
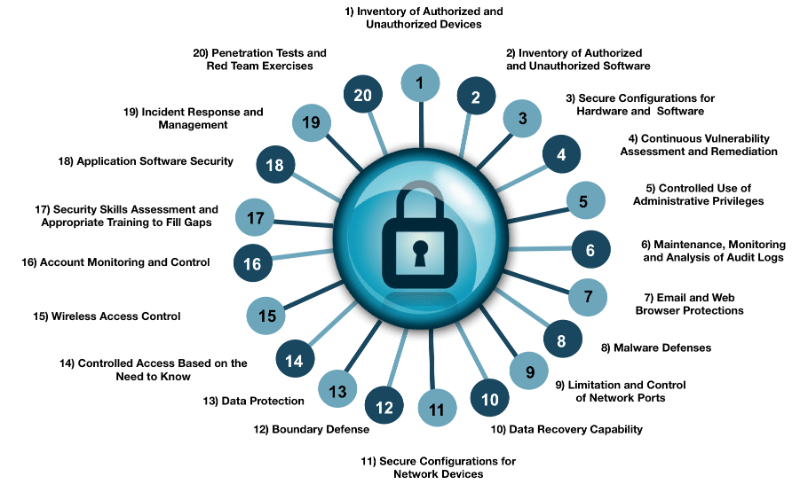
A Configuration Management Database (CMDB) is a repository that is an authoritative source of information of what assets are on the corporate network. At least, that’s what it’s supposed to be. However, in many of my recent discussions, the more common definition given for CMDB is “a struggle.” Does that sound familiar? If so, keep reading. If not, please share your secrets in the comments below! Maintaining an accurate list of systems on the network along with what is installed on those systems has proven to be incredibly difficult to maintain. Change is inevitable, and organizations need to stay nimble to be successful. Many organizations struggle to maintain an authoritative list, be it on a spreadsheet or using a specific management tool. Then again, we’ve managed to get by without it. Why should we invest time and effort in fixing this problem? Depending on your role, the answer could be a little different. At the end of the day, whether you are in Compliance, IT Security, or IT operations, your department is a cost centre for your organization. If you cannot justify spending more money, the business is not going to prioritize fixing this problem over other initiatives. First, let’s look at why this is a problem from a security perspective. The average information security professional loves to hack into things. That’s why we got into security in the first place, right? That is all fine and well but what good is a penetration test if you are unaware of what assets are there to test against? We know what should be there, but what is actually there? One of the first things an attacker is going to do when trying to break into your organization is search for a device sitting somewhere on the network that you forgot about or did not know about. There is a very good chance that the forgotten system is unprotected and unpatched, leaving it vulnerable to attack. The users of that system know it’s there, but does the security team? Unfortunately, many organizations still face the problem of system owners hiding their systems from security, so they are not pressured to keep them up-to-date and hardened. Knowing what is on your network is the key first step in deploying security controls. This is why having an up-to-date, authoritative inventory of the hardware and software on your network is number one and two on the CIS Critical Security Controls. Deploying security tools on your endpoints is a key part of defence-in-depth. However, if there are endpoints without those security tools, there are gaping holes for attackers to use as pivot points into more sensitive areas of your network. Tony Sager said it best:
“Identifying what’s on your network is a basic information security best practice that, unfortunately, remains difficult for many organizations. If you don’t know what you are protecting, it’s very difficult to apply the most effective controls. And it’s even more difficult to recover effectively if you are exploited.”
So, how do we apply this in real life? I’m glad you asked! Traditionally, organizations have relied on the change management process to alert the information security team of the provisioning of new networks and systems. Clearly, there needs to be some sort of process improvement here. A possible technical solution that I’ve seen work very well is leveraging your organization’s Vulnerability Management (VM) Program. As part of the VM program, the VM solution needs to scan the network. As part of that scan, a lot of key information is gained that can be leveraged by the CMDB. Information such as IP addresses, hostnames, operating systems and installed software is easily profiled during the vulnerability scan. A simple integration between the VM solution and the CMDB can automate the process of keeping the CMDB up-to-date. Of course, with great automation comes great responsibility. A properly deployed and tested program must first be place before this process can be automated. This brings us to the most important part. How do we justify making asset inventory a high priority? It’s not the sleek new technology that everyone wants to play with. It seems boring, but without this building block, even the best of marketing campaigns won’t be able to bail you out. First, each organization should have a framework for implementing security controls. The CIS Critical Security Controls are a great industry best practice to assess your security program against. If you have not yet done so, be sure to leverage the great work that has been done by the industry leaders at the Centre for Internet Security.
The Controls have been recommended by Kamala D. Harris (Attorney General, CA), defining them as:
“...a minimum level of information security that all organizations that collect or maintain personal information should meet. The failure to implement all the Controls that apply to an organization’s environment constitutes a lack of reasonable security.”
Second, let’s look at one of the key costs of any IT department: software licensing. The CMDB should be able to tell the organization how many of what is being used so that the appropriate amount is spent on software licenses. I’ve seen a number of organizations successfully leverage their vulnerability scan data to identify the number of instances of installed software. This allowed them to match their findings against the number of licenses they were subscribed to. In each case, they were able to reduce the number of subscriptions and greatly reduce their software licensing costs. Third, over the last couple of years, there have been a record number of 0-day vulnerabilities identified with fancy logos that attract a lot of attention from executives. Security administrators often were caught flat on their heels and scrambled to get updated signatures and plug-ins from their vulnerability scanning vendors. Signature updates require the appropriate QA time frames, for which executives do not always have the patience. Having an up-to-date CMDB allows the security administrator to simply query the database for all of the known affected versions of the vulnerable software. This provides an instant list of the potential exposure of the organization. (We will leave alone the fact that Verizon's 2015 Data Breach Report says, "99.9% of the exploited vulnerabilities were compromised more than a year after the CVE was published.") To summarize, it’s about time organizations started paying more attention to the quality of their asset inventory. Having an up-to-date repository of the assets on the network along with the installed software on those systems is a key foundational control for any information security program. It is so critical and it takes up not one, but the two top spots on the CIS Critical Security Controls. This year, make it a priority to provide your organization with an authoritative asset repository.
Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

