
Malicious actors continue to abuse coronavirus 2019 (COVID-19) as a lure to profit off of innocent people. Indeed, Arkose Labs found that 26.5% of all transactions recorded in Q1 2020 were fraud and abuse attempts—a 20% increase over the previous quarter and the highest attack rate ever observed by the security firm's researchers. It's therefore unsurprising that we've seen the U.S. Department of Homeland Security launch "Operation Stolen Promise" and other initiatives in an attempt to combat these growing numbers of fraud attempts. While law enforcement officials work to take down these fraudsters, you as a user can leverage your awareness of the latest COVID-19 scams to not only protect yourself but to also safeguard others by reporting new ploys to the authorities. Here are some of the latest ruses for which you should be watchful.
No, Washing Your Driveway WON'T Protect You Against COVID-19
As reported by NorthWalesLive, the North Wales Police (NWP) Flintshire learned that fraudsters had been going around to elderly residents and asking if them if they would like to pay to have their driveways cleaned. Their hook? They claimed that a clean driveway could protect them against COVID-19. Yeah...no. NWP Flintshire said it this way:
We have had numerous reports today of elderly and vulnerable people being pressured to have their driveways washed and disinfected. They’re claiming that it protects against the COVID-19 virus. To be clear, this is nonsense.
As of this writing, local authorities had stopped several suspects while on patrol, but they were still in search of a suspicious white Transit tipper.
Anubis Trojan Disguised as Coronavirus Tracking Map
In a video posted on YouTube, ESET security researcher Lukas Stefanko shared that an attack campaign targeting Italian users. The operation began with a malicious website that informed visitors they could install a COVID-19 map app from Google's Play Store by clicking an embedded ad. Those who complied did not download an app from the Play Store, however; the app loaded directly from the site. Once opened, the app immediately raised suspicions with its installation of 20 GB worth of data. The app then asked the user to enable Accessibility Services. Upon being granted these privileges, the app turned off Google's Play Protect security mechanism and secretly contacted its command-and-control (C&C) server to send over some device information. This means of infection gave the campaign all it needed to run Anubis, a banking trojan which stole users' information. You can view the infection chain described above in Stefanko's video below: https://youtu.be/U0UsfO-0uJM
Update Your Shipment Details or Don't Get Your Package!
Kaspersky Lab came across a spam campaign informing the recipient that a delivery attempt had failed because their shipment details were incorrect. The message subsequently urged the recipient to provide their updated details so that they could receive their package "before government lock down, prior to the Coronavirus pandemic precautionary major."
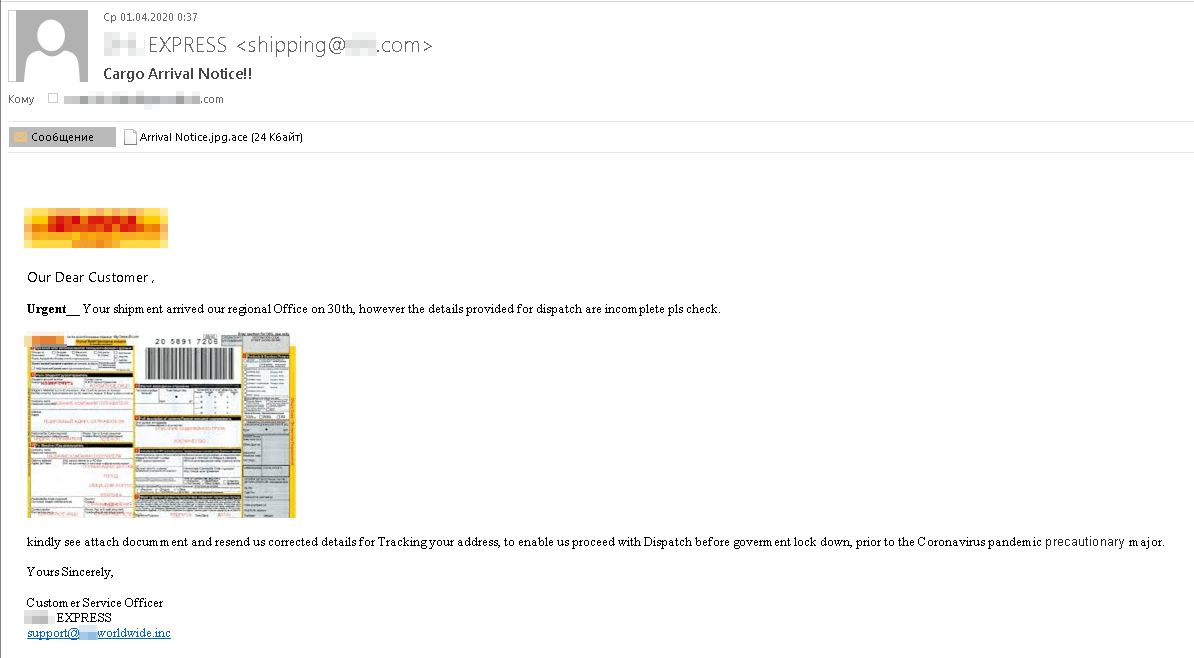
Coronavirus-themed shipment spam message (Source: Kaspersky) As it turns out, those responsible for the COVID-19 spam campaign weren't interested in stealing the recipient's information. Instead, they embedded a small image of what appeared to be a receipt. It was too small to read, however—a clever technique to trick the recipient into clicking on the attachment to view the "receipt." This file turned out to be an executable ACE archive that loaded the Noon spyware.
