
A new sextortion scam is informing victims that their computers suffered a malware infection after they visited an adult website. In this latest ruse, digital criminals claim that they infected a user with malware after they visited a child pornography website. They then say that they leveraged that infection to capture compromising video footage of the user. Finally, the attackers threaten to share the video with the targeted user's email contacts and Facebook friends unless they meet the extortionists' demands and pay $2,000 worth of Bitcoin within 72 hours. Here's a copy of the scam note, as provided by Bleeping Computer.
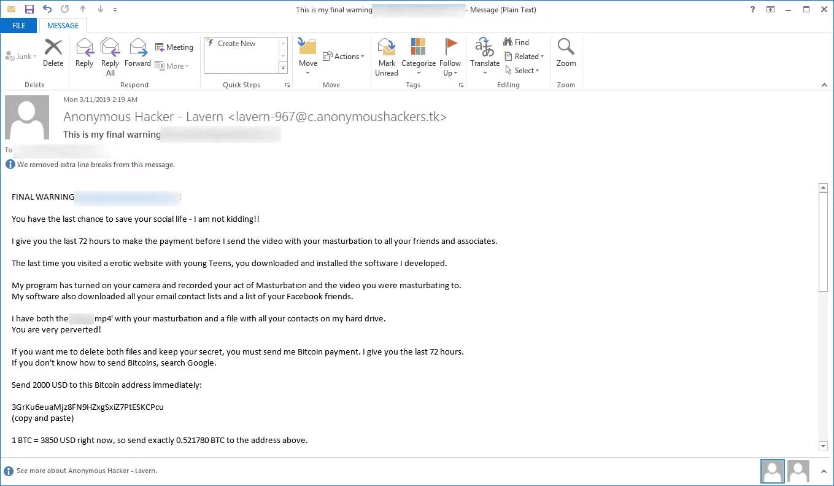
Final Warning Sextortion Scam Email (Source: Bleeping Computer) As you can see, the digital criminals threaten that they'll release the video if the user tries to deceive them. As quoted in the note shared by Bleeping Computer:
You can visit the police but nobody will help you. I know what I am doing. I don't live in your country and I know how to stay anonymous. Don't try to deceive me - I will know it immediately - my spy ware is recording all the websites you visit and all keys you press. If you do - I will send this ugly recording to everyone you know, including your family. Don't cheat me! Don't forget the shame and if you ignore this message your life will be ruined.
This isn't the first time that bad actors have preyed on users with sextortion scams. Indeed, there have been no less than three such sextortion variants since July 2018. The earliest version used breached passwords to trick victims into meeting their demands. Another variant used redacted phone numbers, while the most recent iteration infected users with GandCrab ransomware. As with these earlier versions, users who come across the newest sextortion scam variant discussed above should not give into the extortionists. They should instead keep an up-to-date security solution installed on their devices as well as exercise caution around suspicious email attachments and embedded links.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

