
The Retail Cyber Intelligence Sharing Center (R-CISC) hosted its inaugural summit this April – an event which brought together more than 200 information security leaders from some of the region’s largest retail and consumer services organizations. Throughout the two-day event in the “Windy City,” industry experts shared insights, advice and lessons learned from tackling the cybersecurity issues affecting these sectors today. Speakers included representatives from several Fortune 500 organizations, such as AT&T, Google and Facebook, as well as a number of cybersecurity firms like Tripwire. If you missed the event, check out these eye-catching visualizations of some of the presentations created by talented graphic artist Kelly Kingman.
A Vision for the Future: How Retailers Will Shape the Industry
Participants: Colin Anderson; Ken Athanasiou; Bob Bragdon; Jim Cameli; Bill Dennings; Scott L. Howitt; Brad Maiorino; David McLeod; and Suzie Squier During the opening keynote, the R-CISC Board of Directors discussed why information sharing and collaboration is our best bet to secure the industry in the future. Bill Dennings, EVP, Chief Compliance, Risk & Security Officer at Uphold emphasized that "no one retailer looks alike." Organizations must get everyone to the table, he said, in order to build trust and adopt cross-sector information sharing, which will benefit us all.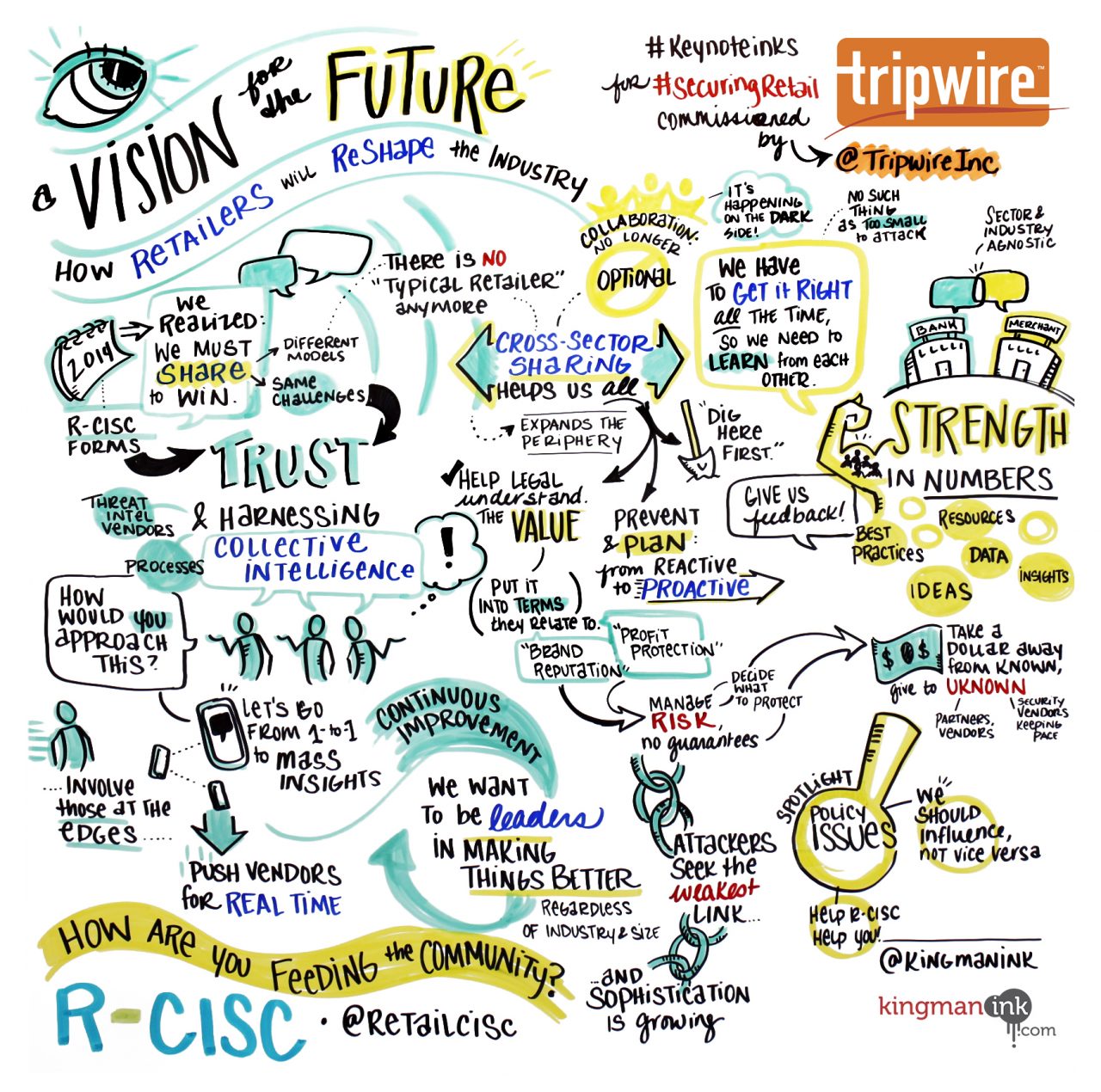
Becoming the Borg: Strategies for Collective Threat Defense
Participants: Daniel Conroy, CISO at Synchrony Financial; Bill Dennings, EVP, Chief Compliance, Risk & Security Officer at Uphold; David McLeod, CISO at JCPenney In one of the following sessions, Dennings further explored the concept of collaboration in a panel with Daniel Conroy, CISO for Synchrony Financial, and David McLeod, CISO of JCPenney. The trio discussed the topic of 'shared consciousness' – an approach that unites retailers and their key partners in a common purpose, strengthens security strategies and helps unmask threat actors.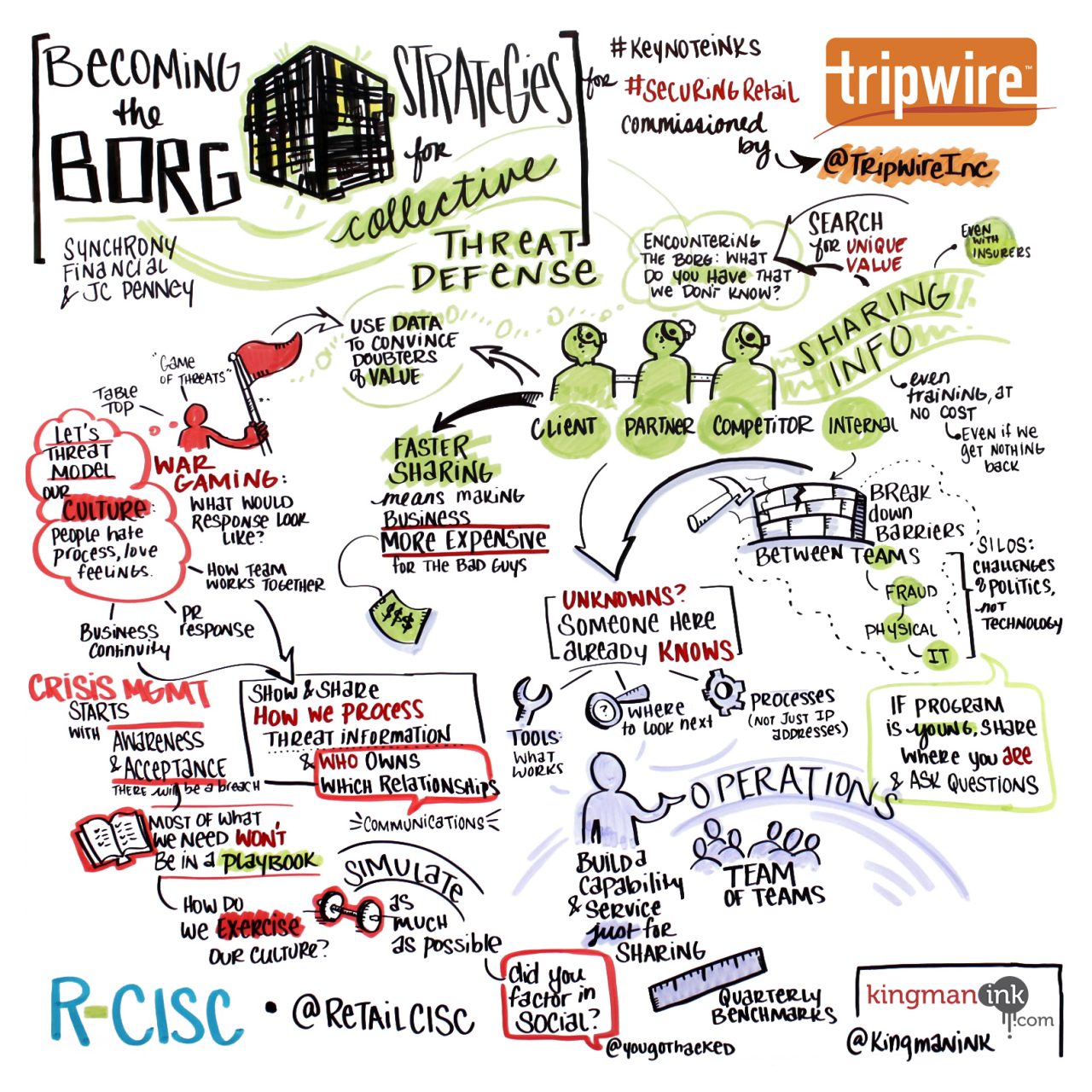
