
Many in the digital security community are coming together to combat malicious actors during the coronavirus disease 2019 (COVID-19) global outbreak. One of the most visible of these new efforts is the COVID-19 CTI League. Made up of approximately 400 volunteers living in approximately 40 countries, the COVID-19 CTI League is working to block attackers from health care organizations and other medical facilities at this juncture. Reuters reports that the threat intelligence collective is also looking to preventing lowly phishers and fraudsters from capitalizing on people's fears surrounding the outbreak. It's not an easy fight. New coronavirus-themed phishing attacks and scams spring up daily. But raising awareness is key. Towards that end, let's discuss some of the scams that made headlines this week.
BlackNET Distributed by Fake "Corona AV"
Digital fraudsters revealed their true colors in the first scam in this week's roundup. Detected by Malwarebytes, the ruse began when spam campaigns tricked users into visiting a website entitled "Corona Antivirus -World’s best protection." Yes, the malicious actors would have had you actually believe that antivirus could protect you against COVID-19!
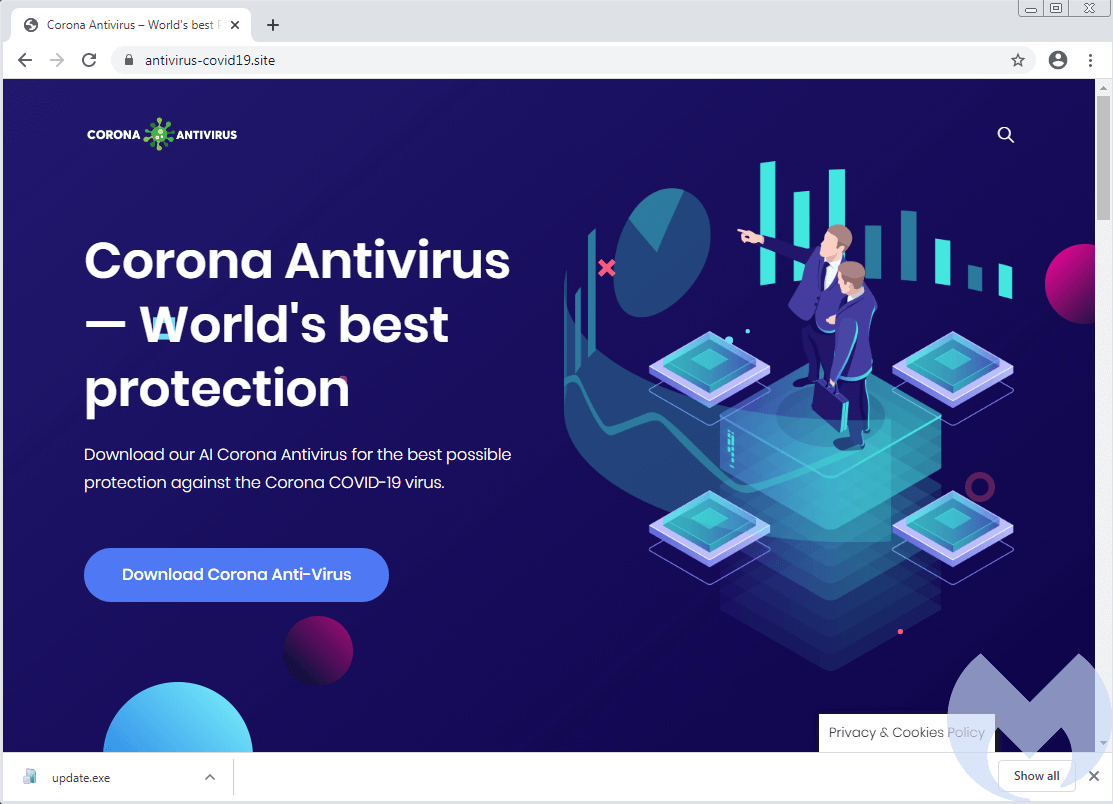
A screenshot of "Corona Antivirus -World’s best protection." (Source: Malwarebytes) The nonsense didn't end there. As the website went on to add:
Our scientists from Harvard University have been working on a special AI development to combat the virus using a windows app. Your PC actively protects you against the Coronaviruses (Cov) while the app is running.
In the event someone actually fell for this ploy and installed the program on their computer, the fake app infected the device and enslaved it as a bot for the BlackNET botnet.
Free Passes to Netflix? They're Fake!
Apparently, malicious actors figured they'd capitalize on current social distancing recommendations and self-isolation orders by spreading around fake offers of free Netflix subscriptions.