Donations to COVID-19 Fight Sought by WHO Posers
In this scam email shared with Tripwire, malicious actors sent out attack emails urging recipients to consider donating to the World Health Organization (WHO). With a sender address of "[email protected]," the emails explained that any and all donations would "support WHO's work, including with partners, to track and understand the spread of the virus; to ensure patients get the care they need and front line workers get essential supplies and information; and to accelerate research and development of a vaccine and treatments for all who need them." Given these benefits, the messages instructed recipients to click on an embedded "Help Us Fight" button. https://twitter.com/davidrfindlay/status/1256108435147493376 The World Health Organization is indeed seeking donations to support its fight against COVID-19. But it's hosting its own donation form on its official website here. By contrast, the attack emails discussed above direct recipients to visit the malicious domain "help-who[.]com" so that attackers can use an unsecured form to steal individuals' payment card details.
A Pitiful Pandemic Puppy Ploy
According to CBS19, the Better Business Bureau learned of an instance in which an elderly couple wanted to adopt a Shih Tzu puppy off Craigslist. Myla Blum, in her 70s, and Norman Blum, 84, were looking for a puppy because their other dog was getting old. They were having trouble finding a puppy when they found an Craigslist ad from someone who claimed that their child had died and that their landlord wouldn't allow them to keep the puppies. They were offering the puppies for $350 including shipping. It wasn't too long before the person who claimed to have the puppies started acting strangely, however. They insisted that all communication be conducted through text, and they wanted half of the money to be sent upfront. After the individual behind the ad refused to let someone come see the puppies, CBS19 searched the individual's phone number on Google and found that it registered a hit for "pet scams."
Seeking Help with the FMLA? Don't Click This Email!
IBM X-Force came across the last scam operation included in this week's roundup. The campaign consisted of attack emails that appeared to originate from the U.S. Department of Labor. Those emails claimed that the Department of Labor had made changes to the "Family and Medical Leave of Act" as a result of COVID-19. Subsequently, it instructed them to review the changes made to the Act by opening an attached Word document.
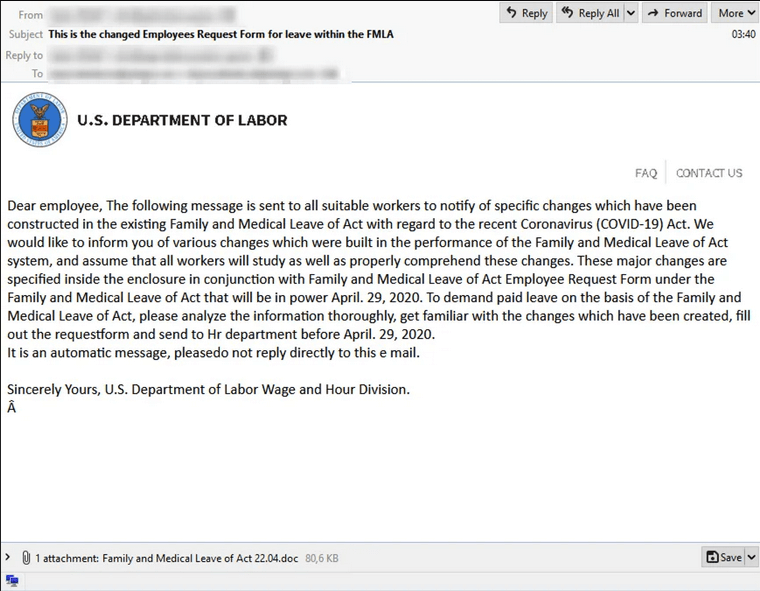
The fake FMLA email (Source: IBM X-Force) But the email didn't contain any information about the legitimate Family and Medical Leave Act. Instead, it installed Trickbot for the purpose of enlisting victims' devices into a botnet. Have you seen a coronavirus-themed scam? If so, let us know by reaching out on Twitter.
Check out our other COVID-19 scam roundups below!
- COVID-19 Scam Roundup – May 11, 2020
- COVID-19 Scam Roundup – May 4, 2020
- COVID-19 Scam Roundup – April 27, 2020
- COVID-19 Scam Roundup – April 20, 2020
- COVID-19 Scam Roundup – April 14, 2020
- COVID-19 Scam Roundup – April 6, 2020
- COVID-19 Scam Roundup – March 30, 2020
- COVID-19 Scam Roundup – Week of 3/16/20

