Financial gain or fraud was the primary driver of the 11,698 instances of insider privilege abuse – defined as any unapproved or malicious use of organization resources – in last year's Verizon Data Breach Investigations Report.
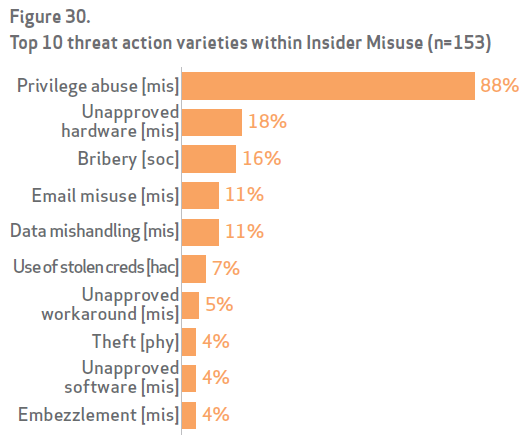
Source: 2014 VDBIR A malicious insider can be detected in a number of ways, and there are both non-technical and technical indicators of risk. Some non-technical indicators include:
- The not-so model employee – This individual has been consistently the first in and last out of the office lately. There’s a lot of work to do so this individual is pulling some long hours. If there isn’t a project due soon, this could be an indicator that the individual is working on a little extra-curricular malicious work.
- The Ironman streak – An individual who hasn’t taken a vacation in a long time may not have had the opportunity to share his or her work with others. If they are keeping their work to themselves without collaborating or having others review, there is a chance that their project is of that extra-curricular malicious nature.
Both of these indicators lead back to the same root. The individual is trying to hide their malicious intentions from others, and exploiting the trust gained within the organization for their own malicious intent. Technical indicators are a little easier to identify. Rules can be setup in your SIEM, DLP, etc. to detect these indicators. Some of the technical indicators include:
- Increased number of logins varying in remote and local
- Logging into the network at odd times
- Change in websites visited from work to personal
- Increased export of reports and downloads from internal systems
- Unauthorized cloud storage sites being accessed regularly
What Causes An Employee To Go Rogue?
The answer to this question, unfortunately, isn’t a simple one. There could be a variety of factors which contribute to the Recruitment or Tipping Point of an individual as described in the Insider Threat Kill Chain. This is the point where the insider turns from good to bad.
- An outsider promise – An outsider, such as a competitor, could provide a financial incentive for an insider to turn rogue. As a reward for siphoning out information, the competitor could promise employment within their company.
- A life changing event – If the individual has a tendency to keep to themselves, others may not know of a life changing event. This may not directly cause an individual to turn rogue, however, combined with an outsider promise, they may think they have nothing to lose.
- Two weeks notice – An employee who is about to leave the company may want to take something with them on the way out. This could be customer information, trade secrets, or anything that may be useful in a future role. This is an unethical act and often (if it isn’t, it should be) against company policy.
- Stagnancy – An employee who was recently disciplined or perhaps passed over for a promotion or raise may be looking for revenge. There is potential for this type of an individual to reach their tipping point and become a malicious insider.
The Sky Is Falling! What Do I Do?
Have you heard the saying: “An employee doesn’t quit a job, they quit their boss,” or “A person who feels appreciated will always do more than what is expected.” There is a lot of truth to these when it comes to reducing the risk of an employee turning into a malicious insider. If an individual feels appreciated and enjoys what they do, they will ensure they do a good job. If an individual enjoys and cares about working for their company, they will ensure they protect the secrets of that company. Not only does an individual’s success become the success of the company, but the success of the company becomes the individual’s success. From a non-technical perspective there are several precautions that can be taken to detect and prevent insider threats:
- Consider threats from insiders in risk assessments
- Ensure background checks are conducted on all new hires
- Clearly document and enforce policies and controls
- Conduct security awareness training for all employees
- Monitor and respond to suspicious behavior
- Anticipate and manage negative workplace issues
- Establish clear lines of communication and procedures between human resources, legal and the IT teams
From a technical perspective some of the controls that can be considered are:
- Implement strict password and account policies
- Enforce separation of duties, least privilege access and data classification
- Track the use of privileged accounts
- Implement system change controls and an approval process
- Deactivate access following termination or modify access when a role is changed
- Log, monitor and audit employee network activities
Malicious insiders are definitely a threat that can affect any organization. If you are in the Vancouver area and are planning on attending BSides Vancouver, Tripwire Security Analyst Ken Westin and I will be speaking about insider threats, including case studies and the ways of detection. Hope to see you there!
Resources:

The Executive’s Guide to the Top 20 Critical Security Controls Tripwire has compiled an e-book, titled The Executive’s Guide to the Top 20 Critical Security Controls: Key Takeaways and Improvement Opportunities, which is available for download [registration form required]. Title image courtesy of ShutterStock
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

