
Tripwire recently hosted a webcast entitled, “Talking To The Board: How To Improve Your Board's Cyber Security Literacy -- UK Edition.” For the presentation, Amar Singh, Interim CISO and Founder of both Cyber Management Alliance and Give01Day, an organization that connects volunteer information security professionals together with charities seeking to protect their networks; Ray Stanton, the Executive Vice President at BT Group; and Gary Cheetham, CISO at NFU Mutual, joined Paul Edon, Director of Customer Services at Tripwire, to discuss how infosec professionals can successfully report on security issues to their organization's executives.
In order to optimize these types of executive encounters, it is crucial that we as security personnel understand the extent to which our interests and responsibilities differ from the Board of Directors. We are charged with mitigating network vulnerabilities and reporting on security incidents if and when they should arise. These duties differ significantly from those of the organization's executives, who must synthesize our reports as well as intelligence from the other departments in an effort to grasp how they can best advance the interests of the enterprise as a whole. With this different perspective in mind, we would be remiss to presume that the Board of Directors is necessarily comprised of technical experts. In fact, one of the key lessons that emerged out of both an earlier U.S. version of this same webcast and a post synthesizing the thoughts of leading security experts on cyber security literacy is the fact that executives speak a language that is oriented towards business risk and not security risk. Security personnel must therefore adopt this particular risk orientation if they are to successfully communicate their reports to the Board. One word best encapsulates these sentiments: relevance. As Ray Stanton explained in the webcast, executives can best understand threats when we relate to them the enterprise's potential exposure--that is, the possibility of financial and reputational damage--in a fact-based, passionate (but level-headed) manner. After all, a Board of Directors is able to cut through the drama and get to the facts and figures of a threat; Amar Singh noted that many did just that following the disclosure of the Heartbleed bug last year. Pandering to media hype does not lead to valuable budget, yet translating the impact of a security risk into business impact just might. Building off of and closely related to business-relevant information is the idea of context. As we all know, the roles and personalities that comprise a Board vary across (and oftentimes within) organizations. Any message that seeks to explain the security impact of an incident must therefore cater to the viewpoints and interests of these individuals. To illustrate, Gary Cheetham in the webcast discussed how in response to incidents such as the Target breach back in 2013, it is important to convey to your Board whether the same kind of intrusion could happen to your organization. This exchange would also demonstrate that you are up-to-date with important happenings in your field, which will make the executives more willing and eager to engage you in the future. The webcast panelists expand upon this notion and suggest that proactively building relationships, such as meeting key stakeholders in regular one-on-one 30-minute calls, can lay the ground for valuable alliances in the event of a future incident.
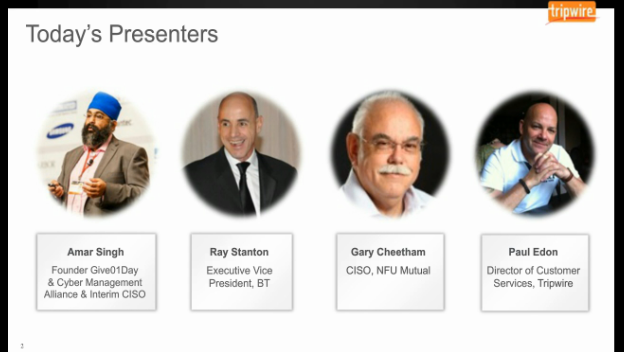
Amar Singh, Ray Stanton, and Gary Cheetham go on to discuss the types of language we should use when engaging executives, to what extent issues such as compliance and risk factor into their organizations' business priorities, and what (if any) "golden tickets" security personnel can use to gain immediate access to budgetary resources. To hear the three speakers discuss these and other topics, please listen to the full webcast here. To learn more about how you can improve your Board's cyber security literacy, please click here to read the results of a May 2015 survey sponsored by Tripwire. Alternatively, you can read a whitepaper on or click here to learn more about Tripwire's engagement with the subject in general.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

