
In the attacker's world, all vulnerabilities and potential exploits work toward the hacker's advantage — not yours, not mine. This includes WordPress hacks. While living back east (over a decade ago), I was friends with several small business owners. One weekend morning, the owner of the local photography studio called me at 7 am and said: "I think I've been hacked." I could hear the soft clicking of a keyboard in the background. Once he began describing the state of his hacked website — all those sweet clicking keyboard sounds erupted into a wild swarm of angry bees. Meanwhile — still brain-fuddled and immensely groggy — I asked him a crucial question, "do you have a backup?" Dead silence ensued. I held my breath. Maybe he held his, too. After about ten seconds, he replied, "No, I do not have a backup." For the most part, WordPress hacks can be rather complicated, and if you don't have a backup, a hacked site will make an adult wail like a baby.
13 WordPress Worst Security Practices
WordPress hacks happen all the time. Keeping your WordPress site safe from cybercriminals requires that you avoid plummeting into the froth of WordPress worst security practices. When a WordPress site broadcasts worst security practices, you can rest assured — the bad guys will always line up to listen. WordPress worst security practices include:
- Minimal or no WordPress maintenance (not updating core, plugins, and themes).
- Not backing up the database and files.
- Lack of malware checks, security scans, security plugins (or services) and security monitoring.
- Failure to limit login attempts.
- Failure to use sitewide SSL.
- The use of weak passwords.
- Using the default user admin account instead of using a custom name.
- Adding too many admins (use caution when giving user privileges).
- Not using two-factor authentication (2FA).
- Using plugins and themes from untrustworthy sources.
- Failure to use the latest PHP version.
- Failure to use a firewall.
- Using "cheap" low quality or shared hosting.
Though the above list is not comprehensive — on the positive side, it provides a baseline to build upon. To clarify, moving away from WordPress worst security practices can improve your security posture. Furthermore, if you shift to security best practices, you can dumb down the listening prowess of the bad guys.
Automated Tools
Many small businesses have limited budgets alongside insufficient security knowledge. In other words, this combination often overlooks website security as an essential priority. Perhaps your small businesses or startup uses WordPress. You may not even know what platform your website runs on. If you haven't a clue as to what powers your company website, you can ask your web designer, query BuiltWith or use a browser extension like Whatruns.
The relative ease of attacking a smaller business has become such that it’s now perceived as being worth a hacker’s time and effort in more cases – particularly when smaller businesses don’t patch out known vulnerabilities that hackers can use automated tools to quickly scan for and exploit. – Scott Ikeda, CPO Magazine
With the ease and use of automated vulnerability tools, it's easy for businesses (of any size) to be targeted by hackers. Remember this: for cybercriminals, WordPress hacks are an easy slam-dunk when worst security practices enter the arena.
WordPress Is a Hot CMS
In late May of 2003, I experienced the birth of WordPress 0.70. No plugins. Zero widgets. No spellcheck. Sixteen years later, this particular CMS has undeniably become the love of my writing life! Its evolution over time has been nothing short of Olympian. WordPress is currently one of the fastest growing content management systems. As of this writing, WordPress is used by 34% of all websites and has a CMS market share of 60.7% (see figure 1). BuiltWith lists at least 24,808,989 live websites that use WordPress. What's more, there are over 800 new sites built daily and more than 55,000 plugins.
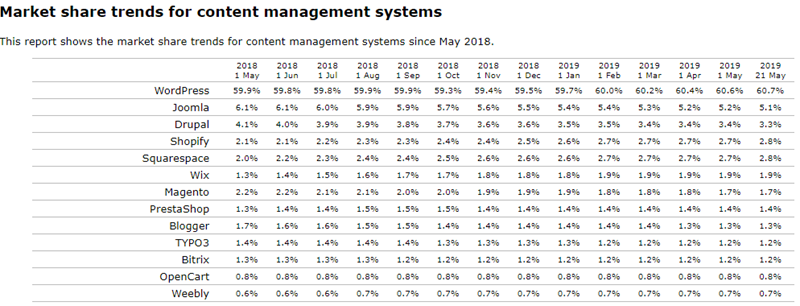
Figure 1: W3Techs CMS Market Shares
Checks and Balances Rule
Transitioning from worst security practices to security best practices is equivalent to acknowledging an elephant has been coexisting with you in the room. This magnanimous twelve-ton entity you previously were unaware of has materialized and come to life. In the meantime, you must plan to remove this behemoth creature from the room. What's more, it is absolutely critical to begin keeping tabs on all your digital assets. This includes your company website. In other words, company involvement in website security is crucial. To clarify, If you hired a consultant or outside agency to handle your site, you should also have an internal employee crewing the ship. Above all, remember this: the ability to act on knowledge is power. Undeniably, to put it another way, checks and balances should always rule.