A Primer on Cyber Geopolitics for Retailers
Speaker: Norma Krayem, Senior Policy Advisor at Holland & Knight Cybersecurity has become a tangled web of global geopolitical risks, says Krayem. Meanwhile, retailers sit at the center as the principle target of adversaries, state and federal legislators, global regulators, etc. Krayem answered topical questions, such as what it takes for retail security leaders to manage new and emerging requirements from numerous diverse players, as well as the motivations behind each group.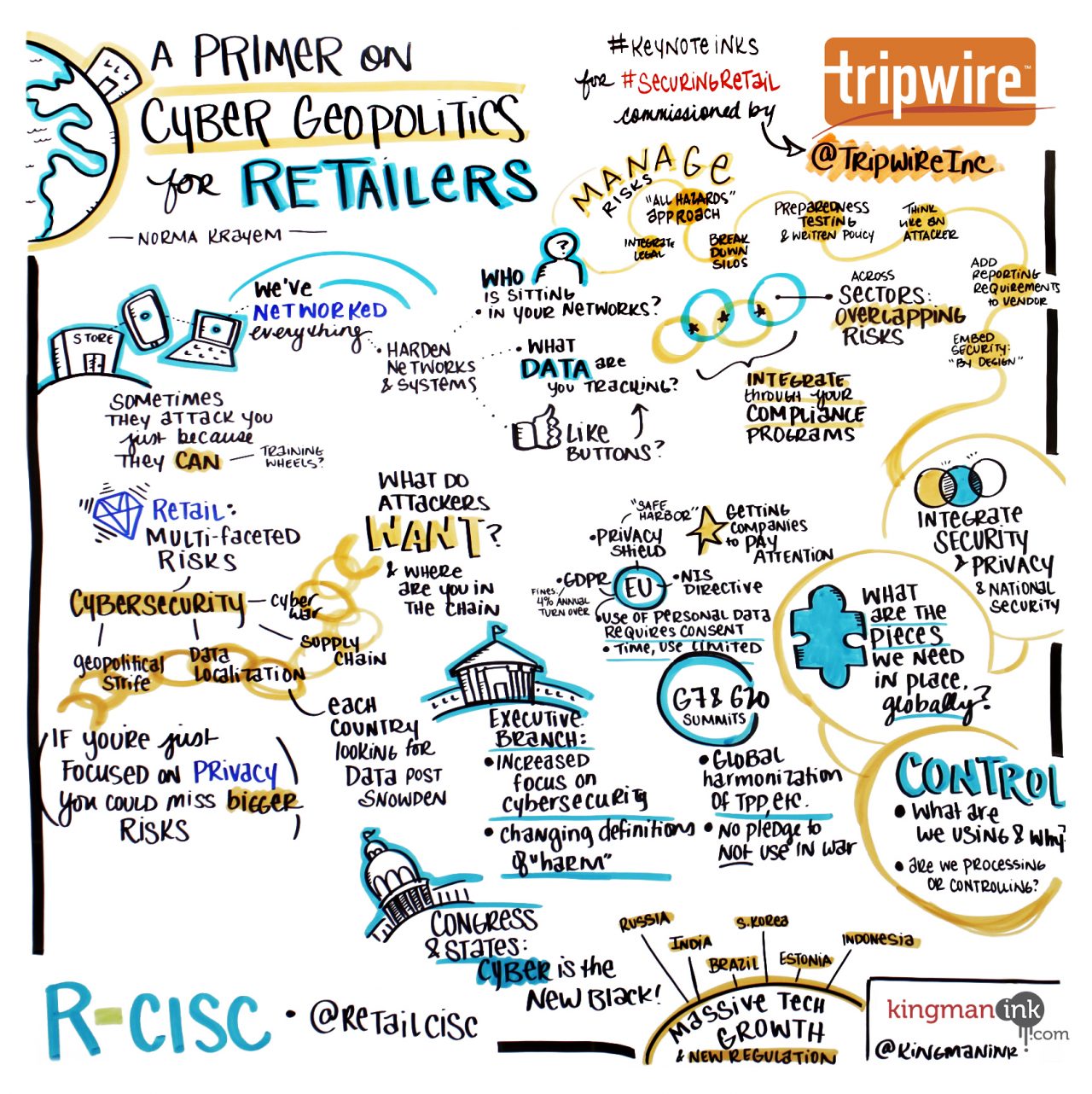
The IoT Challenge: Influence, Innovate, Secure
Speaker: Scott L. Howitt, CISO at MGM Resorts International Savvy new integrations hit the market daily. From environmental sensors to smart homes to iPad wine lists for the in-the-know aficionado. In this session, Howitt described how the Internet of Things (IoT) is changing the consumer landscape – retail being the new horizon. So, how are retail security leaders thinking about IoT? And how can they prepare for this innovation? Howitt suggested the key is to get ahead.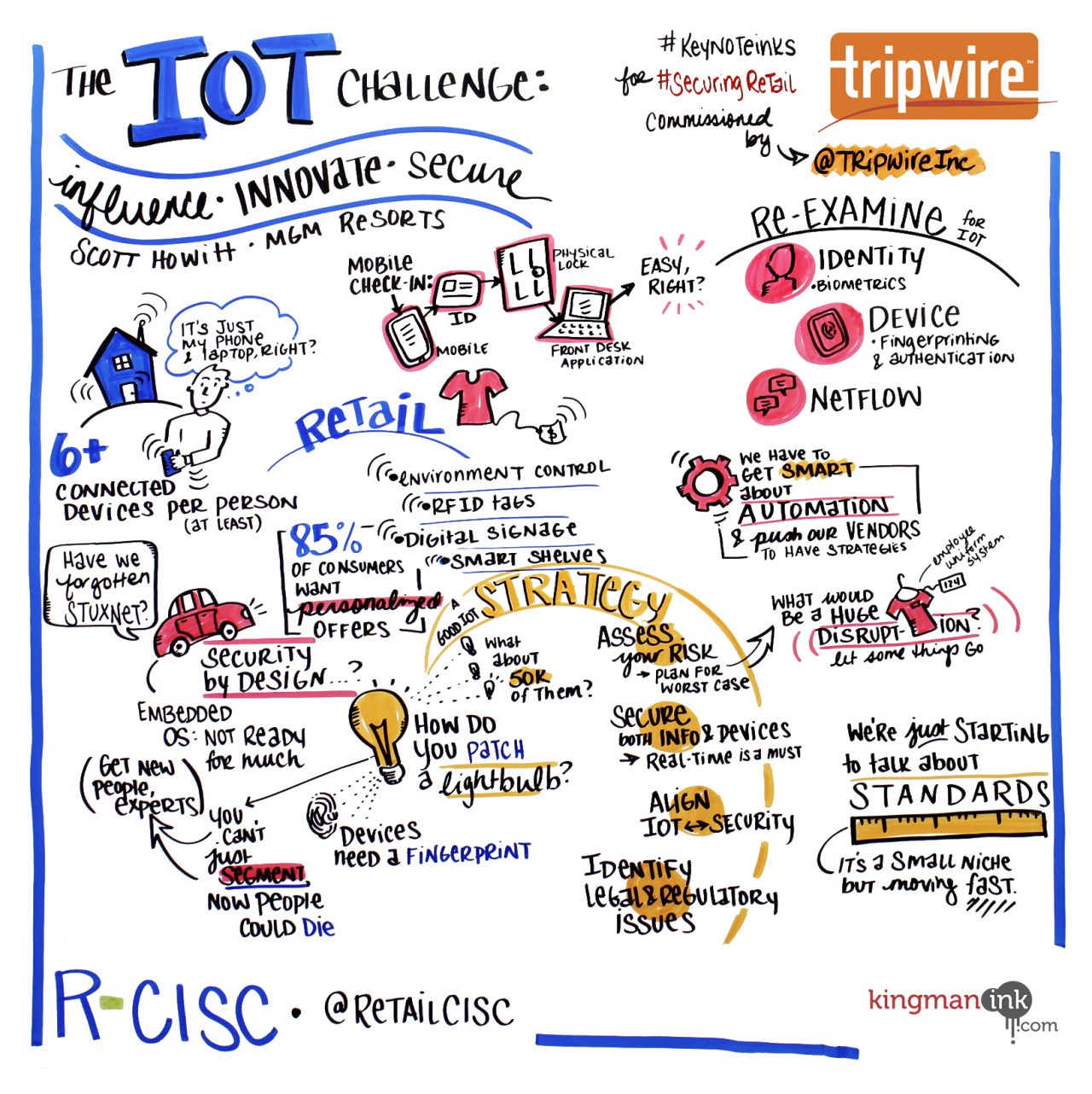
