
A typical information security conference can cost $5,000 plus plane and hotel costs and, although it might seem to be an exorbitant sum of money, many of us could easily defend the value and necessity of the training to bolster one’s technical capabilities. But when was the last time you invested even just a few hours of your time to working on developing your information security career in truly meaningful way? Technologies are advancing rapidly, and there is good reason to always be learning new tech skills but if you strip away the revolving technologies from what you do, there you are. Infosec skills are essential, but so are YOU! It is important to focus on building your long-term career and not just your tech skills, some of which come and go. There are many reasons to develop your career for the long haul. Here are a few in question form to get you thinking about them: Are your completely satisfied with your current employer, and do they respect and compensate you fairly based on the value you deliver? Is what you do making the world a better place? Are you working on your life’s work? Do you aspire for a more meaningful role?
P.A.D.S. Success Model
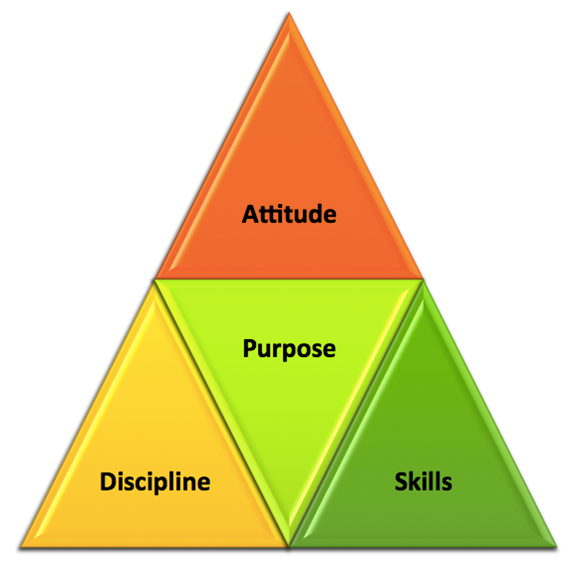
It can be helpful to visualize your career development objectives using the P.A.D.S. success model. Central to success is having a definitive purpose that you are passionate about (e.g. developing penetration testing tools). Having a good attitude toward your work and others is essential to career progression. Discipline helps you develop a structure for consistently meeting goals (e.g. finishing a pen test report). Finally, you want to have both technical and interpersonal skills in this business.
Infosec Career Cone
When creating an individual development plan, getting your vision documented, instead of just keeping it in your head, is crucial but most forms make it difficult to imagine what success really looks like. Many of our next steps are not merely bullets on a list but are instead ranges of possibilities. They are combinations of both our deliberate efforts and available opportunities.
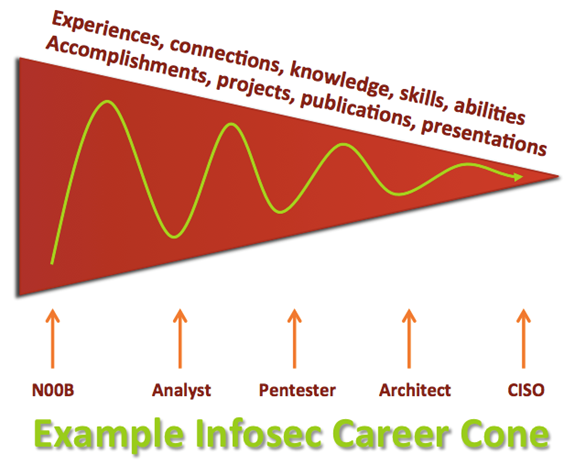
Using the cone of uncertainty, commonly used in project planning, for visualizing your infosec career can be helpful. What is important to keep in mind is that at each stage in your career, you should strive to develop experiences you will be talking about much later in your career. For example, an information security analyst will produce resume bullets that will be pertinent when they apply for the CISO role ten years from now. These experiences could be security incidents your were involved in, relationships you have forged with other security practitioners, projects you helped lead, publications you have written, presentations you have given, skills you have picked up along the way and more.
Information Security Career Development Plan
With this in mind, give your information security career development plan a shot with these simple steps:
- Define your mission and goals
- Identify gaps
- Develop an action plan
- Execute your plan
- Continually assess your progress
I hope this article has inspired you to deliver your life’s work. Just remember to stay focused on taking actions that benefit both your career and your employer. If you find yourself struggling to find congruence, it may be time to propose a shift in your role at work. Constantly take steps forward along your career path even if it means parting ways with an employer. Life is too short and what you have to offer is too precious to wait or beg permission from someone else to unleash your gifts to the world and experience the fruits of your labor. To learn more about developing your information security career and helping others in the security community, consider attending my presentation at BSidesSLC on March 20 and 21 in Salt Lake City.

About the Author: Glen Roberts is the host of the Hackers On Fire podcast and has over a decade and a half of experience managing infrastructure & security teams. Glen is finishing his Master of Science in Information Security Management at SANS Technology Institute and possesses several industry certifications including CISSP, MCSE, MCDBA, GCIH, GWAPT, GSLC, GSNA, GLEG, GCPM, CCSK, ITIL, Apple Certified Associate and IBM Certified Solution Architect. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. If you are interesting in contributing to The State of Security, contact us here.

