I’ve been studying the security designs of various embedded devices for the past couple of years. This research has led me to uncover dozens of critical flaws in internet-connected devices ranging from enterprise NAS devices and access points to countless consumer products like wireless routers, home automation controllers, security cameras and more. I even had the opportunity to hack a million-dollar smart beach home and demonstrate several baby monitor flaws on the nationally televised Crime Watch Daily series. After a while, I felt a lot like Sisyphus continuously pushing a boulder up a hill. Each disclosure takes a considerable effort on my part and frequently requires more time and energy than the actual vulnerability discovery. Vendors do not always make it easy to find the appropriate point of contact and generally lack anyone with a strong understanding of security. I concluded from these experiences that my time might be better spent teaching and evangelizing about device security rather than just finding the same bugs in different products day after day. This is something we discussed within VERT, and it eventually led to the creation of VERT’s IoT Hack Lab. The first IoT Hack Lab was run in 2015 at the 9th SecTor conference in Toronto.
We set up a handful of IoT devices and some Hacktops, giving attendees the opportunity to receive guidance on how to penetration test a device. We also used videos to quickly demonstrate IoT software exploits and had stacks of “cheat sheets” with tips for running an IoT security audit. Having a mix of fully patched and known vulnerable devices allowed us to guide some people through the process of re-discovering what we had previously found, while others were free to explore new territory in search of 0-day vulnerabilities. Interest in the Hack Lab was really quite exceptional, and we found ourselves with a full table for most of the day. Feeling encouraged from the experience at SecTor, I set out to expand on the cheat sheet with more detailed information on the processes I use to sniff out vulnerabilities. This work gradually ballooned into a rather large slide deck of training materials, and at some, I decided to also extend the Hacktop image to include the ability to emulate certain vulnerable components from the included firmware updates. I had the opportunity to put my skills as a trainer to the test when AusCERT invited me to lead a full-day training workshop at their 2016 conference in the beautiful city of Gold Coast, Queensland. This training material, under the name "Brainwashing Embedded Systems," was offered two more times in 2016 at DEF CON 24 as a 4-hour workshop and at SecTor 2016 as a full day of training. Earlier this month, we had the good fortune to run the Hack Lab at the New York State Cyber Security Conference, where I also gave a keynote presentation on the IoT threat landscape. The Hack Lab was, again, a great hit with dozens of conference attendees spending hours at our booth and leaving with a copy of the Brainwashing Embedded Systems course material VM complete with three virtualized embedded devices for continuing education after the conference. I’m pleased to announce that I will be returning to DEF CON and SecTor again this year for more hands-on IoT hacking. I am grateful to the organizers of both conferences for giving me the opportunity to teach from my experiences breaking device security models. Brainwashing Embedded Systems will be offered as a free 4-hour workshop at DEF CON 25, as well as a paid full-day training session at SecTor 2017. The IoT Hack Lab will also be available again in the SecTor expo hall.
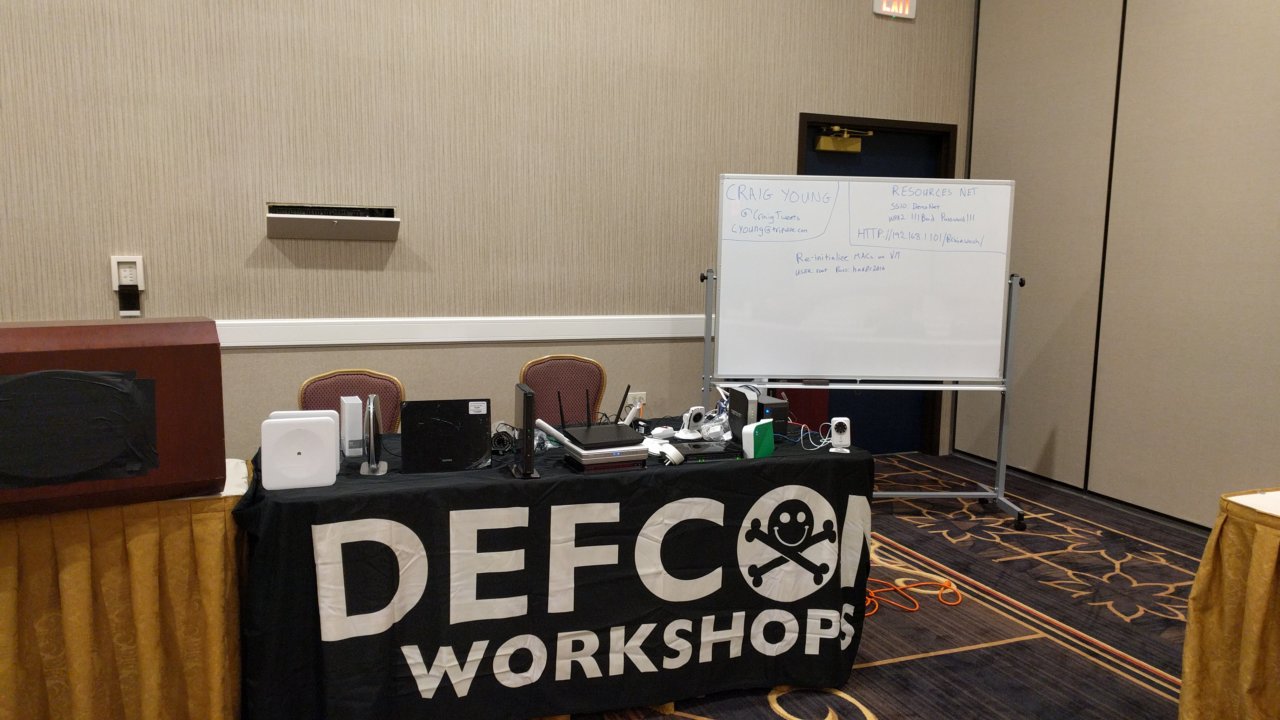
Spaces are limited for both of the training sessions, so early registration is recommended. The DEF CON 25 workshop will be held from 2:30-6:30PM on Thursday in room Octavius 4 at Caesar’s Palace. Pre-registration for DEF CON 25 workshops open in July. Check https://defcon.org for details. *REGISTRATION IS NOW FULL* SecTor 2017 registration for the training, as well as the expo hall is open at https://sector.ca/register/

