
Digital attacks continue to exploit coronavirus 2019 (COVID-19) as part of their malicious operations. On May 5, 2020, the U.S. Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA) along with the United Kingdom's National Cyber Security Centre (NCSC) published a joint alert in which they revealed that they had witnessed APT actors targeting local governments, academia and pharmaceutical companies. Investigators determined that these nefarious individuals were intent on stealing research data into a vaccine along with intellectual property for "commercial and state benefit." Digital attackers aren't just targeting research organizations and medical entities. They're also going after users and organizations of all shapes and sizes. With that said, it's important to stay on top of the latest COVID-19 ruses circulating in the wild. Here are some of the most recent ploys that have made headlines.
Fake COVID-19 Credit Union Profiles Popping Up on Instagram
The PhishLabs team revealed to Security Boulevard that digital fraudsters are impersonating credit unions on Instagram. To pull this off, malicious actors began creating fake profiles that contain financial institutions' names, logos and links to their websites along with mentions of COVID-19. They then started using those accounts to DM followers and to inform them that they had been selected for a cash prize.
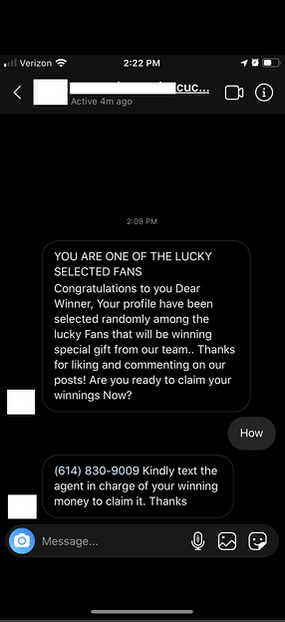
An example of a DM from a fake COVID-19 credit union profile (Source: Security Boulevard) The messages instructed users to send a text to a number so that an agent could help them claim the money. In reality, threat actors leveraged that number to convince users to hand over their account credentials. They then abused that information to compromise their victims' banking accounts.
Work-from-Home Offers Used to Conceal Money Mule Scams
That wasn't the only piece of research from PhishLabs this past week. In a blog post published on the security firm's website, researchers revealed that they had come across attack emails from a spray-and-pray campaign that had attempted to entice people laid off as a result of the pandemic with work-from-home opportunities. One email offered recipients as much as $5,000 a week for a fabricated position.
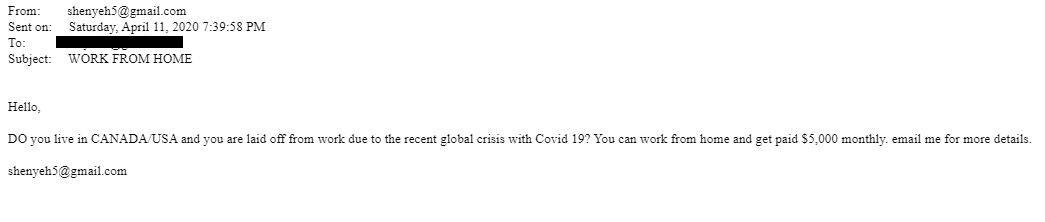
Sample work-from-home scam (Source: PhishLabs) Sounds too good to be true, doesn't it? That's because it is. Indeed, whenever someone consented to these "job terms," malicious actors enlisted them into a money mule scam. These ruses cause financial hardship; they don't alleviate it. For instance, in the event that recipients hand over their banking information to their "employers," nefarious individuals might misuse that data to steal from their accounts. Banks might also hold users liable for depositing stolen money into their accounts.
Remcos Engaging in All Kinds of Coronavirus-Themed Attacks
Microsoft Security Intelligence took to Twitter to announce that the digital attackers had been using numerous attack campaigns with COVID-19 lures to distribute Remcos RAT. In one example, researchers revealed that malicious actors had impersonated the Center for Disease Prevention and Control (CDC) Health Alert Network to target South Korean manufacturing firms. These emails claimed to offer recipients updates about "safety measures and existing cases in [their] city," but in reality, they leveraged a .ISO file to drop Remcos as their payload. https://twitter.com/MsftSecIntel/status/1257324139515269121 In another campaign detected by nefarious individuals, digital attackers impersonated the American Institute of CPAs and claimed to be delivering "COVID-19 related updates" to its members. Those emails arrived with a .ZIP archive that delivered the trojan.
Medical Suppliers Targeted by Agent Tesla Operations
Researchers at FortiGuard Labs came across an attack campaign that targeted a medical device supplier. Those responsible for the operation claimed that they had tried calling earlier about purchasing a "quite bulky list of pharmaceuticals and medical devices" for the purpose of assisting with the COVID-19 response. They said that no one had picked up the phone, so they indicated that they had sent over an attachment allegedly containing information about their company.