WordPress Hacks
There are several ways attackers can hack your site. With WordPress powering 34 percent (see figure 2) of the Internet, the bad guys are always looking for ways to exploit WordPress vulnerabilities. Whether it is via common weak spots like comments, contact forms, old insecure WordPress versions, plugins, themes or weak passwords, hackers embrace any opportunity that hinges on a set-up-and-forget mentality.
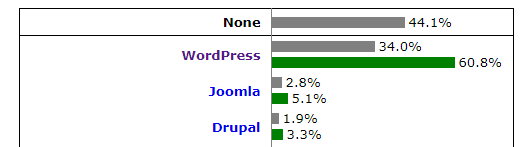
Figure 2: W3Techs, WordPress Runs 34% of the Entire Internet According to a recent Sucuri report, in 2018, WordPress suffered 90 percent of CMS cyberattacks, (up from 83 percent in 2017). Sucuri also noted other key findings in CMS exploits related to improper deployment, security configuration issues, a lack of security knowledge or resources, overall site maintenance by webmasters or broken authentication and session management. To clarify, a passive approach to website security can leave you unequipped and unsuspecting of any WordPress hacks that have occurred. Not to mention, weeks can bleed into months, and months can flow into years before an incident is discovered. In the attacker's world, all vulnerabilities and potential exploits work toward their advantage.
Build a Security Mindset
By now, you are probably wondering how to remove the elephant from the room. To begin with, elephants obviously can't fit through the door. You will have to tear down the wall, lead the elephant out and then rebuild the wall. This is the same way you need to approach the use of WordPress worst security practices. At the present time, If you have a WordPress site powered by a set-up-and-forget mentality, it's time to clean up the dung. Firstly, to minimize the possibility of WordPress hacks, you should employ WordPress best security practices (by reversing the 13 worst security practices listed above): WordPress security best practices include:
- WordPress maintenance (always update the WordPress core, plugins, and themes).
- Always backup the database and files.
- Implement malware checks, security scans, security plugins (or services), and security monitoring.
- Limit login attempts.
- Use sitewide SSL.
- Enable strong passwords.
- Remove the default admin username and replace with a custom name.
- Limit admins (use caution when giving user privileges).
- Use two-factor (2FA) authentication.
- Only download plugins and themes from reputable sites.
- Use the latest PHP version.
- Use a firewall.
Secondly, you should evaluate your hosting needs with a security mindset. Never leave all hosting decisions with your consultant or website designer. More often than not, they lack the security expertise for hardening and maintaining your company webs. In other words, you should have an internal employee who is knowledgeable in WordPress, MYSQL and PHP to maintain checks and balances. Additionally, the best options would be to hire a system admin to manage your website or purchase managed WordPress hosting.
Don't Forget to Monitor WordPress Plugins
With so many vulnerabilities continually being discovered in WordPress plugins, a set-up-and-forget mentality coupled with worst security practices can prove disastrous.
Cybercriminals actively look for new vulnerabilities in popular content management systems such as WordPress and Drupal, as well as popular plugins that are found on many websites. An unpatched vulnerability in either the CMS or associated plugins provides an entry point for attackers to compromise the website by injecting malicious code and impacting the unsuspecting users visiting these sites. — Prakhar Shrotriya, Zscaler
Recent examples include WP Live Chat Support malicious redirects and Convert Plus that allowed unauthenticated attackers to create accounts with administrator privileges. What's more, last month researchers warned that the wildly popular WP Database Backup plugin could let attackers take over a victim’s entire operating system! Though this flaw has since been patched (as of version 5.2), the sheer possibility of a plugin firing off an OS command injection should send hackles up your back.
In unpatched versions of WP Database Backup, an attacker is able to inject operating system (OS) commands arbitrarily, which are then executed when the plugin performs a database backup. Injected commands would persist until manually removed, executing each time a backup is run. — Mikey Veenstra, Wordfence
The above example illustrates why it is imperative for you to update plugins post haste. Also, you should always delete unused plugins and avoid abandoned plugins altogether.
It's Wrap-Up Time
As I have noted above, all small business websites (including startups) need to reject this set-up-and-forget mentality. Most important, you should remove the elephant from the room by building and maintaining a healthy, cybersecurity mindset. By the same token, you should always apply security best practices. In truth, we are all connected...by keeping your website healthy and happy, you will be giving back to the Internet as a whole.

About the Author: Bev Robb is a freelance writer/editor/social media manager and “thought leader” for information security. She has written security articles for Dell, BMC, Simility, and Tripwire. Previously, she was the Fortscale Security Technology Editor/writer and Publication Manager/writer for Norse Corporation. She has a B.S. in Sociology from Southern Oregon University. A computer security/Internet consultant for 25+ years, she started her digital life on the Internet before the advent of the Mosaic browser.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

