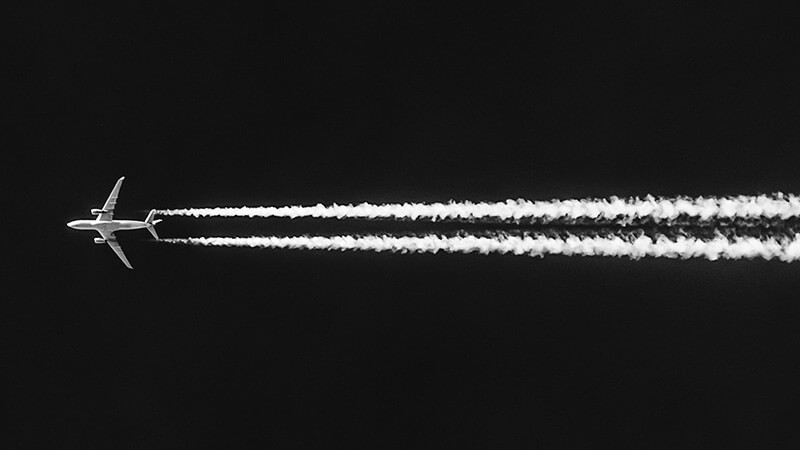
One of the major improvements that the avionics industry is undergoing is an Internet of Things (IoT) upgrade. And this is inevitably affecting how airlines approach aircraft safety. From the beginning, safety has been paramount to the aviation industry. But while it is a welcome innovation, the incorporation of IoT devices in aircraft comes with attendant challenges that are not unrelated to cybersecurity risks. Safety for aircraft no longer rests upon physical security. Now, it extends to securing connectivity between networked aircraft components, including avionics systems.
Avionics, Connectivity, and Cybersecurity Risks
In 2015, security researcher Chris Roberts was sanctioned for exploiting vulnerabilities in a United Airlines plane and causing it to fly sideways briefly. According to widely publicized report of the FBI, Roberts hacked into the plane’s In-Flight Entertainment (IFE) system while aboard the flight and tampered with the command of the plane. Three years later, researcher Ruben Santamarta hacked planes flying above by exploiting weaknesses in satellite communications infrastructure. These flaws enabled him to gain remote access to and to spy on hundreds of planes from the ground. Both events brought to light the new reality of aviation and why flight connectivity must be kept very secure. Flight connectivity is the vehicle of sensor information and analytics data flow. Any digital device can be hacked—even more so if it’s connected to the internet. The connectivity capability of airplanes boosts efficiency, but it could also create loopholes for unauthorized remote access. And since connectivity is based on networking, one cannot imagine the far-reaching damage that a hacker can wreak by exploiting one teeny-weeny loophole. For instance, according to the Design Assurance Levels set by avionics certification documents, a ‘no-effect’ danger level would be a failure that affects no more than the IFE system. Recalling what Roberts was able to do with an IFE vulnerability, significant risks exist with even these low-level security weaknesses.?
Avionics Cybersecurity Certification
As aviation adjusts to the new normal of the ‘connected aircraft,’ how can we keep avionics systems secure? Over the years, certain certification documents have been introduced to regulate information security and ensure safety on aircraft. They include DO-326A/ED-202A, DO-355 and DO-356.
DO-326A/ED-202A
The main certification document addressing aircraft cybersecurity is DO-326A/ED-202A. Titled “Airworthiness Security Process Specification,” it’s colloquially referred to as an intro to aviation cybersecurity. It is also called the cyber version of the DO-178, the main certification document for avionics software systems. The creation of a separate document for aircraft information security different from DO-178 rightly highlights the utmost importance that must be attached to cybersecurity in avionics. The guidance set in the documents is meant for implementation throughout the development life cycle, from design to deployment. The seven steps it covers are as follows: Plan for Security Aspects of Certification, Security Scope Definition, Security Risk Assessment, Risk Acceptability Determination, Security Development, Security Effectiveness Assurance and Communication of Evidence.
DO-355
The full title of DO-355 is “Information Security Guidance for Continuing Airworthiness.” It was published in June 2014 as a collection of supplementary requirements focused on operations and maintenance. It is different from DO-326A in that the latter is meant for development-wide implementation rather than for addressing maintenance needs arising from aviation information security threats.
DO-356
The full title of DO-356 is “Airworthiness Security Methods and Considerations.” It was published in September 2014 just after the introduction of DO-355. It is a companion document to DO-326A/ED-202A that proves compliance with airworthiness security requirements throughout the stages of development. It should be noted that DO-326A/ED-202A, DO-355, and DO-356 offer no guidance on physical attacks. Instead, they focus on intentional unauthorized electronic interaction including instances of malware installation and system manipulation. Aviation companies should be looking towards the full-scale adoption of the requirements in these documents for the development and maintenance of their avionics systems. That focus should be on identifying compliance gaps. The earlier in the development stage that gaps are discovered, the easier they are to fix. In addition, information security, much like physical security, requires continuous monitoring as threats keep getting exposed. Malicious actors are looking to exploit any vulnerability that they find. Therefore, security monitoring is necessary even if, and especially when, nothing seems wrong with the system. The provisions in DO-326A/ED-202A and the other documents are not yet mandatory. Currently, they mainly serve as guidelines. However, airlines that recognize its need have integrated its regulations into their avionics development processes. In any case, talks have been underway for a while to make the requirements of DO-326A/ED-202A mandatory for airworthiness across the board.
About the Author: Michael Usiagwu is an Entrepreneur, Tech Pr Expert and CEO of Visible Links Pro. He assists various organizations to stay abreast of the latest technology. Some of his insightful content can be seen in Readwrite, InfoSecurity Magazine, Hackernoon, and lots more. He’s very much open to assist organizations to increase their latest technology development. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

