
American multinational conglomerate holding company AT&T has announced the launch of its public bug bounty program on HackerOne. Revealed on 6 August, the new program will award security researchers who submit reports on eligible vulnerabilities that affect AT&T's websites, mobile apps, devices and exposed APIs. In-scope flaws include weaknesses that affect the confidentiality or integrity of user data or privacy, enable individuals to obtain unauthorized access to important data/resources or enable the execution of unauthorized code, among other properties. By contrast, the vulnerability disclosure program does not support bugs that breed attacks against the company's infrastructure, social attacks or distributed denial-of-service (DDoS) attacks. AT&T's program will award as much as $2,000 for a report on an eligible critical-level vulnerability. That reward amount drops to $750 and $300 for researchers who properly disclose a flaw of high and medium severity, respectively. At the very bottom of its award hierarchy, the company will reward $150 to researchers who uncover low-level vulnerabilities.
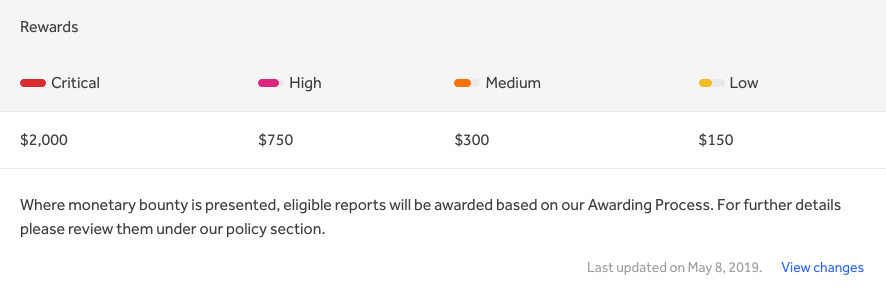
AT&T's bug bounty reward structure. Those wishing to participate in the new program will need to register and/or log into their account with HackerOne. Once they've discovered a viable vulnerability, they should make sure that their report includes the details and tools needed to reproduce the flaw. They can then expect to hear back from the company within one business day after submitting their report. That being said, not all eligible reports will produce an award. AT&T won't issue a bounty if someone submits a duplicate submission of a vulnerability already covered. It will also not reward those who fail to abide by the principles of responsible disclosure. Not only that, but the company said it might even take punitive action in those cases.
You must submit your report as soon as you have discovered a potential vulnerability. By submitting the vulnerability, you affirm that you have not disclosed and agree that you will not disclose the vulnerability or your submission to anyone other than AT&T following the process set forth in the Program. Absent AT&T's prior written consent, any disclosure would violate the Program. It is understood and agreed that money damages would not be a sufficient remedy for any breach of this paragraph by you or your representative(s) and that AT&T shall be entitled to specific performance as a remedy for any such breach, including injunctive relief. Such remedy shall not be deemed to be the exclusive remedy for any such breach but shall be in addition to all other remedies available at law or equity to AT&T.
Additional information on the bug bounty program can be found here. You can also click here the details of some of the most essential bug bounty programs in 2019. News of this vulnerability disclosure framework arrived on the same day that the U.S. District Court for the Western District of Washington at Seattle unsealed an indictment against a 34-year-old man from Pakistan. Law enforcement extradited that individual from Hong Kong to the United States for charges of having bribed AT&T employees to unlock over two million phones. He's also facing charges of having hacked the American multinational conglomerate holding company's computers.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