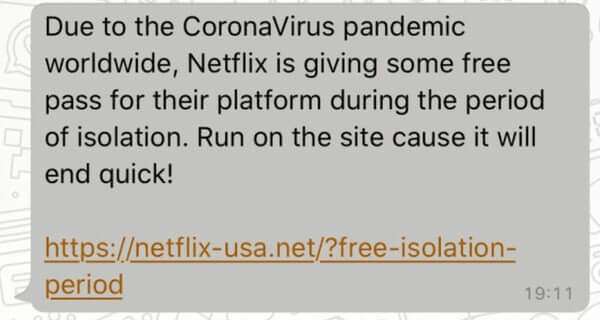
One of the fake Netflix passes. (Source: Bitdefender) As you can see in the image shared above, the link did not lead users to the legitimate Netflix domain "netflix.com" Instead, it pointed them to a lookalike site hosted at "netflix-usa[dot]net." That site asked visitors to answer some questions about how they were handling the global pandemic. It then asked them to share the site with 10 of their friends. Bitdefender reasoned that the site did this for the purpose of tricking even more individuals into sharing their personal information with the attackers.
"Coronavirus Finder" – Ginp's Trick of Stealing CC Data
Kaspersky Lab spotted a new attack campaign involving the Ginp banking trojan. Upon receiving a special command, Ginp redirected users to a web page advertising a program called the "Coronavirus Finder." The website claimed that users could reveal the number of people infected with COVID-19 near them in exchange for a small fee.
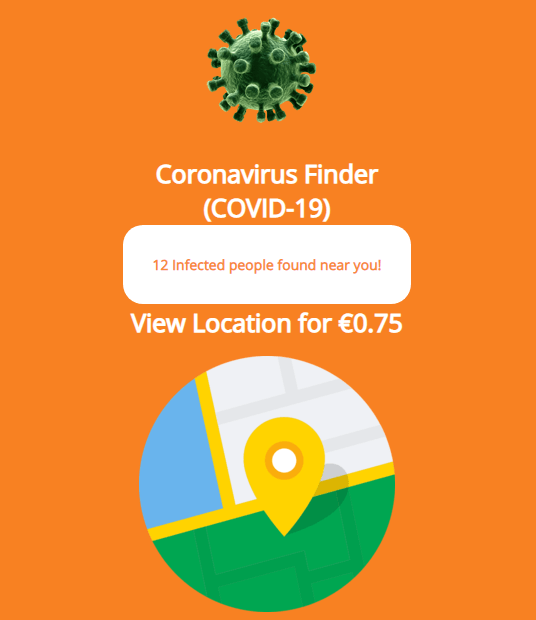
Coronavirus Finder (Source: Kaspersky Lab) Not surprisingly, the program was a fake. It was simply a trick to convince visitors into submitting their credit card information. They didn't even charge the small fee advertised on the web page! Why? Probably because they were thinking of other ways they could abuse the victim's credit card data on a larger scale.
Promise of COVID-19 Safety Mask Gives Way to...Nothing?
Upon visiting the site hxxp://coronasafetymask[.]tk, researchers at ZScaler found a message informing users that they would receive a "Corona safety mask" if they agreed to download an app.
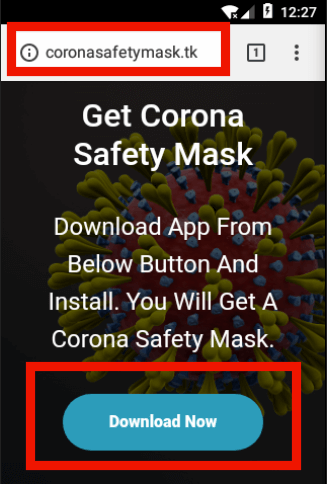
Scam webpage (Source: ZScaler) The app immediately demanded the right to read contacts and send SMS messages once it had finished loading on a victim's device. It then asked the user to click on a button that supposedly redirected them to a portal where they could enter their information for the purpose of procuring a mask. Nothing happened once they clicked the button, but it's possible that after further development, the portal could ask users to "pay" for a mask by entering in their credit card information. That being said, the app did leverage its "read contacts" permission to collect all of a victim's contacts and send out SMS messages that spread the scam even further.
Fake Goodwill Payments from UK Government
Scammers know that many individuals and businesses are in desperate need of economic assistance as a result of their ongoing self-distancing orders. Cruelly, these attackers are capitalizing on this hardship to steal even more from those who are already suffering. In a scam shared by the Dorchester Police, for instance, nefarious individuals sent out text messages informing people that Her Majesty's Revenue and Customers (HMRC) had decided to offer them with a "goodwill payment" in the amount of £258.
