
If you've ever attended an infosec or hacker conference, you're sure to have seen the Capture the Flag or CTF. As with anything in this industry, there are ebbs and flows in the debate of the value of the competitions. Some argue that they are unrealistic. Others champion them for the skills required and the creative thinking. Let's be real for a moment. When is the last time that a penetration tester found the output of /etc/passwd in the comments section of a website? I know there may be fringe cases, but this is not the "norm." The reality is that many are thematic and fun. Traditional Capture the Flag competitions typically have some of the same elements:
- Scanning and Enumeration
- Web Application
- Cryptography
- Steganography
- Exploitation
- Scripting
- Reverse Engineering
It's kind of ironic that scanning and enumeration and exploitation are in bold. Why? They are parts of the "Ethical Hacking process," as shown below:
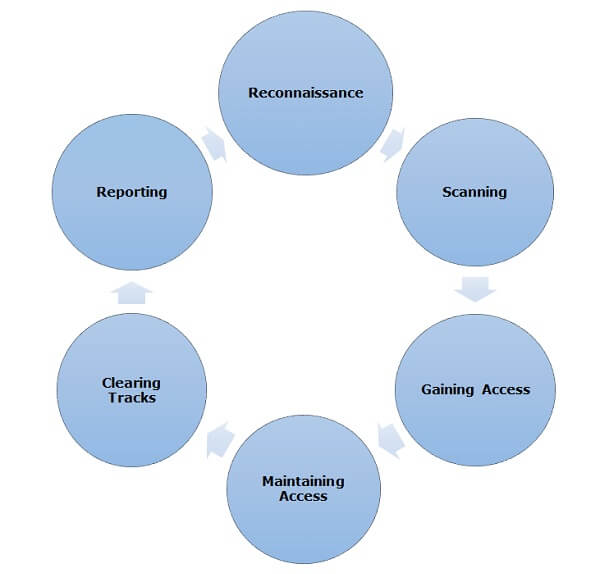
Ethical Hacking Process As time progressed, we have moved from basic CTFs to several varieties:
- Network King of the Hill (NetKOH)
- Social Engineering (SECTF) [Note: I may know a thing or two about these, especially the 2017 DerbyCon SECTF.]
- OSINT CTF
- Forensics CTF
The Value and the Series
So, what am I getting at? They are not precise mirrors of real life. That is not what they are meant to be. They are meant to be challenges to both your technical skill and creativity. Some are more "fun," and others are more about "street cred." In this series, I will be discussing how Capture the Flag exercises work and some common tools and techniques used in them. For starters and a sneak preview, here are my planned topics:
- (Theoretical Ideas) ARP Scanning with netdiscover and arp-scan
- NMAP
- Nikto
- Dirbuster and dirb
- Burp Suite
- Vulnerability scanners
- wp-scan
- Reverse Shells
- Wireless
- A wrap-up post to tie it all together.
This is not meant to be an all-inclusive series about CTFs but rather a story of my experiences in participating in the CTFs and what I have found that works. I have recently been turned on to CTFs in helping to build one for BSides Knoxville and a Forensics CTF for my local Defcon chapter dc865. I also accidentally discovered a vulnerability in a home router after doing a CTF because I had not reverted back to my non-CTF configuration. Here are some links regarding that vulnerability and the associated CVE:
- https://advancedpersistentsecurity.net/cve-2018-10641/
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10641
- https://nvd.nist.gov/vuln/detail/CVE-2018-10641
- Full Disclosure Mailing List
- https://www.peerlyst.com/posts/vulnerability-disclosure-insecure-authentication-practices-in-d-link-router-cve-2018-10641-joe-gray

About the Author: Joe Gray is a CISSP-ISSMP, GSNA, and GCIH who joined the U.S. Navy directly out of High School and served for 7 years as a Submarine Navigation Electronics Technician. Joe is an Enterprise Security Consultant at Sword and Shield Enterprise Security in Knoxville, TN. Joe also maintains his own Blog and Podcast called Advanced Persistent Security.
He is also in the SANS Instructor Development pipeline, teaching SANS Security 504: Hacker Tools, Techniques, Exploits, and Incident Handling. In his spare time, Joe enjoys reading news relevant to information security, attending information security conferences, contributing blogs to various outlets, bass fishing, and flying his drone. You can connect with him on LinkedIn here.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor and do not necessarily reflect those of Tripwire.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

