It’s that time of year, again, when the brightest minds in the business gather to talk all things cyber in the city of San Francisco. To start off the busy week ahead, BSidesSF kicked off day one with some great speakers and intriguing presentations. For those of you that didn’t make it out, here’s a short and sweet recap of some of today’s talks. It was definitely a tough choice between the two tracks but fortunately, videos and slides will be made available soon! A special thanks to Kelly Kingman, our graphic artist that created very cool visualizations of the talks in real-time.
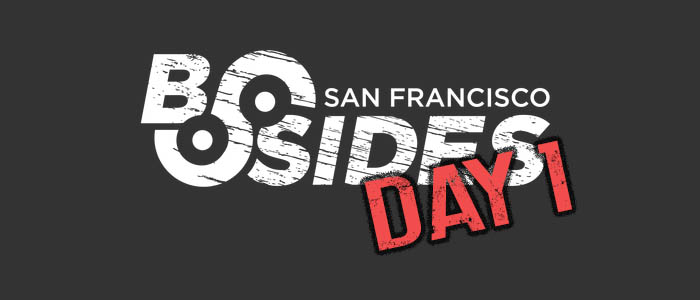
Critical Infrastructure: The Cloud Loves Me, The Cloud Loves Me Not.
Speakers: Bryan Owen (@bryansowen), Mike Jarvis (@mikejosisoft) Watch Video (Source: IronGeek)
Bryan and Mike took turns playing devil's advocate on how the public cloud could make the nation's critical infrastructure more or less secure. Giving several scenarios demonstrating how these vital utilities could be attacked – impacting the millions that depend on these services daily – the speakers examined pros and cons of utilizing the cloud to help manage these systems and their data. One example was the natural gas system, in which attackers could send signals to control gas valves or cause a line to over-pressurize. One argued, now why would we use the cloud for that? Doesn't that sound like a recipe for disaster? On the plus side, the cloud could solve several issues with wireless routers and outdated software. This maintenance could be outsourced to the cloud, letting IT teams to focus on other, more important things.
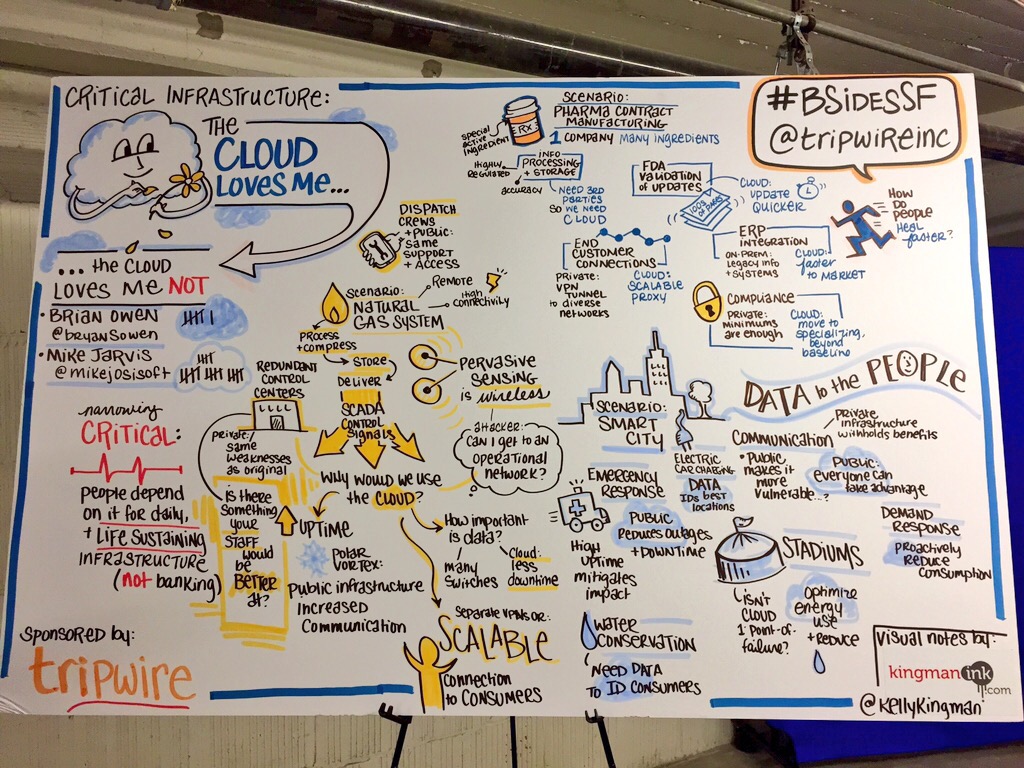
F*k These Guys: Practical Counter Surveillance
Speaker: Lisa Lorenzin (@llorenzin) Watch Video (Source: IronGeek)
A very enthusiastic and passionate Lisa Lorenzin gave some great insight on what we can do to better protect ourselves from the meta data that is being collected about us. As Lisa explained, although meta data is a hard problem to solve, the easier problem is how we choose to defend our privacy. She gave three simple tools that should be the basics for anyone that cares about their privacy:
- HTTPS everywhere. Use it.
- Duck Duck Go. Stop giving Google your search info.
- Private browsing. Every major browser now has incognito mode, which keeps these cookies from being stored.
For the more serious users wanting to go beyond these measures, Lisa also suggested various other tools, such as Privacy Badger, an alternate DNS provider, Flock, and email encryption services, that offer increased privacy for the cost of a little inconvenience.
