
On March 27, 2020, President Trump signed an unprecedented $2 trillion stimulus package into law. The legislation received support from both chambers of the U.S. Congress for its goal to minimize the economic effects of the global coronavirus 2019 (COVID-19) pandemic, reported CNN. A key component of that package was the direction to provide economic relief to Americans in the form of stimulus checks of varying amounts depending upon their income. Digital attackers know this financial assistance is on its way, which is why various U.S. governmental entities are warning consumers and businesses to be on the lookout for scams. In early April, for instance, the U.S. Internal Revenue Service (IRS) raised the alarm about phishing campaigns that could seek to steal their personal and/or tax-related information. It was just a few days later when the Federal Bureau of Investigations (FBI) revealed that it had detected an increase of coronavirus-themed business email compromise (BEC) scams targeting municipalities. These financial ruses, not to mention other COVID-19 ploys, will continue to prey upon users for the foreseeable future. But awareness can help to prevent people from falling victim to these schemes. That's why we at the State of Security feel it's necessary to stay on top of the latest scams exploiting the coronavirus. Let's look at some attacks that recently made headlines.
Woman's Home Raided After Lie of Neighbor's Death

A View of Grasmere Road in Oldham. (Source: BBC News) According to BBC News, police responded to reports of a burglary on Grasmere Road in Oldham, a town in Greater Manchester. A 92-year-old woman suffered this burglary after she received a visit from some unexpected guests. These individuals knocked on the woman's door and informed her that her neighbor had died of COVID-19. That was their first lie. Their second lie came when they offered to clean the woman's house for free. But they did no such thing. Instead, they stole a purse, some money and some jewelry, a crime which left the victim "understandably distraught."
Nigerian Prince Scams in the Age of COVID-19
The rise of coronavirus-themed ploys has not diminished the prevalence of Nigerian Prince scammers. Indeed, PhishLabs discovered one example in which digital fraudsters impersonated the U.S. Department of Treasury. Those responsible for this email claimed that the United Nations and the U.S. President had instructed them to "release all unclaimed ATM card to the beneficiary to curtail the recession because of the outbreak of the Corona Virus." All they needed was a one-time $50 fee.
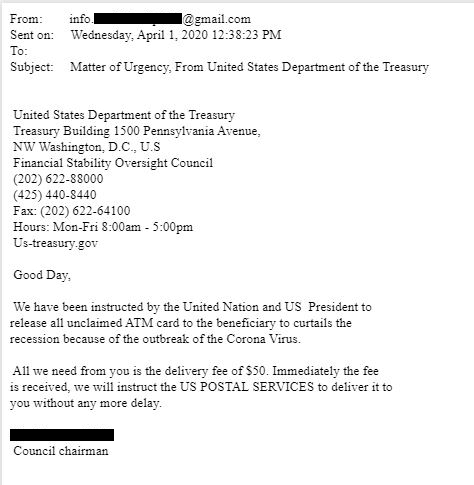
The Nigerian Prince scam in which fraudsters masqueraded as the U.S. Treasury Department (Source: PhishLabs) PhishLabs also observed a ploy that originated from a compromised email account at a medical organization. In this message, the scammer informed the recipient that the World Health Organization (WHO) had decided to award them with a grant of $550,000 in order to combat the coronavirus. They then instructed the recipient to contact the burner email address "who.specialfundsdpt01@gmail[.]com."
LokiBot Infostealer Hidden in Fake WHO Guidance Doc
Many digital attackers are understandably eager to impersonate the WHO as a means of disseminating their ruses. In one example observed by Fortinet, for instance, malicious actors spoofed the WHO to advertise the creation of a document that allegedly contained instructions on how residents could protect themselves against COVID-19. All they needed to do was open an attachment with the name “COVID_19- WORLD HEALTH ORGANIZATION CDC_DOC.zip.arj.”