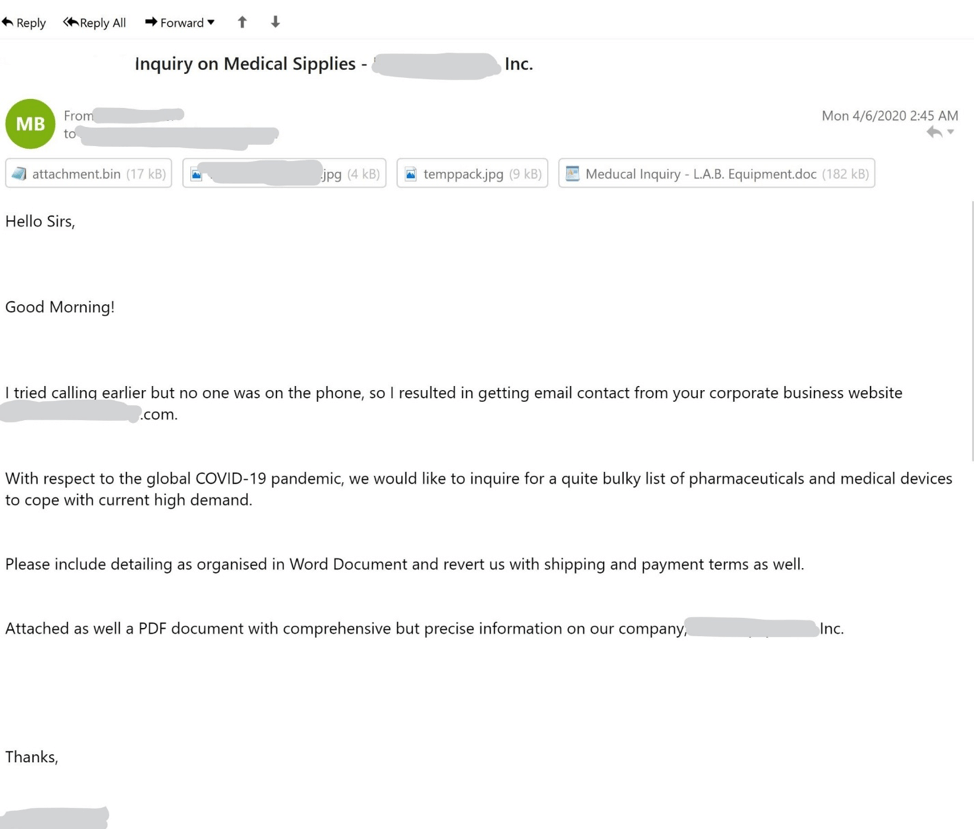
The fake email sent to the medical "sipplies" provider (Source: Fortinet) Of course, that attachment was a fake. The malicious Word document leveraged CVE-2017-11882 to download a file from a predefined URL. This file turned out to be a sample of Agent Tesla, a well-known infostealer family.
Fake IRS Pages Designed to Help Steal Users' Stimulus Checks
In the last ploy of our week, researchers at SecureWorks witnessed nefarious individuals targeting users with phishing pages designed to look like tax forms employed by the U.S. Internal Revenue Service.
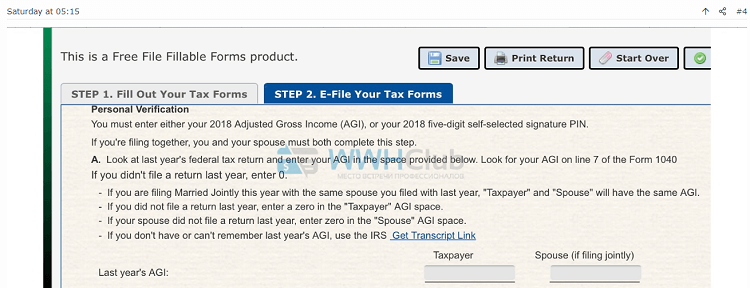
Phishing page to collect victims’ tax information. (Source: Secureworks) Likely distributed via attack emails and other means, these phishing pages had a simple purpose: steal users' tax information. They then leveraged that data to impersonate victims on official IRS tax forms so that they could collect both their tax returns and their stimulus checks. Have you seen a coronavirus-themed scam? If so, let us know by reaching out on Twitter.
Check out our other COVID-19 scam roundups below!
- COVID-19 Scam Roundup – May 11, 2020
- COVID-19 Scam Roundup – May 4, 2020
- COVID-19 Scam Roundup – April 27, 2020
- COVID-19 Scam Roundup – April 20, 2020
- COVID-19 Scam Roundup – April 14, 2020
- COVID-19 Scam Roundup – April 6, 2020
- COVID-19 Scam Roundup – March 30, 2020
- COVID-19 Scam Roundup – Week of 3/16/20