Disrupting the Economics of Cybercrime
Speaker: Brian Krebs, Journalist and Investigative Reporter In an ironic twist, security advances—such as the current EMV shift—often spur new opportunities for fraudsters, which leaves retailers wondering how to build on a constantly changing foundation. In this keynote, security journalist Brian Krebs offered a roadmap to disrupting cybercrime in a financially fluid world—starting with bridge-building between retailers and financial service providers. Krebs highlighted how this partnership can help organizations better understand the economics of cybercrime, identify criminal motivations and pressure points, and build appropriate deterrent strategies.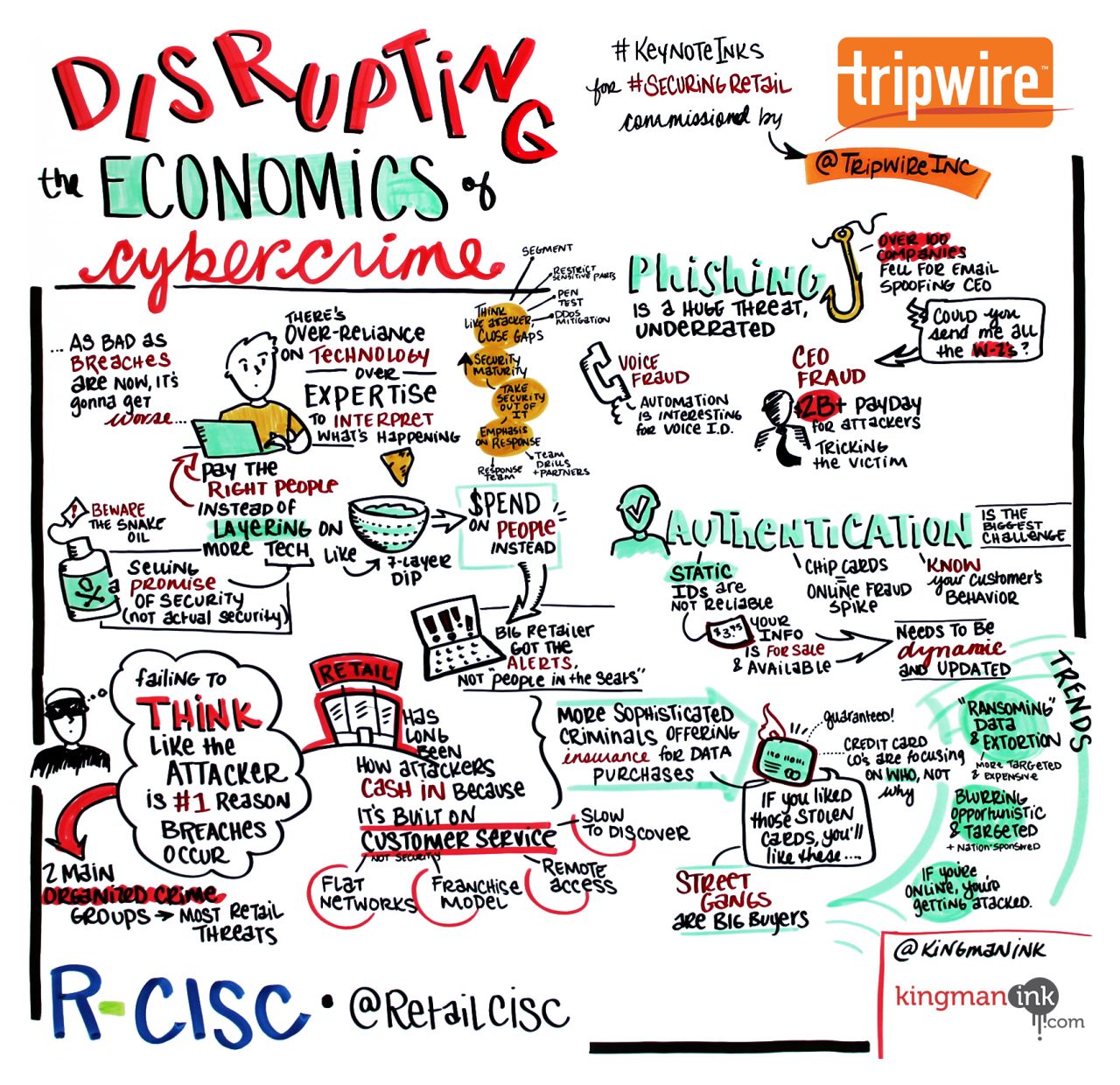
Risktocracy Rising: Lessons Learned on the Front Lines of Fraud
