
Data breaches are common in the news lately, but a recent study by credential monitoring firm VeriClouds focuses specifically on the credentials of Fortune 500 employees found in account leaks posted online. Using a corpus of 8 billion stolen credentials gathered over three years, the total number of employees of each Fortune 500 company was compared with the number of unique credentials for each company found online in data leaks. The study finds that an average of 10 percent of all Fortune 500 employee email credentials have been leaked via some form of data breach. The greater the number of account credentials found online, the greater the risk that one of those details can be used to gain access to company resources. That risk is real; some industry sectors such as Telecommunications were more than double the average at 23 percent of employee emails found in a data leak. Other higher-than-average sectors exposed included Energy at 18 percent and Financials at 17 percent. That 17 percent represents a total number of 555,000 email credentials found leaked across Fortune 500 financial companies. The password strength of the leaked credentials was also examined. Overall, the report found that some sectors had large percentages of weak passwords in use. Two of the higher examples were Computers and Office Equipment with 25 percent weak passwords, as well as Transportation with 17.6 percent of exposed passwords being found in the top 100K most common passwords. These leaked credentials can be difficult for even a Fortune 500 organization to defend against, as the risk may exist completely outside of security staff control. Steve Tout, CEO of Seattle based VeriClouds, is deeply familiar with this dilemma:
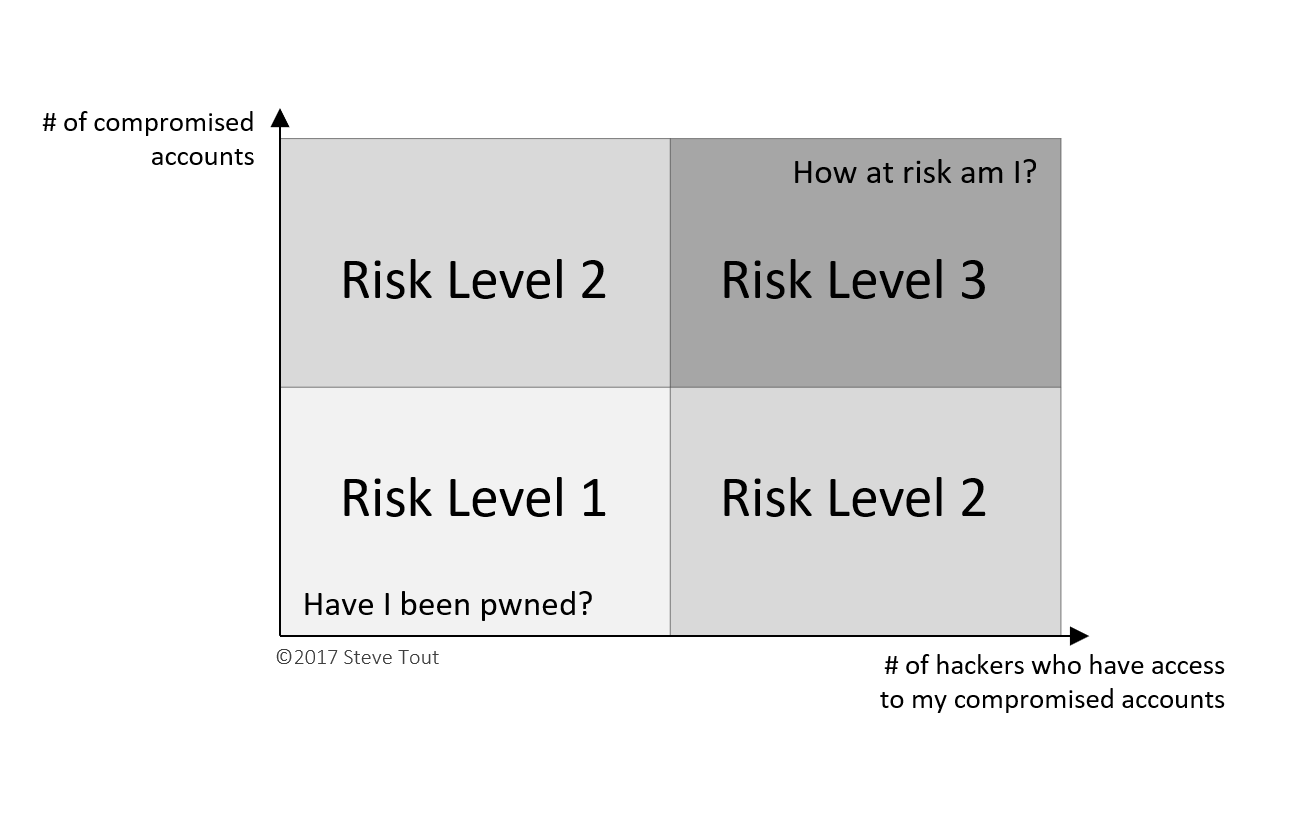
"It is no longer enough to answer, 'Have I been pwned?' The risk that compromised credentials pose to users and business increases exponentially as leaked credential data becomes readily available to nation-state attackers and cyber criminals through the dark web. Forward-thinking organizations need to adopt security solutions that help answer the question, 'How at risk are my users and my organization?'"
Take, for instance, password reuse amongst online accounts, a threat which is common in high-profile data leaks such as Sony and Yahoo and the myriad of smaller or even as yet undiscovered hacks. Both types of incidents could be putting your important partner accounts at risk. Additionally, there exists the potential for an attacker to use these leaked credentials for more traditional attempts at compromise via self-hosted services. As organizations move more functions into cloud and software-as-a-service providers, a greater number of third-party accounts are becoming business critical. Among others, social media accounts used for marketing communication and cloud provider accounts used for hosting could be especially devastating if compromised. It is important to ensure that all organizational third-party infrastructure, software, and platform service accounts are secured with multi factor authentication to provide an extra layer of defense against these types of compromises. Users should also be educated on the importance of a good password policy and the dangers of password re-use, and they should receive encouragement to use a password manager to improve password quality. Tripwire offers multiple solutions to help secure against data leaks. Enforcing regulatory compliance can help ensure internal password policies are met and data exposure is minimal in case of a breach. File Integrity Monitoring can detect the instant an attacker establishes themselves in your network. Vulnerability management can find services you didn’t know existed and protect you against an attacker’s lateral movement. To find out more about Tripwire solutions, click here.

