It's the kind of bad news that every organisation hopes it will never have to find itself sharing with its customers - hackers have breached computer systems, and accessed a database containing sensitive personal information. On this occasion, the corporate victim warning 1.1 million customers that an attack has occurred is CareFirst, a major health insurer. The company says that it has recently determined that in June 2014 hackers were able to gain unauthorised access to a database, used to collect details entered by members and other individuals on CareFirst's websites and online services. To its credit, CareFirst hasn't tried to sweep the unfortunate news under the carpet. A warning is displayed prominently on its website, and an apologetic video message from CareFirst's CEO can be watched on a website, carefirstanswers.com, set up specifically to share news and advice with affected customers.

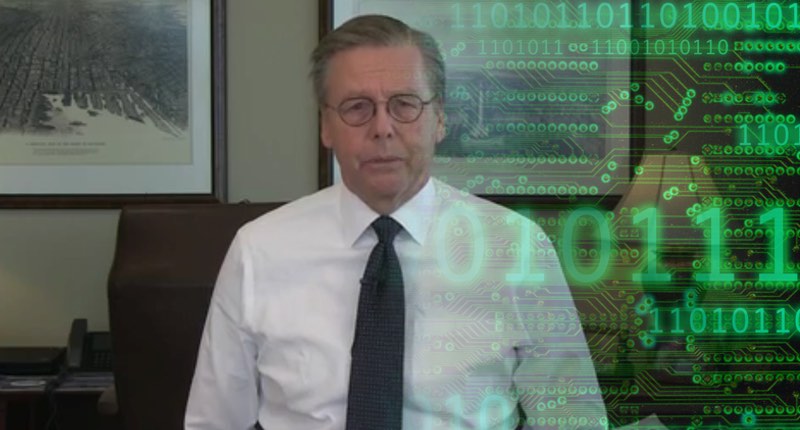
In the video, CareFirst CEO Chet Burrell says that the attack was discovered as part of an ongoing security initiative, after a third-party security company was brought in to explore potential issues following a spate of attacks against other health insurers in recent months. Burrell was keen to stress that no passwords, social security numbers, financial information or medical claims were exposed. However, user ids created by customers as well as members' names, birth dates, email addresses and subscriber identification numbers could have been accessed by the attackers.

The fact that breach occurred in July last year, and has only been uncovered now highlights a key problem with detecting online crime. When the contents of a hacked database are raided it's not like the Mona Lisa being stolen from the Louvre, there's no gap on the wall where the painting used to be. The "loss" of data is virtual, meaning that more sophisticated methods have to be used to determine that it might have been accessed illegally and data siphoned out. CareFirst says that no evidence of any further breach has been found by the security experts it called in. It's too early, and there's no information available, to speculate as to how the hack occurred or whether CareFirst might have been able to do more to prevent it. For now, all that can be said is that it appears to have responded appropriately and transparently, warning its customers about the unfortunate situation and offering free credit monitoring and identity theft protection for two years. Furthermore, the fact that it chose to audit its network for security breaches following the hacks against Anthem and other healthcare firms sends an important message to all businesses - don't assume it cannot happen to you. When you read about hacks against other companies, don't be tempted to enjoy another firm's misfortune, but instead ask yourself the difficult question of whether it could happen to you and, perhaps even more importantly, has it already happened to you? Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