Speaker: Allison Miller, Product Manager, Security, Google The expansion of cybersecurity, especially in retail and consumer-facing platforms, has long been an exercise in ‘follow the money.’ Miller stressed that where money moves, so too do threats and exposures—ask anyone on your fraud prevention team. She discussed how platforms of all kinds leverage automation, big data and behavioral analytics to protect assets, accounts and end-users.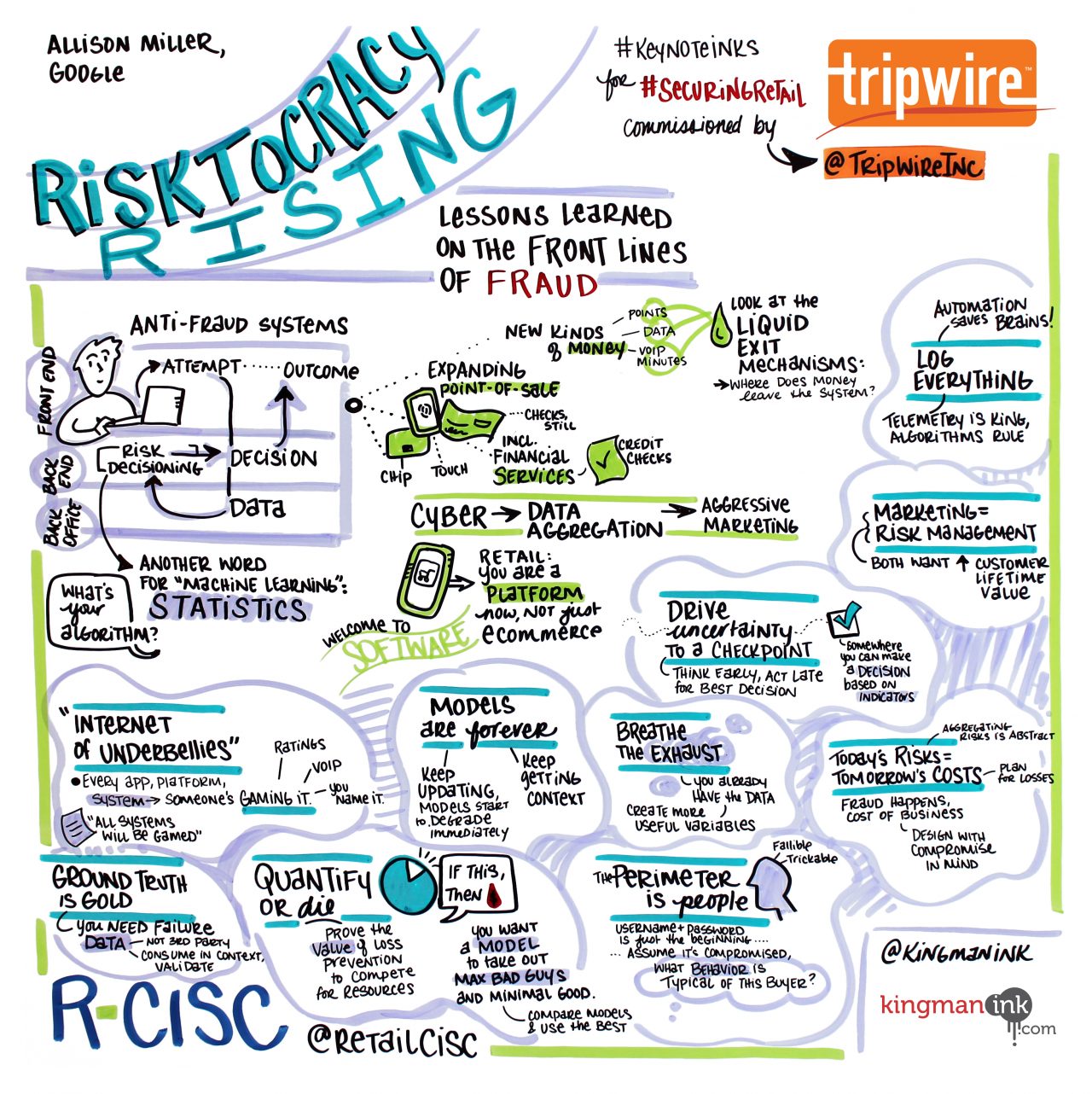
Applying Security@Scale to Your Business
Speaker: Alex Stamos, CSO, Facebook What’s it like leading the diverse, fast-moving team responsible for securing the data of more than 1.6 billion people? Stamos shared lessons for securing systems at scale against the most skilled adversaries and addressing some of the common problems facing all CISOs. Stamos explained how Facebook integrates secure development practices into a dynamic development environment, the effectiveness of unannounced and frequent red teaming, the benefits of threat indicator sharing, and what we can learn from one of the world’s largest bug bounty programs.
