
Digital fraudsters have seized upon coronavirus 2019 (COVID-19) as a lure for their new scams and attack campaigns. Together, these malicious operations constitute nothing short of a deluge. Barracuda revealed that it spotted 9,116 coronavirus-themed spear-phishing emails between March 1 and March 23, 2020—a 667% increase over the 1,188 attacks detected a month earlier. By comparison, the security firm spotted just 137 coronavirus-themed email campaigns in January. Unfortunately, nefarious individuals show no sign of cooling it with their coronavirus-themed scams. All of us therefore need to stay on top of these ploys, including but not limited to those borne by email. With that in mind, let's look at some of the latest COVID-19 ruses that made headlines.
Texts Demand You Take a "Mandatory" Online COVID-19 Test
The Better Business Bureau (BBB) received reports of individuals posing as employees of the U.S. Department of Health and Human Services (HHS) or another U.S. government department. Using SMS text messages, these malicious actors instructed recipients to click on a link for the purpose of completing a "mandatory online COVID-19 test." There's just one problem: there's no way of testing someone for COVID-19 online. With that said, the link used in this scam likely directed recipients to a fake web portal designed to steal their personal, financial and/or medical information. Attackers could have then monetized that data on the dark web or leveraged it to conduct secondary attacks.
You're Infected...by Malicious Macros
Not dissimilar from the ploy described above, a scam detected by KnowBe4 used attack emails to warn recipients that they had come into contact with a "colleague/friend/family member" who has COVID-19. The email then instructed them to download and print an Excel spreadsheet so that they could bring it with them to the nearest coronavirus testing site.
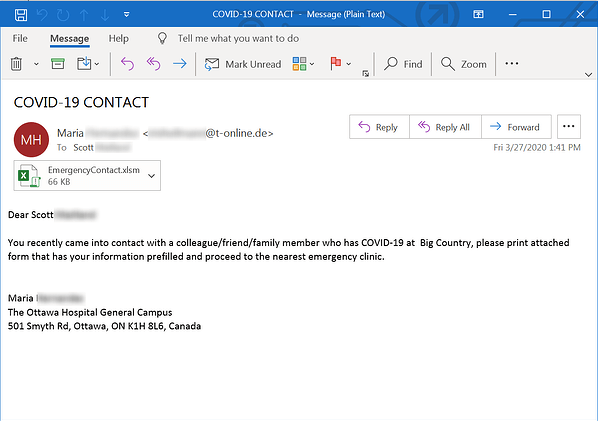
A screenshot of one of the attack emails (Source: KnowBe4) It's no surprise here that the Excel spreadsheet, named "EmergencyContact.xlsm," did not have recipients' data prefilled like the email said it would. Instead, the document informed users that they needed to enable content in order to view the spreadsheet's details. When they complied, users unknowingly activated the document's malicious macros and allowed this code to infect their machines with a trojan downloader.
Remcos RAT Masquerades as U.S. Small Business Association
Researchers at IBM X-Force recently detected an attack campaign that sent out emails disguised as official correspondence from the U.S. Small Business Association (SBA). The emails claimed to provide recipients with an application number with which they could apply for a "small business disaster assistance grant." All they needed to do was to sign an attached document allegedly authorizing a request for a tax return transcript and to upload it on SBA's website, the scammers told their recipients.