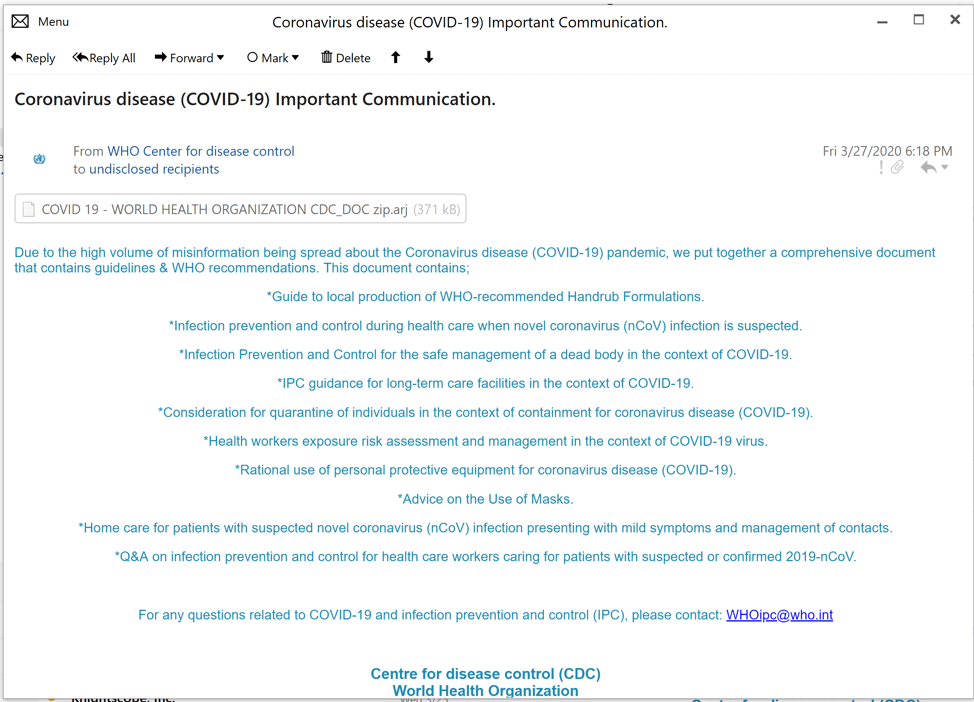
Body of scam email (Source: Fortinet) When decompressed in 7-zip, this attachment revealed that the file took on "DOC.pdf.exe” as its extension. Users who overlooked this change and activated the extension inadvertently infected themselves with Lokibot, a well-known family of info-stealing malware.
Evasive Phishing Campaign Leveraged Coronavirus-Themed Work Files to Steal Credentials
Not all coronavirus-themed email scams are rudimentary in design and execution. Menlo Security spotted one campaign that used multiple attack techniques to target 100 companies located in Asia and the United States. The operation began with a personalized email that appeared to come from the organization's CEO. Malicious actors made this email convincing by researching the target organization beforehand and by copying design elements like the footer and layout from legitimate pieces of correspondence. In an effort to bypass organizations' mail filters, these attack emails delivered PDF documents containing shortened links that invited recipients to read about their employer's "COVID-19 employee benefits."
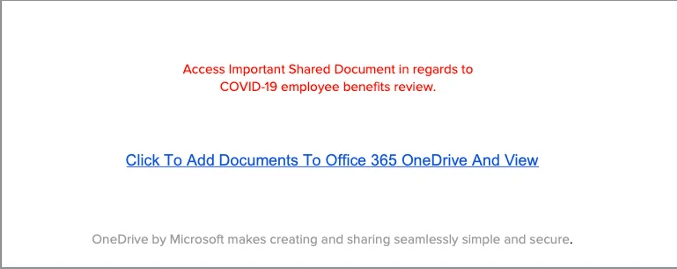
Users who clicked on the link found themselves redirected to a form hosted on a real Microsoft service. This form instructed them to submit their login credentials, presumably for the purpose of enabling attackers to access their business accounts and the sensitive information potentially stored therein.
Blood from COVID-19 Patient Sold on Dark Web?
In a truly bizarre scam shared by McAfee, a fraudster who claims to have been infected with COVID-19 offered to sell their blood and saliva for $1,000 on a dark web forum. They claimed that they were doing this to "provide for [their] family financially." You can see the original ad in a Twitter post embedded below: https://twitter.com/ChristiaanBeek/status/1244560044273868803?s=20 Whoever created this advertisement more than likely wanted to scam someone on the dark web forum out of $1,000. Then again, there's no way to prove whether this was a scam or a legitimate offer.
Man Arrested for €6 Million PPE Scam
And now for some good news! Europol announced the arrest of a 39-year-old man who had masqueraded as a legitimate company and promised to deliver personal protective equipment (PPE) such as FFP2 surgical masks and hand sanitizers. Through these efforts, the individual defrauded a French pharmaceutical company out of €6.64 million. The company had delivered this sum to a bank account based in Singapore, yet the "provider" never responded, and no supplies ever arrived. After hearing of this theft, Europol reached out to its counterparts in Singapore. Local law enforcement authorities responded by blocking part of the payment that had been made in the scam. They also identified the man responsible for the ruse and arrested him shortly thereafter. Have you seen a coronavirus-themed scam? If so, let us know by reaching out on Twitter.
Check out our other COVID-19 scam roundups below!
- COVID-19 Scam Roundup – May 11, 2020
- COVID-19 Scam Roundup – May 4, 2020
- COVID-19 Scam Roundup – April 27, 2020
- COVID-19 Scam Roundup – April 20, 2020
- COVID-19 Scam Roundup – April 14, 2020
- COVID-19 Scam Roundup – April 6, 2020
- COVID-19 Scam Roundup – March 30, 2020
- COVID-19 Scam Roundup – Week of 3/16/20