The Talent Strain: A Conversation in Creative Recruitment and Retention
Speakers: Amy Bogac, Director, IT Security Operations, Walgreens; Steven Young, VP, Security and Risk Management, CISO, Kellogg Company No one perceives talent quite like cybersecurity leaders. Faced with a critically undersupplied talent pool, managers dig for superstars in a climate of heavy competition, inflated pay rates and interindustry poaching—and that’s only half the struggle. Once your team is in place, how do you keep them engaged, and how do you build a strong benchmark for security? In this session, Bogac and Young provided strategies and tips for how to grow and enhance an organization's cybersecurity team – from engaging young and unconventional talent, to building creative hiring packages and employee enrichment programs.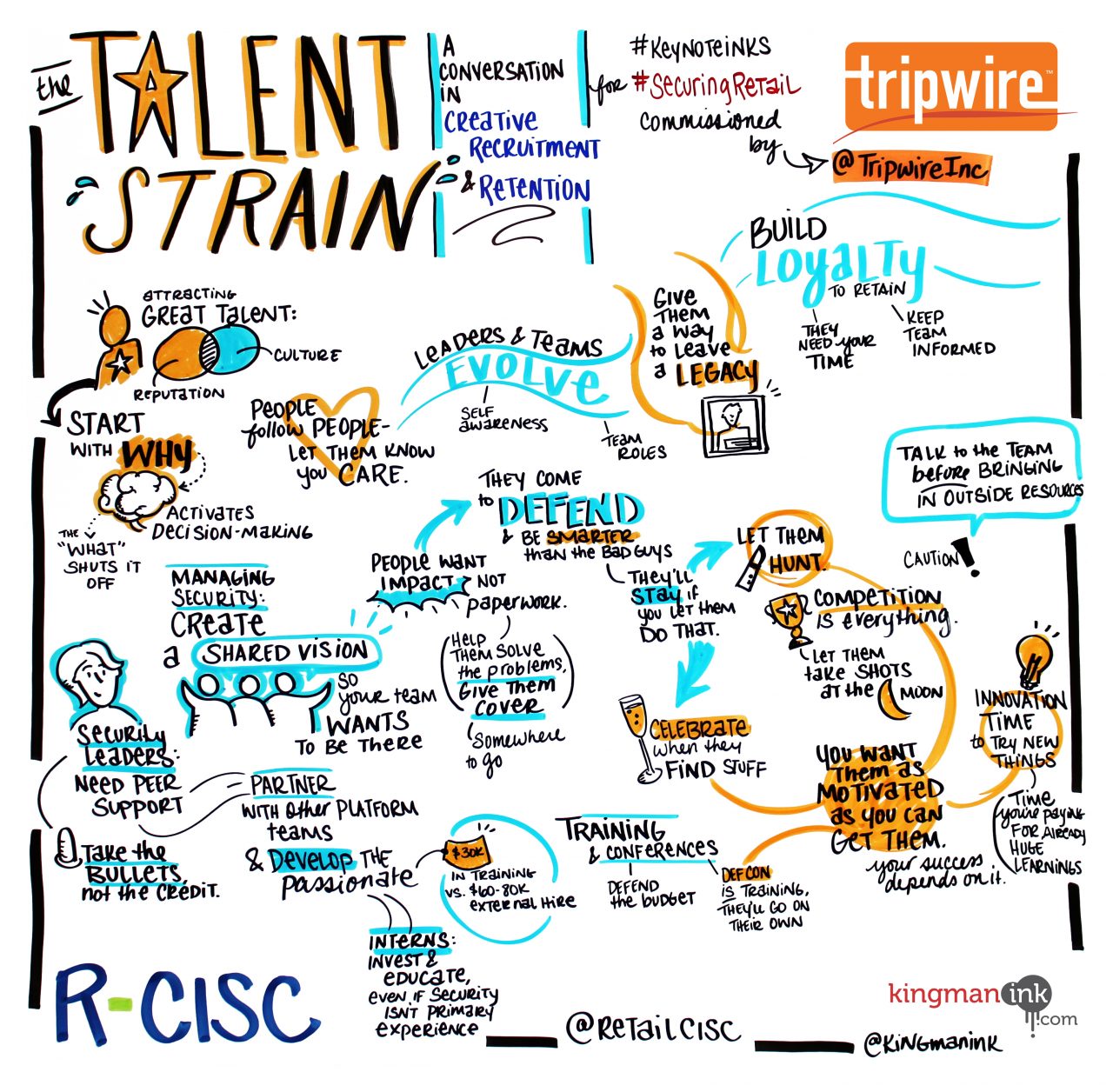
Disaster Response in the Digital Age
Speaker: Desi Matel-Anderson, CEO, Global Disaster Innovation Group, FIT During crisis response, every moment counts. Whether in the virtual world of cybersecurity or a real-world