
In recent years, Wi-Fi networks are usually secured with the Wi-Fi Protected Access II (WPA2), a security protocol which leverages a strong cryptographic hash function (PBKDF2 with the network's ESSID as salt) to protect the pre-shared key (PSK). Breaking into a WPA-2 network can be a great challenge during a penetration test. A modern GPU that is able to calculate an average of 80000 hashes per second will need up to 30 days to break an 8-character PSK. In these cases, a Wi-Fi phishing attack comes in handy. Wi-Fi phishing consists of two steps. The first step involves the process of associating with Wi-Fi clients unknowingly (e.g. KARMA / Evil Twin techniques), while the second step involves presenting to the victim user a familiar authentication interface. Making the authentication interface look legitimate will greatly increase the success rate of the attack. In this respect, the interface should be generated on the basis of something that is appropriate for a certain user (e.g. an interface that is similar to the one used by the legitimate Access Point (AP)). This, of course, involves gathering information from the target environment and victim user. Even with no knowledge of the technologies or services used by the user, it is possible to collect the required information from:
- Beacon frame (physical layer): One of the management frames in IEEE 802.11 that is transmitted periodically by the AP. It contains all the information about the network, such as i) the ESSID, ii) the encryption type, and iii) the BSSID (MAC address) of the AP.
- User-Agent header (application layer): An HTTP header that contains a characteristic string with details regarding the network peer. By redirecting the victim's HTTP requests to a website controlled by us, we are able to retrieve useful information from this header, such as i) the web browser and ii) the operating system of the victim.
The interesting thing about the BSSID (found in the beacon frame) is that it can be used to determine the router manufacturer. For example, if the first digits of the MAC address are "00:12:17", we can be pretty confident that the beacon frame was broadcasted by a Linksys router. By knowing the router manufacturer, we can craft fake router configuration pages accordingly as illustrated in the image below.
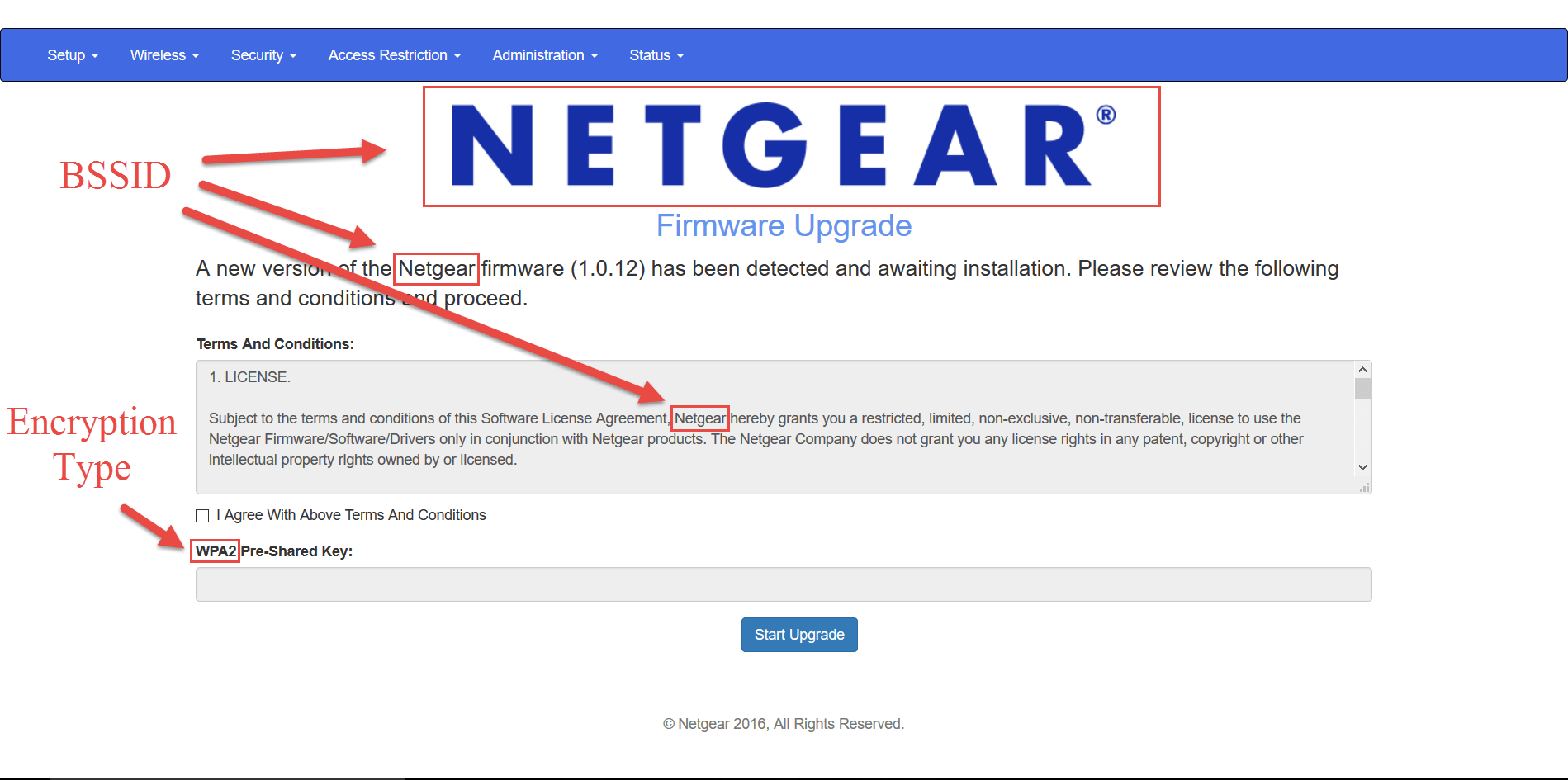
In this image, both the BSSID of the victim's AP and the encryption type of the target network are used to craft a victim-customized phishing page asking for the PSK. This trick became quite popular in the past few years, surpassing the traditional brute-forcing of the 4-way handshake. However, this attack raises suspicion and advanced users will hardly fall for this. But look at the following image.
