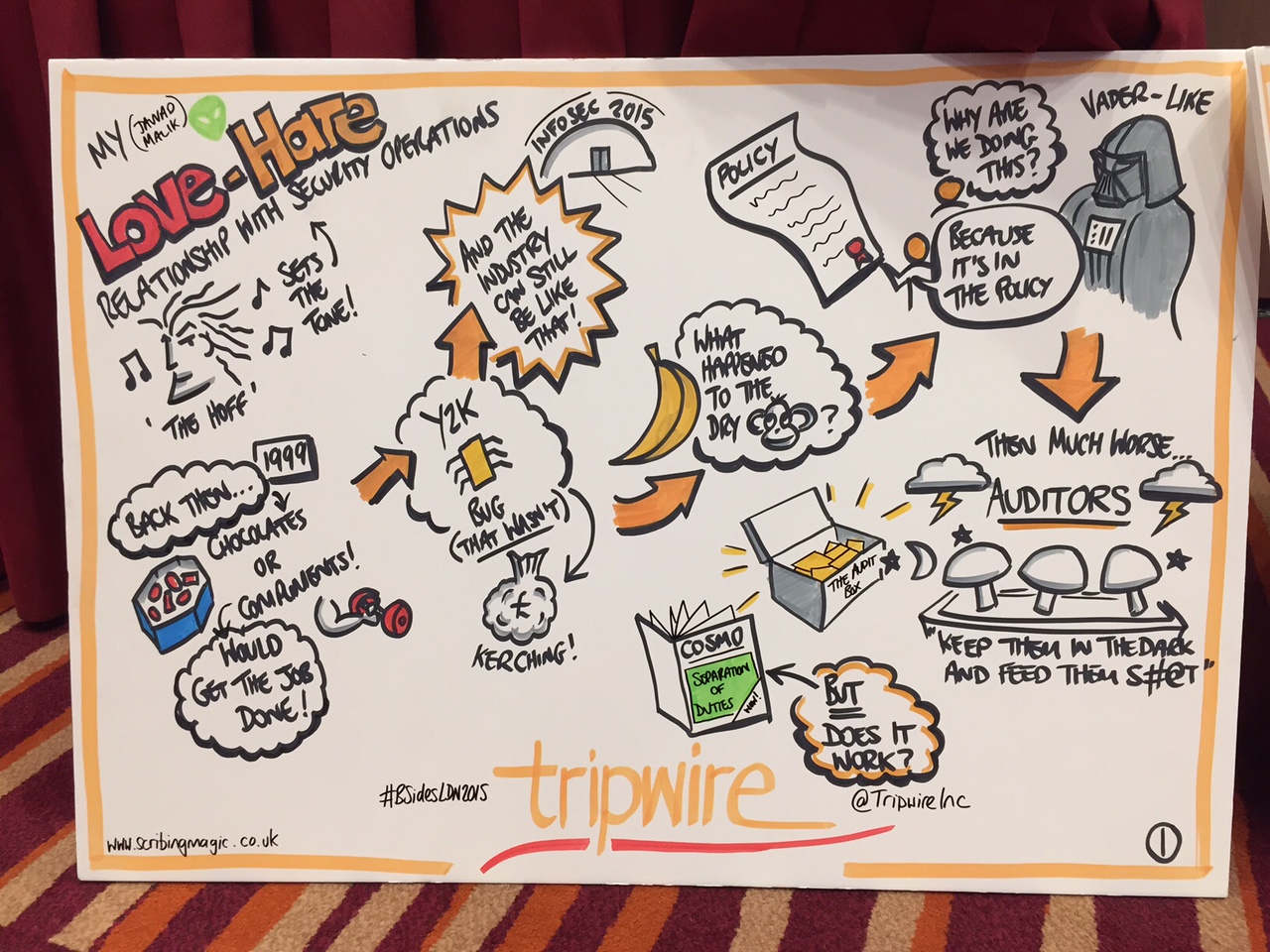
In one of the most entertaining talks of the day, Javvad set the tone from the offset, using the Hoff in Kung Fury as a catalyst to describe how he views security.
Javvad began by giving us a background on his first job back in security back in 1999. Working in security operations, one of his first experiences was dealing with the Y2K bug.
He then used the 5 monkeys in a cage analogy to illustrate how security was when he first started. People were told a lot things, highlighting the case on passwords: you should change them every 90 days, they should be a certain length, etc. But the key question was WHY?
Javvad added it was the same with policy. You ask the right questions, but get the same responses: "The policy said so!"
He then went on to talk about his experience with auditors. He entertained the crowd by talking to us about his initial dealings with a couple of auditors and how that stained his viewpoint, vowing never to entertain an auditor again.
That was until he met a certain friend, who gave him some solid advice to overcome this.
If you weren't at the talk, I’ll leave that to your imagination to figure it out…
He then went on to discuss other areas, such as separation of duties, privilege identity management and a very entertaining story on how he learned to script and create a winning formula to get a special recognition award from his employers.
He also gave an interesting story about “accepting risk,” and how people weigh up the convenience versus security argument. Often times they then decide they just need to accept “there will be a risk”—a real insight into the issues we still see today connecting the business with security.
Overall, the whole of BSides was a great experience. I got the meet new faces, I learned a lot and was thoroughly entertained by a range of talks.
Credit to the organisers of the event, they did a fantastic job and I already look forward to next year!

