In May 2017, the Equifax data breach compromised critical credit and identity data for 56 percent of American adults, 15 million UK citizens and 20,000 Canadians. The Ponemon Institute estimates that the total cost to Equifax could approach $600M in direct expenses and fines. That doesn’t include the cost of the security upgrades required to bring its IT system up to date. Around the time that Equifax became aware of its breach in 2017, Facebook incorporated vulnerable software into its video uploader. By the time that Facebook learned of the breach 14 months later, attackers had already exploited a vulnerability to compromise 50 million user accounts. The amount of data lost in the Facebook breach was less than a third than in the Equifax security incident. But the cost for losing that data will be almost three times what Equifax paid. According to Barrons, the Facebook breach could cost $1.63B in fines from European regulators alone. So, what’s the difference? Well, GDPR does permit regulators to fine companies who don’t maintain compliance up to four percent of their global revenue. (For Facebook, that was $40 billion in 2017.) But, GDPR is not the point of the story. GDPR is just the first major strand in a web of privacy regulations which trade agreements are propagating worldwide. Those agreements are dramatically raising the stakes for a data breach. As an example, Europe’s GDPR concept is connecting to regulatory efforts and influencing regulatory thinking in countries far beyond European borders. Trade agreements with Europe require that trading partners provide privacy and other protections equivalent to what GDPR offers. So, when South Korea and Japan signed formal agreements with Europe, they recognized equivalency with GDPR. But these other countries are not simply sycophants of the EU. They are true believers. Japan and Singapore have added jail time for executives in addition to financial punishment, for instance; Korea and Australia have added significant maximum financial penalties. At the same time, the recent Comprehensive and Progressive Agreement for Trans-Pacific Partnership requires that each signatory country “adopt or maintain a legal framework that provides for the protection of personal information of the users of electronic commerce” and “promote compatibility between different regimes.”
| Country | Fine | Prison & Other |
| European Union (GDPR) | 4% of global revenue | N/A |
| Singapore | $370,000 | 12 months in prison |
| Australia | $1.2 million | N/A |
| Korea | 1% of global revenue | N/A |
| Japan | $2,800 | 6 months in prison |
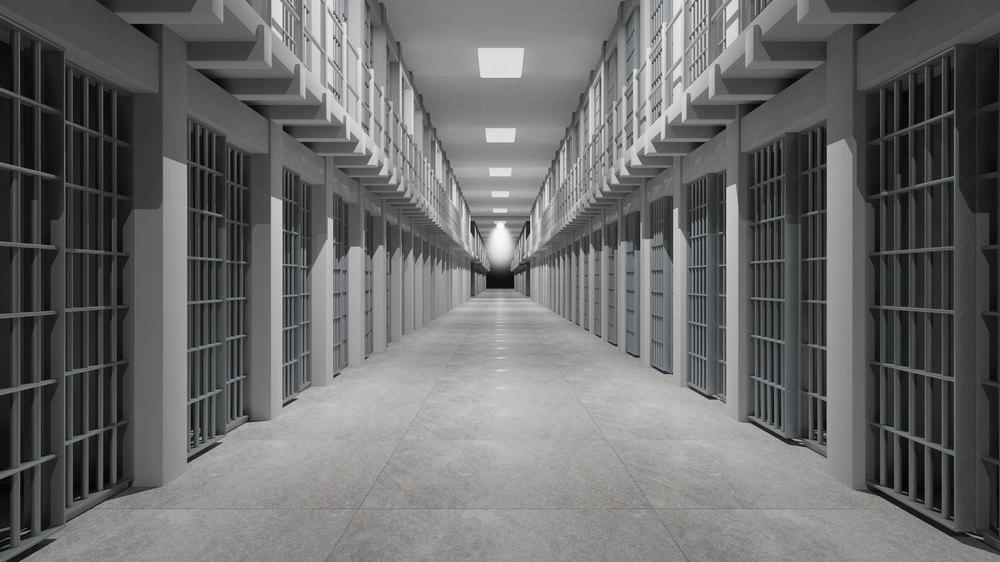
This trend toward more punitive postures should not come as much of a surprise if you recognize that more than 150 of the 195 countries in the world have privacy incorporated into their constitutions. The United States’ relatively lax treatment of privacy in general and data breaches, in particular, is the anomaly. So, the field into which GDPR was sewn is very ripe for the emergence of a tightly connected and increasingly harsh regulatory environment. Let’s tie these events back into your security efforts. International regulators are not interested in punishing companies that suffer breaches. They are interested in punishing companies that are negligent in the protection of customer data. They are also interested in making headline-grabbing examples of companies who prove to be cavalier. With that said, if your company has been pursuing “check box” security because of limited budgets, you are telling regulators that you understand the mechanisms of security but don’t prioritize it highly enough to do it thoroughly. This is probably the least defensible position that you could take when regulators come knocking. Fortunately, the changing regulatory environment could provide an opportunity to revisit security budgets. At the next budget meeting with senior executives, open the discussion by estimating the international data reserves that you presently hold. On the second slide, provide details about the potential penalties in each country. Sprinkle in a few photos of Singaporean penal facilities to provide color and interest. Then introduce a comparison of what your department has deployed versus what you need to do the job right. Tripwire can help. We use the Center for Internet Security’s Critical Security Controls (CSCs) to help protect customers against digital threats. Learn more here.