disaster in your community, empowering yourself, your team and company to respond is imperative. From the use of virtual reality in the Syrian Refugee Crisis to the creation of a robotic zoo in the US/Mexico border crisis, Matel-Anderson uncovers how technologies are empowering humans to create cutting-edge disaster solutions.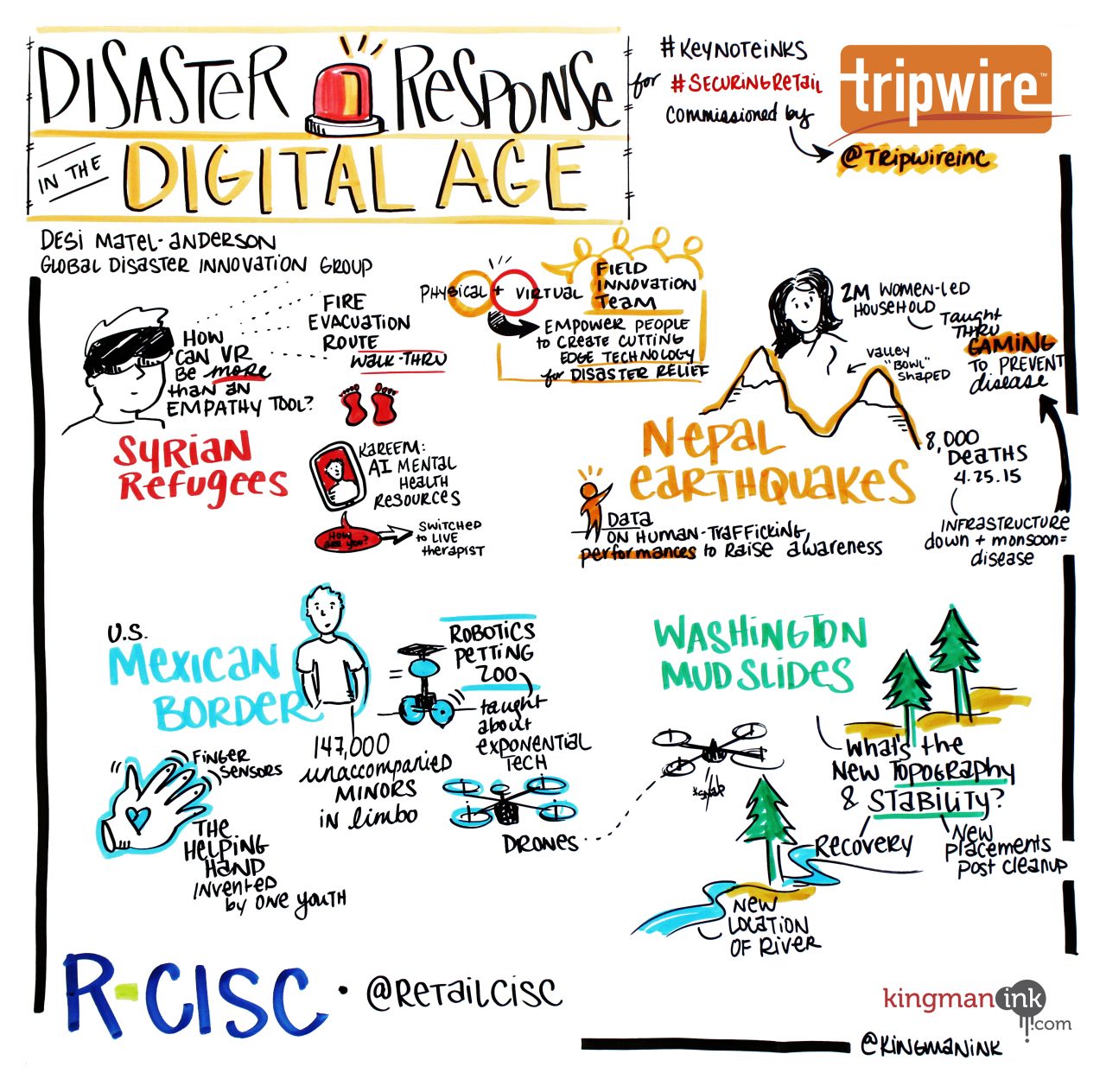
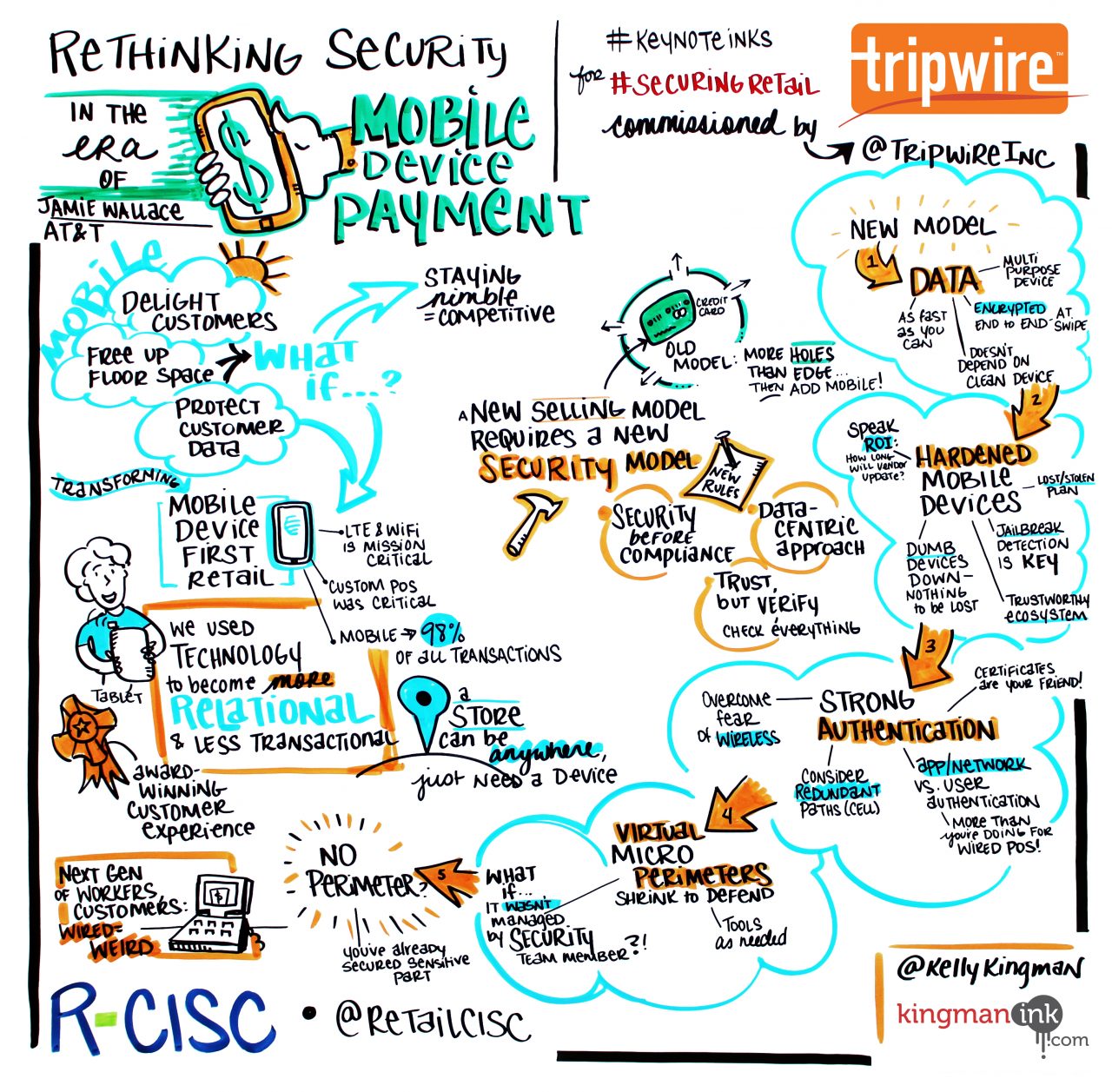
Rethinking Security in the Era of Mobile Device Payment
Speaker: Jamie Wallace, Retail Security Lead, AT&TTo attract and keep savvy consumers, retailers are getting creative with ways to pay. From personal device payments and iPod touch to Square and Apple Pay, payment flair is everywhere. What is the business impact of this evolution? How must teams rethink security to adjust? At AT&T, tablets are the new modus operandi. Customer-friendly and convenient, this method also serves to demonstrate the functionality of in-store product. Wallace shared AT&T's case study from inception to practice and strategies to launch and secure an innovative mobile payment program.
