If you're responsible for your company network there's a strong possibility that you aren't keen on users installing BitTorrent clients. Not only might they be gobbling up vast amounts of bandwidth, but they could also be downloading pirated content or malware that could create headaches for your organisation. But in the case of the popular Russian BitTorrent client MediaGet there's another reason why you may wish to consider torrenting apps as unwanted on your network. Microsoft has detailed how it intercepted a massive malware distribution campaign on March 6th which attempted to infect over 400,000 Windows PCs with cryptomining software in a single 12 hour period.
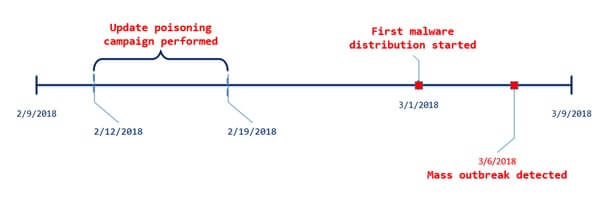
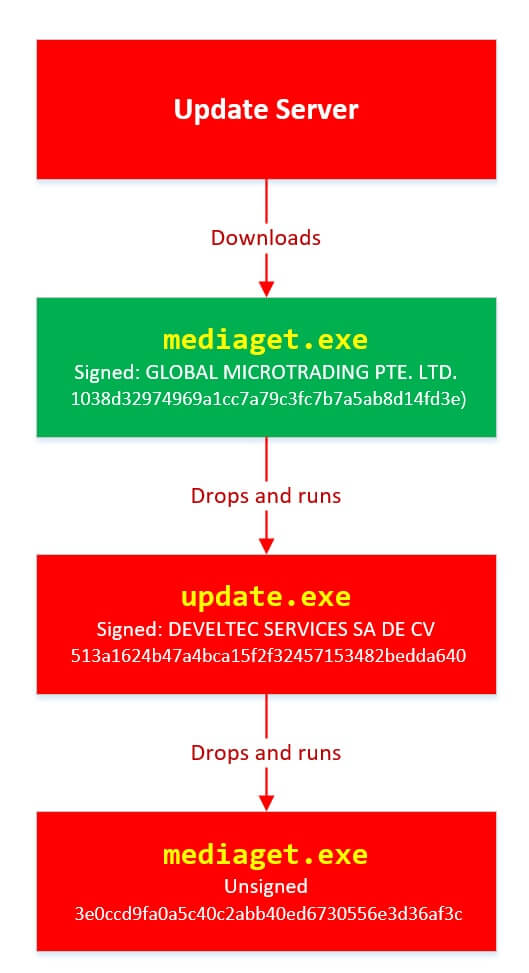
What we now know is how the malware was spread. The attack saw hackers ignore such common-or-garden methods as spamming out malicious email attachments, and instead plant a malicious version of MediaGet on an update server. The poisoned update would itself install a malware downloader called Dofoil (also known as Smokeloader) onto computers, which could then install further malicious code from the internet. In the case of the March 6th attack, the attack culminated in an attempt to run code that could mine the Electroneum cryptocurrency on 400,000 Windows computers. What is clear looking at the timeline is that this was not an opportunist attack, but a well-planned and organised attempt to hijack a large number of computers - and potentially earn a great deal of money - using advanced techniques.
73% of the global infection attempts occurred in Russia (perhaps not surprising considering MediaGet's popularity there), with Turkey and Ukraine accounting for 18% and 4% respectively. Perhaps we're lucky that there has been a drop in ransomware infections as Trojans which mine cryptocurrencies and browser-based cryptojacking attacks have been on the rise. After all, things could have been a lot worse. As Jessica Payne of the Windows Defender Security Research team pointed out via Twitter it would be wrong to categorise the MediaGet attack as merely an attempt to spread cryptomining code, but that the same method could have been used to deliver more pernicious payloads.
"What we did wasn't just to disrupt a 'relatively harmless' mining campaign, but to detect and interrupt a distribution vector that could just as easily have delivered ransomware to those targets."
The advice is clear - ensure that you have layered defences in place, including up-to-date anti-virus software, and minimise the risk that damage will be done to your personal and business systems by following best practices. More than that, however, maybe if your company is not already enforcing a policy about who is and who isn't permitted to run peer-to-peer torrenting software, maybe now would be a sensible time to add that to your list. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

