
The Jokeroo ransomware-as-a-service (RaaS) offers various membership plans through which would-be digital criminals can become affiliates. In his analysis of the ransomware-as-a-service, Bleeping Computer creator and owner Lawrence Abrams found that Jokeroo differs from similar platforms in that it offers at least three different membership tiers. These levels, he observed, attracts would-be digital attackers using various perks and incentives. As Abrams explains in a blog post:
Unlike most ransomware-as-a-service offerings, in order to become an affiliate a would-be criminal has to pay to join a particular membership package. These packages range from $90 USD, where the affiliate earns 85% of the ransom payments, to $300 and $600 packages where the affiliates keep all of the revenue and gets extra perks such as Salsa20 encryption, different ransomware variants, and different payment cryptocurrency options.
At the base membership level of $90, digital attackers have the ability to change the ransom demand, choose the extension and manage their victims using the RaaS dashboard. This utility lets affiliates know when Jokeroo infected each victim and whether they paid. It also allows them to gain even deeper insight, including a victim's Windows version, IP address and geographic location.
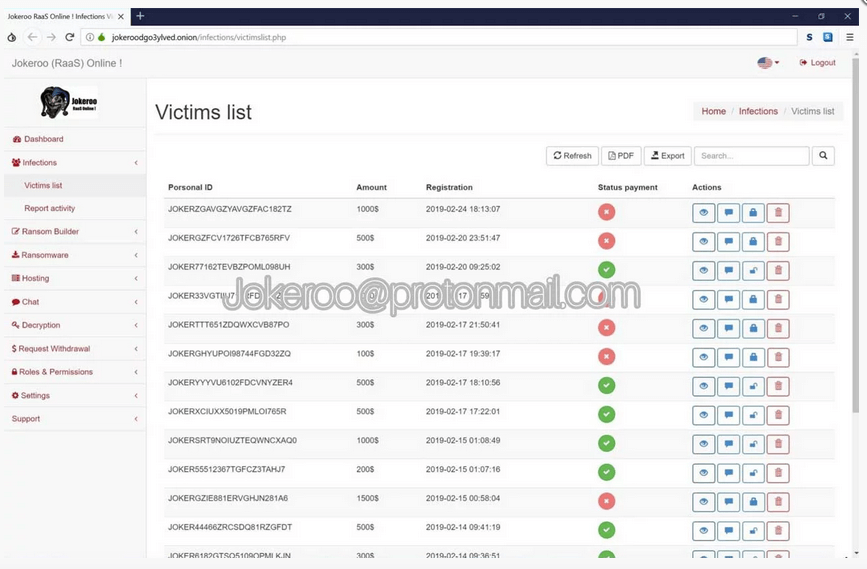
A snapshot of a sample Jokeroo victim list. (Source: Bleeping Computer) According to a security security researcher named Damien, those behind the Jokeroo ransomware-as-a-service initially marketed their creation on dark web marketplaces and hacking forums as a variant of GandCrab. This ransomware has cost victims hundreds of millions of dollars since a spike in GandCrab activity back in January 2018. Fortunately, those affected by the ransomware up through version 5.1 can now use a decryptor to recover their files for free. But Jokeroo eventually came into its own. Illustrating this fact, security researcher David Montenegro observed that malware authors eventually changed the threat's name to Jokeroo. They then began marketing the ransomware on Twitter, noting that it has "no related partnerships." As of this writing, Abrams hasn't observed Jokeroo being distributed. But that could soon change. In response, organizations should follow these steps to prevent a ransomware infection.

