
If malware on your Android phone doesn't steal any of your information, doesn't spy upon your activities, doesn't infect any of your files, and remains invisible... can we still consider it a bad thing? I think the answer is yes, but some security measures appear to turn a blind eye to a Trojan that security researchers at ESET have dubbed "Porn Clicker", which has managed to waltz its way past Google's screening system and bury itself within over 300 apps in the official Android app store.

According to the firm, many bogus versions of a wide range of apps (ranging from Toy Truck Rally to Subway Surfers 2 to GTA San Andreas and Tinder) have been distributed by fraudsters who wish to use your bandwidth to earn themselves affiliate income by clicking on adverts for pornographic websites. Of course, if the apps popped up a copy of the Chrome browser to click on the X-rated ads then chances are that you would notice something unusual was afoot. Criminals have learnt from experience that announcing their presence so obviously only hinders their money-making plans. So, in the case of "Porn Clicker", the apps spin up an invisible browser window - meaning that any ad-clicking is invisible to the naked eye. And then, a minute or so later, it clicks again. The money soon begins to earn cash for the criminals - which is a truth especially evident when you consider that some of the bogus apps have been downloaded thousands of times. In a further attempt to avoid drawing attention to itself in order to maximise its money-making potential, the Trojan knows about a wide range of Android anti-virus products and deliberately fails to engage in its antics if it determines that one is installed.
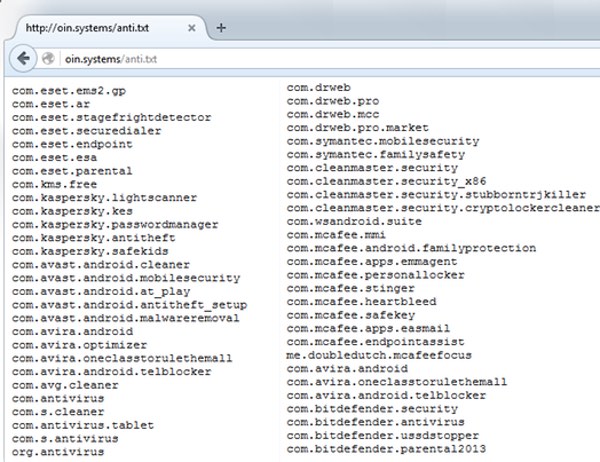
Potentially similar techniques may have been used by the Trojan to avoid detection by Google's vetting process, allowing hundreds of bogus apps to make their way into the official Android app store. Although some may not feel too fussed by its presence compared to information-stealing malware, clearly Porn Clicker isn't harmless. It uses up bandwidth which could cause a higher bill for some users, and your workplace may raise an eyebrow about your smartphone apparently using their Wi-Fi connection to access adult websites. And, by duping Android users into installing phoney versions of apps, sometimes claiming to be free versions of games that are usually sold online, they damage the brand of videogame makers and bring the Google Play Store and third-party app stores into disrepute.
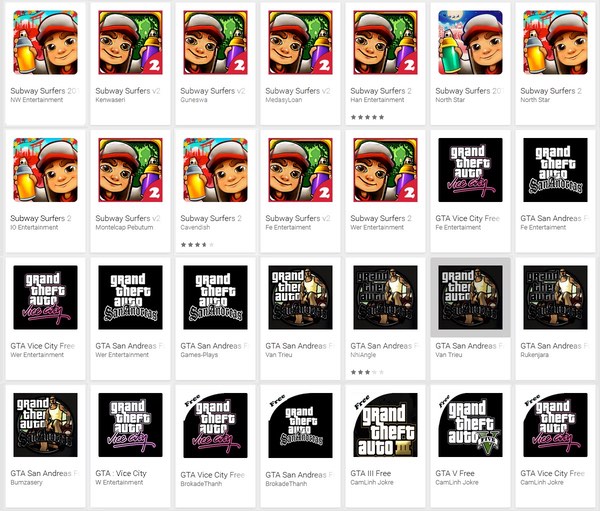
According to the researchers, one of the best ways to protect yourself - and ensure that you are installing a legitimate app rather than one which has 'cloned' its appearance - is to look at the customer reviews:
In cases like this, where the malware pretends to be a newly-released game with a fake app name and fake icon (My Talking Tom 3, GTA 2016, Temple Run 3 …), it’s very important to read user reviews. Many of these trojan porn clickers have received bad reviews and a lot of negative comments from users who had already been scammed. Even if users have no doubt before installation, we advise them to read the reviews and to reconsider downloading the application if there are many negative ratings. In most of these porn clicker cases there are more negative than positive reviews.
And, of course, it should go without saying that if you are serious about protecting your Android smartphone, you should probably be running a security solution on it. A long list of affected apps, their package names, and their MD5 checksums, can be found on ESET's website. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