Retail 2020: Securing Subjective Technologies
Speaker: Brian Sathianathan, Co-Founder & Chief Digital Officer, Iterate Studio
The rise of emerging technologies like AI and virtual reality is taking the retail world by storm and spurring retailers to get ahead of (or at least on top of) the curve. How can industry security leaders prepare for ever smarter, more subject-driven systems? In this keynote, Sathianathan shared his vision for the future of retail. Drawing from experience in secret product and emerging tech development, he explored retail technology trends, the role of IoT and AI learning networks, as well as the integration of security and privacy into this fluid space.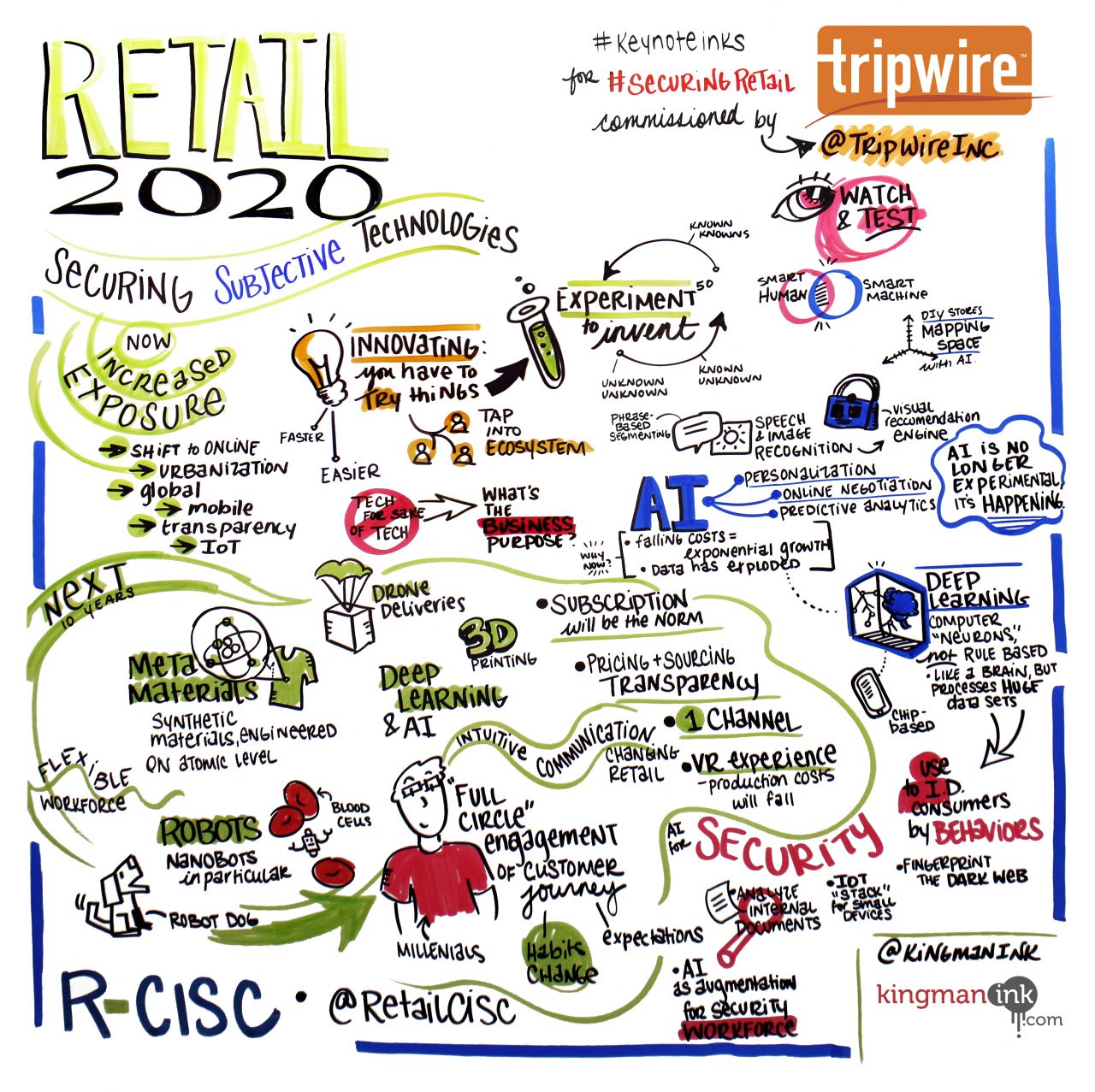
For more information on R-CISC, please visit: http://r-cisc.org/