Your User Passwords Are Already Stolen
Speaker: Lucas Zaichkowsky (@LucasErratus) Watch Video (Source: IronGeek) Lucas discussed the perils of password security, reminding us it's still a huge problem. He gave examples of several high-profile user database thefts, such as eBay, Twitch, Forbes and Adobe, and the implementation failures behind these exposures: passwords are often stores in plain text, obfuscated or encrypted (encryption keys aren't difficult to find and steal); the crypto concepts of salt or rounds aren't used; and password complexity is often hindered by character limitations. He then highlighted some of his own extensive research on cracking known password samples with surprising stats on the amount of passwords he successfully recovered, meaning users continue to use the same password not knowing it's been cracked. In conclusion, Lucas offered his tips for defensive planning:
- Use password management tools
- Use random, complex passwords
- Enforce two-factor authentication
- Mitigate risk where 2FA isn't available
- Apply least privilege access
- Audit and monitor user activity
Medical Device Security - From Detection to Compromise
Speakers: Adam Brand (@adamrbrand), Scott Erven (@scotterven) Watch Video (Source: IronGeek)
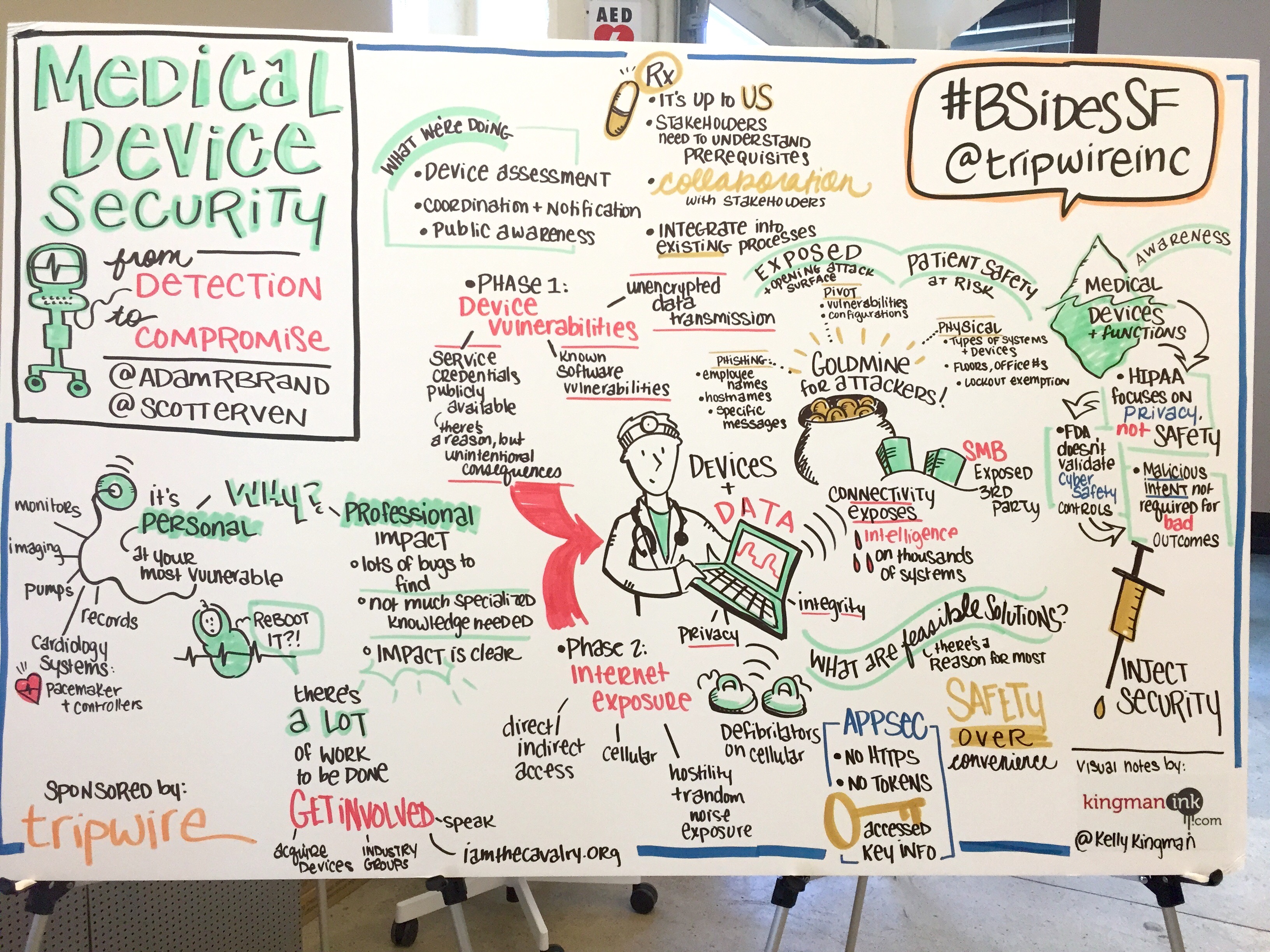
In this eye-opening presentation, Adam and Scott revealed the findings of their research on the security of numerous medical devices. From infant abduction systems and pacemaker controllers to MRIs and anesthesia systems in operating rooms, the vulnerabilities they discovered were a goldmine for attackers. The team also gave several scenarios of how an attacker could leverage these weaknesses, through physical, phishing and pivot attacks. Their diagnosis was that there is clearly a lack of patient safety alignment in medical cyber security practices, and the treatment plan falls to all of us. We must make patient safety the overriding objective, and engage stakeholders to understand the prerequisites in order to incorporate cyber safety into existing processes.
"A software-driven, connected medical device is a vulnerable, exposed one."
Are you at RSA Conference this week? If so, take a look at our in-booth activities and sessions here. See you there!