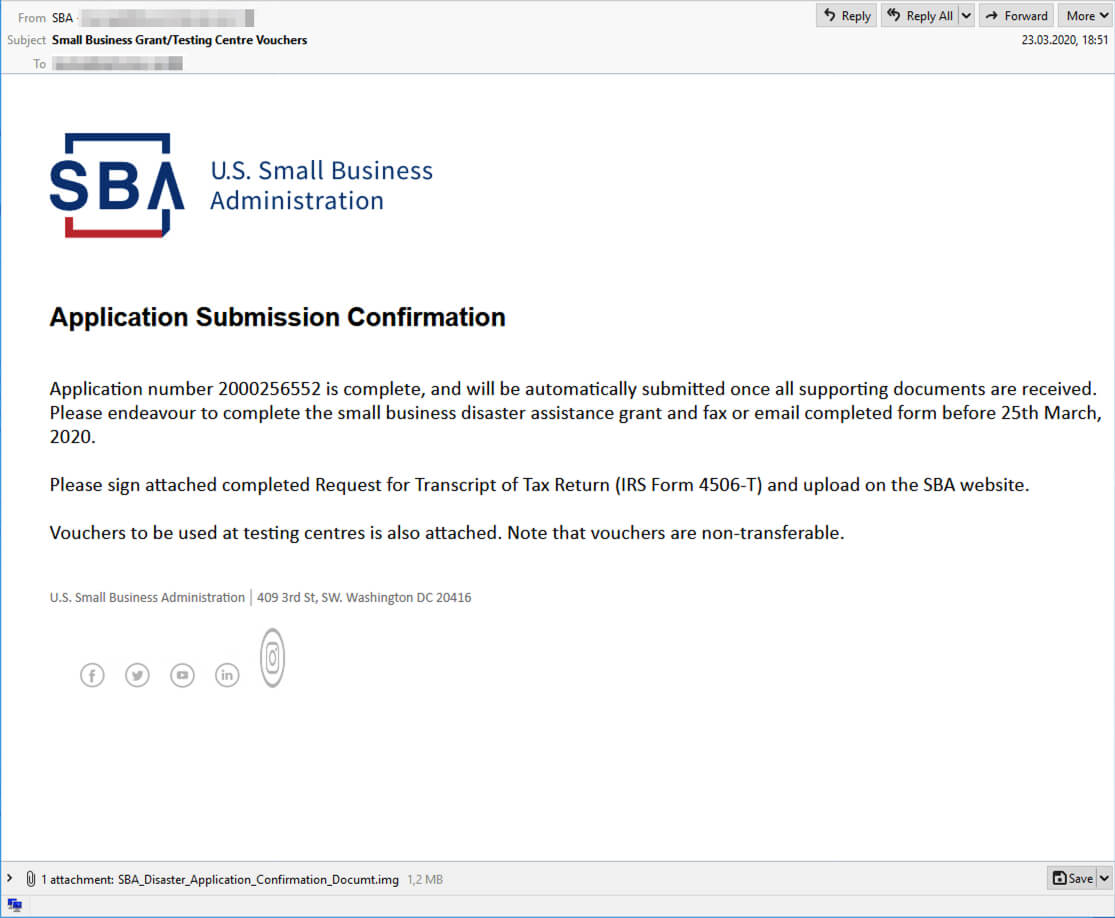
An attack email disguised as a message from SBA. (Source: IBM X-Force) Of particular note to IBM X-Force was the fact that the application process described in the attack email followed the same sequence that's actually employed by the SBA. It's therefore particularly insidious that the attachment did not further recipients' requests for small business assistance. Instead, it downloaded a sample of the Remcos remote access trojan (RAT) family.
Zeus Sphinx Reawakens with COVID-19 Maldoc Campaign
Remcos wasn't the only trojan that attracted IBM's attention by abusing COVID-19 as a lure. On the contrary, researchers at X-Force detected another campaign whose attack emails informed recipients that Canadian Prime Minister Justin Trudeau had decided to award each Canadian who chose to stay home as a result of the coronavirus with a check of $2,500 CAD. The emails then told recipients that they could apply for one of these checks by filling out a request form.
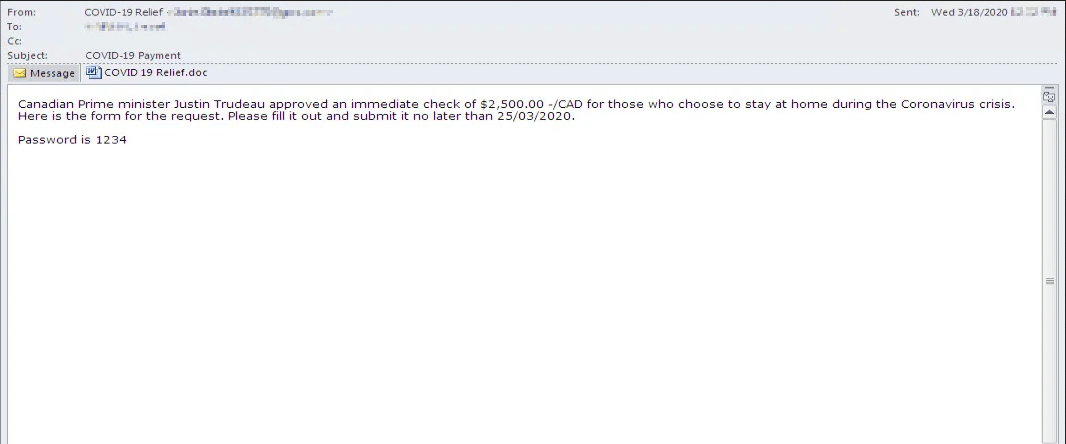
Malspam delivering a Zeus Sphinx infection (Source: IBM X-Force) Once they opened the protected file with a password provided in the email, the document asked recipients to enable content. Users who complied activated macro code that infected their computers with Zeus Sphinx, a malware family which has otherwise laid dormant for three years. Upon establishing persistence, Sphinx used web injections to target major banks located in the United States and Canada.
