
One of the world's leading wire and cable manufacturers, Leoni AG, has been swindled out of a jaw-dropping 40 million Euros (approximately US $44 million) after it was targeted by an email scammer. As Softpedia reports, a young woman working in the finance department of Leoni's factory in Bistrita, Romania, received an email in mid-August claiming to have come from the company's senior German executives. Using inside information to appear more convincing, the email was able to trick the recipient into believing it was a genuine request for a staggering 40 million Euros to be transferred out of the company's bank account. Unconfirmed reports claim that the stolen money was switched into bank accounts in the Czech Republic. The revelation of how the fraud was perpetrated comes after a two-week investigation by Leoni and Romania's DIICOT (Directorate for Investigating Organized Crime and Terrorism) law enforcement agency.
Leoni's stock has dropped almost 7 percent since it announced it had been attacked. There are obvious financial losses that corporations can suffer as a result of business email compromise (BEC) attacks, but it's worth regular employees realizing that they might also feel the repercussions if they are the unwitting participant in CEO fraud. For instance, an employee of payroll and merchant services provider Alpha Payroll was fired earlier this year after being duped into sending W-2 data to a scammer posing as the company's CEO. Business email compromise, also sometimes known as "whaling" or "CEO fraud," is a growing problem. Well-known corporations that have fallen foul of such attacks this year have included Snapchat and Seagate.
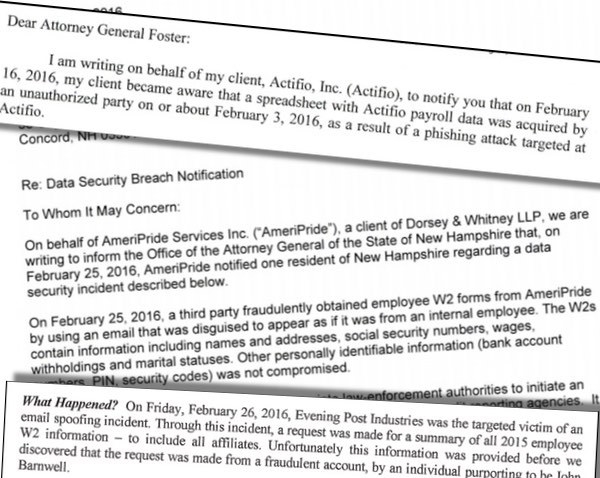
In June 2016, the FBI reported that companies had been stung to the tune of US $3 billion as a result of business email compromise attacks and that there had been a 1300% increase in identified losses since January 2015. As long as attackers continue to spirit away large sums of money from companies, the business email compromise attacks are going to intensify. All organizations need to educate their staff about the threats and put measures in place to reduce the chances of them becoming the next victim of a whaling attack. Learn more about the common techniques used in phishing attacks, and how to protect against them, in this guide by Tripwire's David Bisson. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