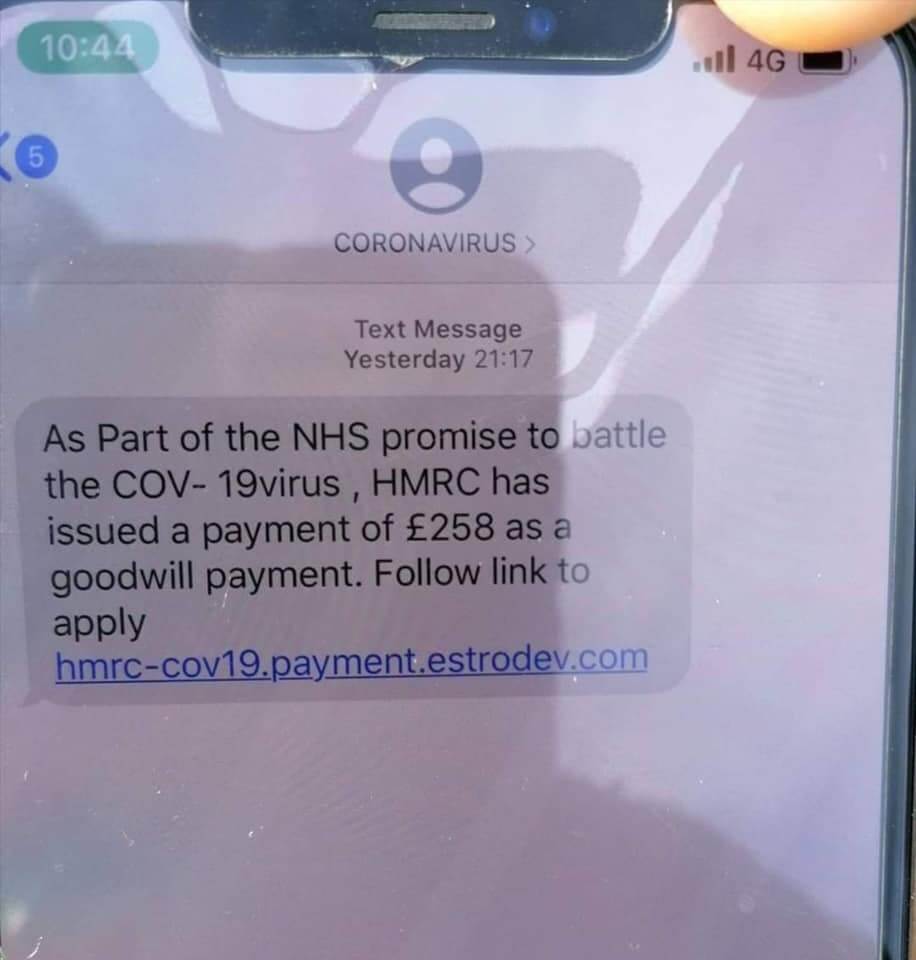
A screenshot of the scam SMS message. (Source: Facebook) The links redirected users to a page that asked them to verify their card details so that the UK government could presumably transfer over the money. Needless to say, those behind this attack likely monetized those details on the dark web or used them to conduct credit card fraud.
Fill out a 'Census Form' to Receive Your Stimulus Check
Along the same lines as the previous scam, WOIO learned of a ploy in which a family member sent a strange Facebook message to one Joshua Wilson in northeast Ohio.
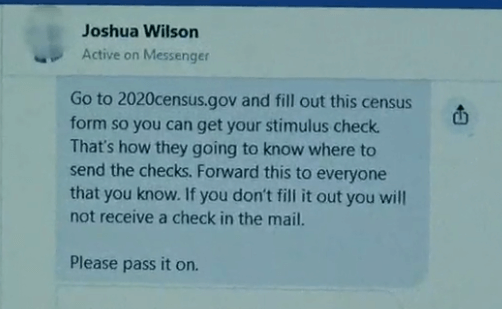
A screenshot of the Facebook message sent to Joshua Wilson. (Source: WOIO) The message informed Wilson that he would not receive his COVID-19 stimulus check from the U.S. government unless he completed his census form. There's just one problem: the census has nothing to do with the stimulus plan. No doubt malicious attackers are using compromised Facebook accounts to try to trick people into providing their personal and/or financial information.
Bank Details in Exchange for Free Meals to Your Kids
The UK government's Department for Education (DfE) issued an alert about a new scam targeting parents. The ploy message read as follows:
As schools will be closing, if you’re entitled to free school meals, please send your bank details and we’ll make sure you’re supported.
DfE confirmed on its website that the emails were illegitimate. It went on to urge recipients to delete the emails from their inboxes and to not respond.
Fines for Breaking Your COVID-19 Quarantine
Finally, as reported by Burien News, the Burien Police Department learned that someone had decided to begin calling Burien residents. These individuals informed their victims that police had a warrant for their arrest because they had allegedly violated their quarantine. They then instructed them to provide their banking information over the phone for the purpose of paying their fines. Of course, no such arrest warrant or fines actually existed. Have you seen a coronavirus-themed scam? If so, let us know by reaching out on Twitter.
Check out our other COVID-19 scam roundups below!
- COVID-19 Scam Roundup – May 11, 2020
- COVID-19 Scam Roundup – May 4, 2020
- COVID-19 Scam Roundup – April 27, 2020
- COVID-19 Scam Roundup – April 20, 2020
- COVID-19 Scam Roundup – April 14, 2020
- COVID-19 Scam Roundup – April 6, 2020
- COVID-19 Scam Roundup – March 30, 2020
- COVID-19 Scam Roundup – Week of 3/16/20
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