Coronavirus-Themed Wiper Overwrites a Victim's MBR
Not all coronavirus-themed attack campaigns are interested in stealing their victims' information. Some just want to make sure that their victims can't access their information going forward. And what better way is there to do that than to overwrite a victim device's master boot record (MBR), information which is essential for a device to locate and therefore boot an operating system?
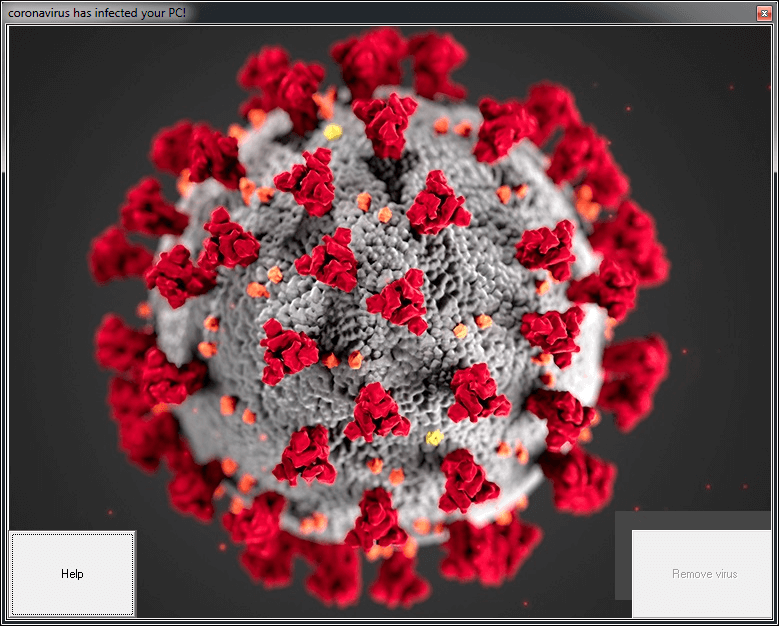
The infection screen for coronavirus.bat. (Source: SonicWall) Such was the case with "coronavirus.bat," a file discovered by SonicWall which identified itself as a coronavirus installer. This file disabled Windows Task Manager, User Access Control (UAC), and options for adding/modifying the desktop. It then informed its victims that "coronavirus" had successfully installed itself on their computers and that their computer would restart. Upon reboot, the malware ran "mainWindow.exe." This executable loaded a binary responsible for overwriting the MBR.
Fraudsters Using Fake Pop-up Testing Sites for Medicare Fraud
Last but not least in this week's roundup, we have a truly reprehensible scam. WDRB learned that fraudsters are creating pop-up testing sites for COVID-19. Here's an image of one that appeared at the corner on 17th and Broadway in Louisville, Kentucky.

One of the fake pop-up testing sites in Louisville, Kentucky. (Source: WDRB) Dressed in personal protective equipment, the fraudsters told passersby that they could test whether they were infected with COVID-19 for a fee of $240. They then used the same gloves to "examine" all of their patients. At best, they rendered no healthcare service; they made off with their victims' money and stole their personal information in order to make fraudulent Medicare and Medicaid claims. At worst, they possibly exposed their victims to the coronavirus by not disposing of their medical gear in between examinations of their patients. Have you seen a coronavirus-themed scam? If so, let us know by reaching out on Twitter.
Check out our other COVID-19 scam roundups below!
- COVID-19 Scam Roundup – May 11, 2020
- COVID-19 Scam Roundup – May 4, 2020
- COVID-19 Scam Roundup – April 27, 2020
- COVID-19 Scam Roundup – April 20, 2020
- COVID-19 Scam Roundup – April 14, 2020
- COVID-19 Scam Roundup – April 6, 2020
- COVID-19 Scam Roundup – March 30, 2020
- COVID-19 Scam Roundup – Week of 3/16/20

