
People have become the primary attack vector for cyber attackers around the world. As the Verizon Data Breach Investigations Report 2022 indicates, it is humans rather than technology that now represent the greatest risk to organizations. According to the SANS 2022 Security Awareness Report, the top three security risks that security professionals are concerned about are phishing, business email compromise (BEC) and ransomware, all closely related to human behavior. Security awareness programs, and the professionals who manage them, are key to managing human risk.
An organization's capacity to successfully identify, manage, and quantify its human risk can be used to gauge the maturity of these awareness initiatives. Organizations may utilize the Security Awareness Maturity Model created by SANS Institute to assess the maturity of their awareness initiatives.
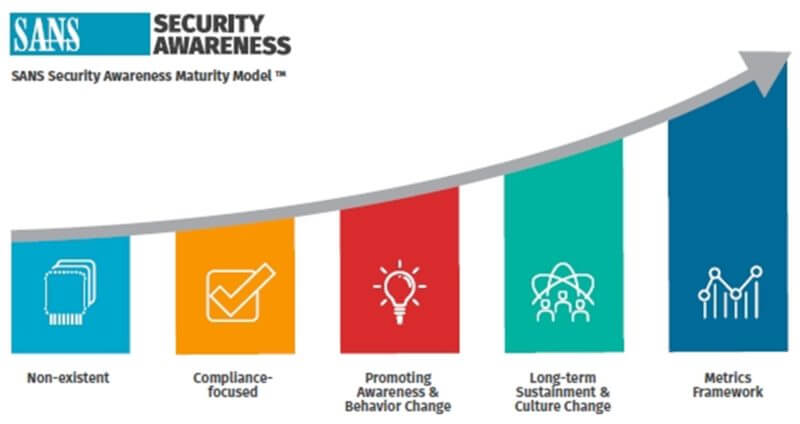
The Security Awareness Maturity Model enables organizations to identify and benchmark the current maturity level of their security awareness program and determine a path to improvement.
According to the same SANS survey, the best developed security awareness programs are those with the most personnel dedicated to administering and supporting them. These larger teams are more effective at collaborating with the security team to identify, track, and prioritize their most significant human hazards, as well as engaging, motivating, and training their staff to manage these risks. Demonstrating that awareness programs are no longer merely annual training to check the compliance box but are crucial for firms to effectively manage human risk, is the key to garnering leadership support.
Building effective and mature security awareness programs and sharing best practices were the goals of the SANS 2022 Security Awareness Summit, which took place on August 3-4, 2022. The summit was a hybrid one and I had the honor to follow the proceedings from the comfort of my home in Greece. Here’s what I have learned.
How to embrace a behavior first mindset
Cassie Clark, Security Awareness Engineering Manager at Brex, started her presentation by discussing the drivers behind a behavior. These drivers can be either individual – knowledge, motivation, biology and automatic thinking – or external including social codes and experience.
To change a behavior, one should isolate that behavior, identify the rationale behind that behavior, and assume that small interventions will be required. To instill a security mindset, organizations need to integrate security into everyday processes, make security easy to digest, and support it with appropriate technology mitigations.
Cassie Clark provided a helpful guide to get started with, which includes the following steps:
- Coordinate with the security team to identify top three behaviors that need tweaking
- Select one behavior and make a list of possible causes
- Infuse behavior into security messaging. Be careful to avoid noise and message fatigue, honor the varying learning styles, and use social proof to your advantage.
- Start collecting data
- Socialize the approach with leadership
Moving beyond awareness
Alexandra Panaretos, Americas Leader for Human Cyber Risk and Education at EY, kickstarted her presentation by posing an interesting question: “What if we didn’t focus on who we are now, but who you could become?” What would it take to enable secure business operations?
To achieve this goal, it is important to successfully reduce human risk. Panaretos identified four key elements of success in human risk:
- Engage - Create role and risk based activities and communications to deliver the right message, to the right person, at the right time to support desired security behaviors
- Enable - Provide employees with the knowledge and the tools to demonstrate appropriate security behaviors and make appropriate choices when faced with challenges
- Execute - Integrate cybersecurity into the role and daily lifecycles of the business
- Evolve - Secure culture builds on trust, effective communication, and positive experiences with security team members
Is conversation a catalyst of change?
Sarah Janes, Owner and CEO at Layer8, provided insights how security champions can foster culture change through conversation and collaboration. This approach is based on scientific research on organizational culture by Edgar Schein and appreciative inquiry by David Cooperrider.
Janes demonstrated that security champions can influence behavior change if they follow the formula (conversation + collaboration) * positive focus. Having security champions that are more active and engaging with their colleagues led to reducing risk because colleagues were more eager to report security incidents and suspicions.
Finally, Sarah Janes offered a roadmap to change behavior:
- Define behavior: utilize champions to find behaviors
- Agree your key results: join the dots to show how stories impact numbers
- Find data sources: changes to systems are easier if there is a line of sight to business risk
- Collect the data: create awards, gamify, but be inclusive
- Present the data: use case studies from other businesses
- Use the data: use data to build the business case for more champions
How to make a developer love security
Madeline Howard and Sophia Adhami from Sage discussed the approach they have followed to enable the development of secure software. The first step was to understand the world of developers. They did so by interviewing AppSec people, product owners, and security champion managers. They also attended all team meetings. Their goal was to understand the developer mindset – the tools they use, the complex technology environment, what makes them tick. By understanding their behavior, Howard and Adhami wanted to build respect and acknowledge their expertise.
Based on the findings of their internal research, they then went on to create the structure to support the change and finally engage developers. The top executives and the AppSec managers set the tone by making security a top priority and then they built tailored messages to communicate the tone to the developers. All developers underwent technology and vulnerability specific training to understand the risks to the business of insecure code. Motivation was provided through awards and recognition – security champion wall of fame, CISO emails, prizes and t-shirts, articles on the intranet.
Howard and Adhami measured change from the onset of their project and they were able to demonstrate to the leadership as well as to the developers that investing in this strategy resulted in decreasing time to fix flaws by 82%.
The key takeaways from this use case are that:
- You do not have to be technical; you just have to be willing to listen
- You are not creating a new culture; you are aligning cultures. We are adding in security so that we all pull in the same direction
- Technical colleagues want to do the right thing, you have to make engagement work for them
Conclusion
There were many more interesting presentations – for example the Equifax use case of how the company transformed their security culture following the 2017 incident – that all demonstrated the importance of focusing on the human element of cybersecurity. Every organization has a culture. The important thing is to transform your culture to become a positive driver of enabling security throughout your business processes. Building a security awareness program that works is possible – just look at that the success stories from other businesses in your industry and adapt best practices to your organization.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

