
A phishing campaign used what appeared to be back-to-work notifications in order to compromise recipients' corporate email accounts.
Near the end of November, Abnormal Security detected one of the campaign's attack emails. That message masqueraded as an internal notification from the recipient's company. It did so by using spoofing techniques to disguise the sender address.
The email didn't originate from inside the company, however. As Abnormal Security explained in its research:
... [T]he sender’s actual address is ‘[email protected]’, an otherwise unknown party. Further, the IP originates from a blacklisted VPN service that is not consistent with the corporate IP. This indicates the sender is impersonating the automated internal system.
Using these techniques, the phishing email attempted to trick the recipient into thinking they had received a voicemail and that a callback was requested.
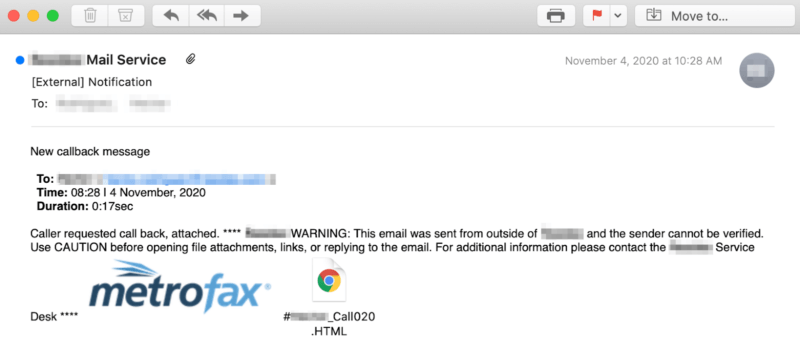
That email instructed the recipient to open an HTML attachment containing the recipient's name in its title.
When opened, that document appeared to lay out new instructions for the targeted company's remote work policy. It also included a link that urged users to submit their acknowledgment of the updated terms. In reality, it sent them to a fake login page designed to steal their email credentials.
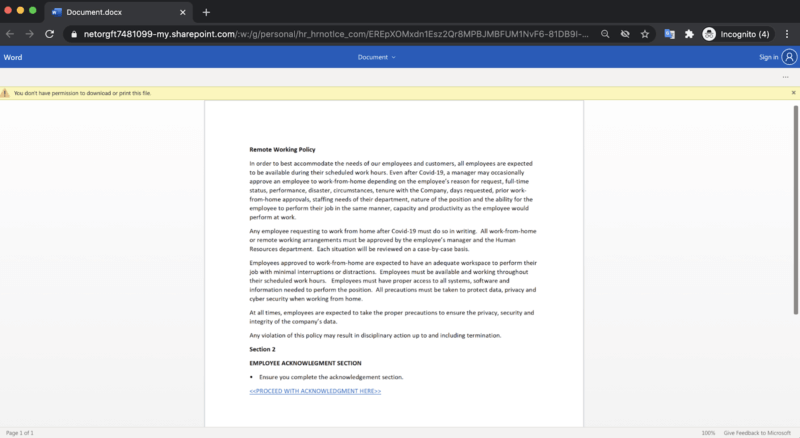
If the user attempted to authenticate themselves, the fake login portal sent their credentials over to the attackers.
Those malicious actors could have then used those details in an attempt to access the targeted company's sensitive data.
At the time of Abnormal Security's discovery, this phishing campaign had bypassed G Suite's email security tools and landed in as many as 100,000 employees inboxes.
This campaign highlights the need for organizations to protect their employees' corporate email accounts against phishers. One of the ways they can do this is by educating their users about some of the most common types of phishing attacks that are in circulation today. This resource is a good place to start.

