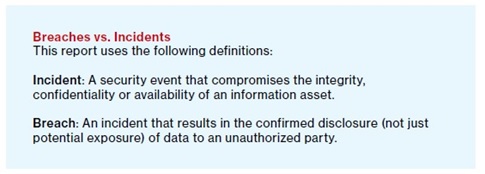
Think of a word that sparks an emotion in you. It could be as simple as “shoes,” which makes my wife smile every time, or it could be a dark and foreboding word. Certain words trigger an emotional—sometimes visceral—response. For me, one of those words is “breach.” In a recent post about the Department of Health and Human Services’ (HHS) classification of a ransomware event as a “breach,” I take the position that ransomware should not be classified as a breach. I have tossed this idea around with an associate, as well as with friends. There seems to be no agreement about what constitutes a breach, and the dictionary definition offers little assistance from an information security perspective. (The word “selfie” is in the dictionary, however.) I remember from my very brief attendance in law school that one of the biggest challenges in law is the definition of terms. This is why legal parlance is so confusing to non-attorneys. Anyone who has purchased real estate has come across the phrase “fee simple absolute,” and anyone who has written a last will has learned the meaning of “per stirpes.” These phrases, handed down over the course of time, have traditional and well-understood meanings in the legal lexicon. (Look, mom – I learned something in law school!) As of now, we have no such common lexicon in the world of information security. Even the most cursory review of recent articles about a data breach always reference that data was taken and re-used in some way. As corroborating evidence, the venerated Verizon Data Breach Investigations Report does not classify a ransomware event as a breach. Rather, according to the Verizon DBIR, ransomware is “crimeware.” One need not read beyond page 5 of the report to find a reasonable definition of the difference between an “incident” and a “breach”:
The FBI also does not classify ransomware as a data breach. I agree that in the traditional sense of a fortress, levy, or bank vault, a breach can be thought of as any break, rupture, or gap in a perimeter. Whenever I read the word in a newspaper headline, I envision the majestic photo of a whale breaching the ocean surface, and that is precisely the problem with the current HHS classification; a breach is about things leaving their normal environment. In a ransomware event, none of the data leaves the original location. It is easy to discuss a ransomware event and end up teetering on the cliff of what could happen rather than the reality of what has actually happened. If breach notification guidelines are predicated upon the idea of what “could have happened,” then all phishing attempts should be regarded as a breach since the phishing attack “breached” the perimeter and got into your mailbox. Do you want to be notified every time a phishing e-mail is delivered to your doctor, hospital, or physical therapist’s office? How soon before you report that stuff as SPAM?
The question that I hope to raise in my dispute of the new classification by the HHS is not so much whether you agree that ransomware is correctly classified as a breach, but rather, are you truly comfortable with such a broad definition of the word “breach”?
Personally, I have a visceral response to that overly broad definition. Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.