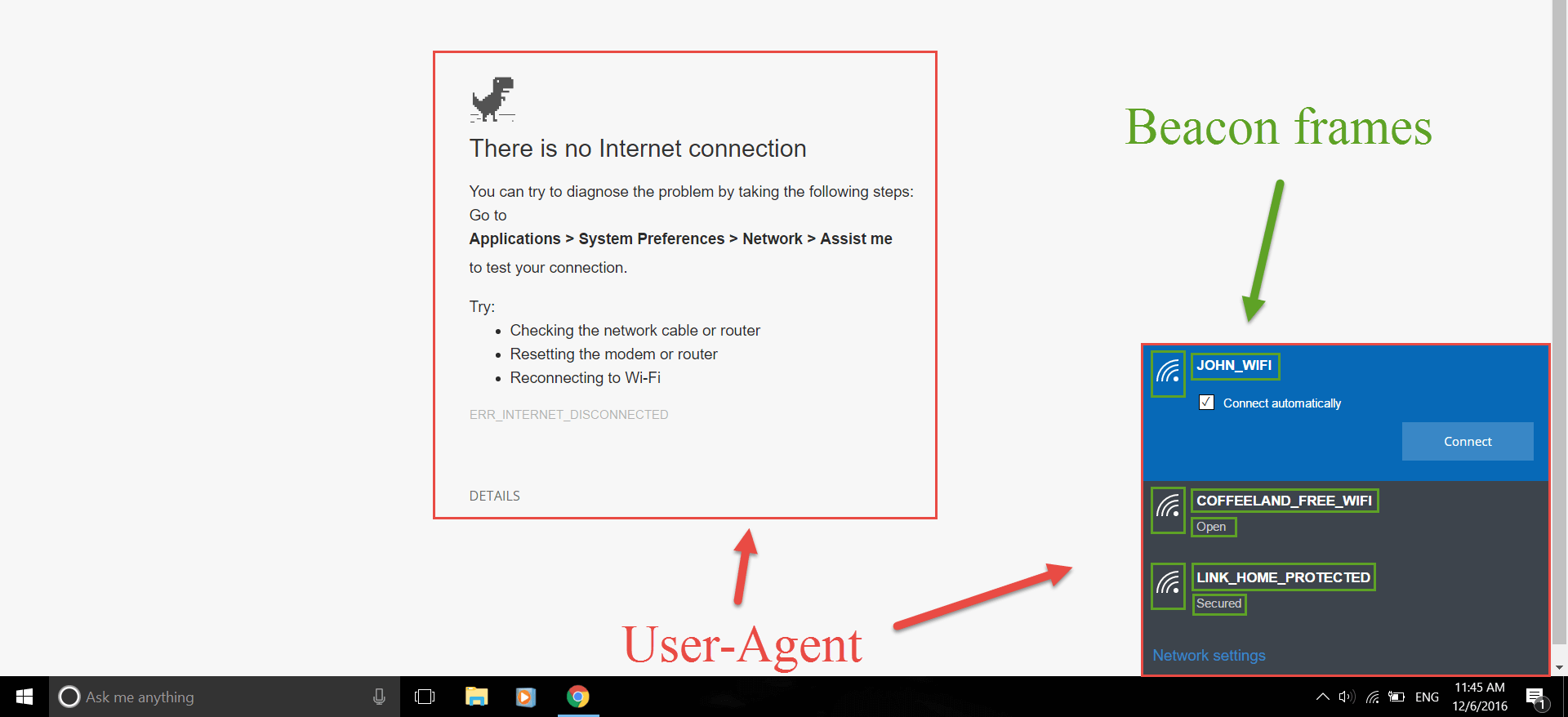
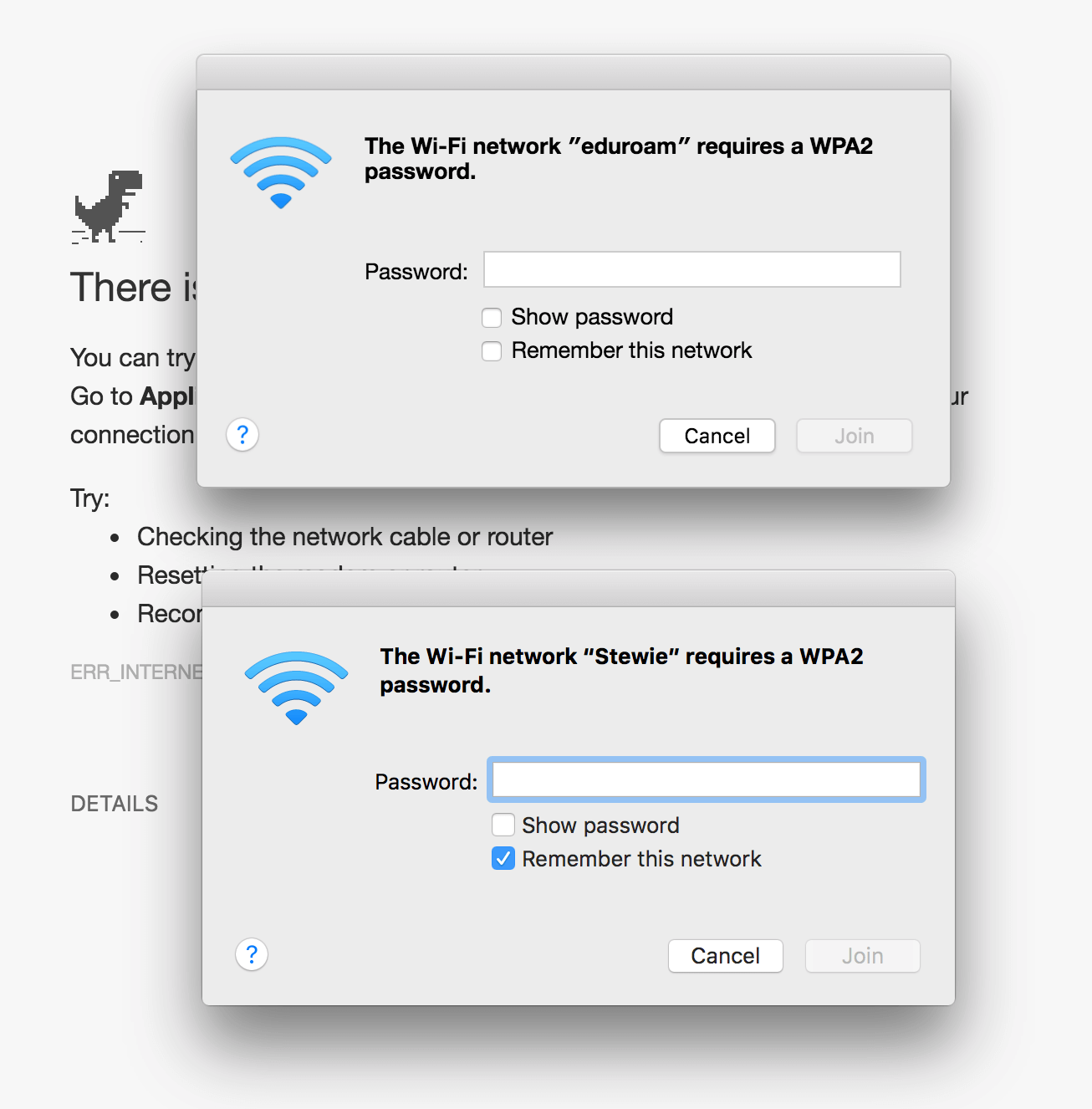
In this phishing attack, we first make the victim believe he is not having any connectivity to the Internet by showing the "No Internet Connection" page in his browser. We display Google Chrome's "Unable to Connect to the Internet" page because the HTTP User-Agent header assured us that the victim is using that specific browser. The same header told us that the victim is running Windows, giving us the chance to display a web-based imitation of Windows network manager. We make this much more realistic by showing the valid networks that are in the victim's neighborhood. In this case, the victim can hardly tell if the network manager is part of the Operating System UI or the web page he is visiting. In the following image, we compare the Mac OS network manager with an HTML-lookalike of ours. At the top is the fake network manager while the one displayed at the bottom is the real one.
Phishing attacks like the above can be performed using the latest version of Wifiphisher (v1.2) that was released a month ago. Wifiphisher is an open-source project, and all this functionality wouldn't be possible without the contributions of the community. Kudos to everyone that helped, especially to Stergios Kolios, Leonidas Vrachnis and Dionysis Zindros.
About the Author: George Chatzisofroniou (@_sophron) is a security engineer at CENSUS S.A. He has performed infrastructure and software security testing for clients around the world, including financial institutions, device & software vendors and telecommunications services providers. His research interests include cryptography, WiFi hacking, web security and network security. George is the lead developer of the popular open-source wireless hacking tool "Wifiphisher". Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Save
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

